Search Results for: malware
Installing SSH on Kali Linux and Ubuntu (22.04)
SSH, or Secure Shell, is a cryptographic network protocol that is used to provide secure communication. It provides a secure channel over an insecure network [more…]
Installing NMAP on Kali Linux and Ubuntu (22.04)
Introduction to NMAP What is NMAP, and why is it essential for network administrators and cybersecurity professionals? NMAP, short for Network Mapper, is an open-source [more…]
The Web of IPStorm: The Case of Sergei Makinin
Ever wondered how someone can take control of thousands of electronic devices around the globe without the owners even realizing it? Let’s dive into the [more…]
The Undercover Network: Socks5Systemz Botnet
Have you heard about this new botnet that’s been lurking in the shadows? Let me paint you a picture. Imagine a digital hydra–you cut off [more…]
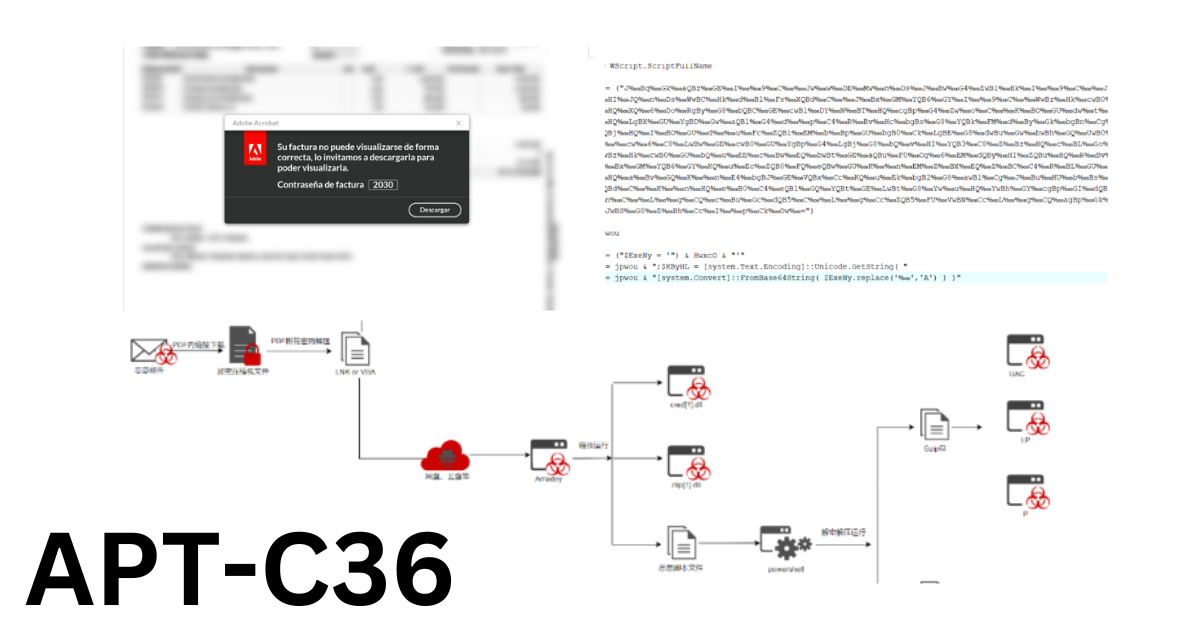
Relentless Cyber Espionage Campaign APT-C-36 Plagues Colombia
Have you caught wind of APT-C-36, the digital shadow lurking across South America? APT-C-36, dubbed Blind Eagle, is not your average cyber adversary. This Advanced [more…]
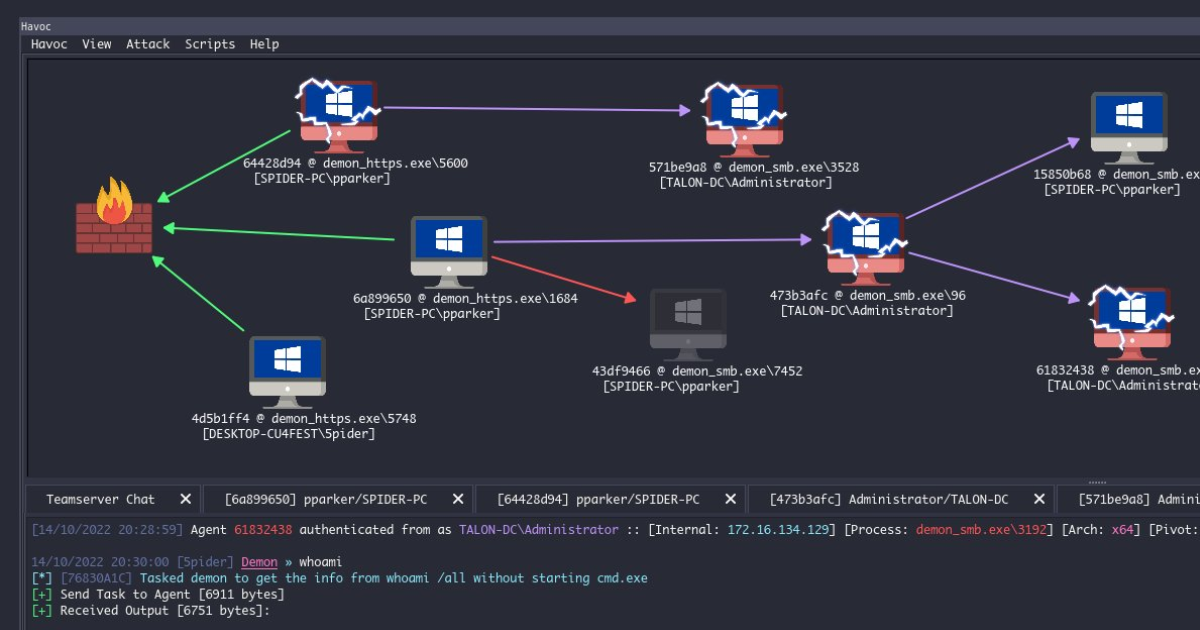
So, have you heard about Havoc, the new tool in the cyber arsenal?
Let me give you the lowdown on what’s brewing in the digital underground with this fresh piece of software called Havoc. Now, you might be [more…]
Cyber Security vs. Information Security: Navigating the Digital Minefield
Alright, What’s the Deal with Information Security? Ever had that nightmare where you’re shouting secrets in a crowded place? Information Security (InfoSec) is the dreamcatcher [more…]
Top Shelf Tools: The Best Eight of Kali Linux
Got a Thirst for Breaking Things Securely? Let’s Talk Pen Testing and Kali Linux What’s this Pen Testing Buzz I Keep Hearing? You’ve stumbled across [more…]
Best CyberSecurity Software Tools For 2024
In 2024, you want to be equipped with the best cybersecurity tools. We have created this list of cybersecurity tools that contain a massive collection [more…]
The Role of Automated Analysis and Triage in Cybersecurity
Big volumes of security threats make it challenging to pinpoint which incidents need immediate attention. Automated analysis and triage systems in the realm of threat [more…]