Tag: guide
Fast PowerShell Commands For Cybersecurity Experts
Use these awesome powershell commands and scripts to elevate your cybersecurity toolkit. There are a lot of things you can do with Powershell, and we [more…]
How to Securely Download Files in Ubuntu 22.04 Using SSH?
The Necessity of Secure File Transfers Ever found yourself puzzled about how to safely transfer files from a remote server to your local machine using [more…]
How to Install Flask on Kali Linux and Ubuntu 22.04
Running the Python Flask API framework If you want a fast light weight API, then go for Flask. Flask, is a popular micro web framework [more…]
Installing SSH on Kali Linux and Ubuntu (22.04)
SSH, or Secure Shell, is a cryptographic network protocol that is used to provide secure communication. It provides a secure channel over an insecure network [more…]
Install Metasploit on Kali Linux (Also works for Ubuntu 22.04)
Ever wondered how cybersecurity professionals and ethical hackers stay on top of their game? They use powerful tools, and one such tool is Metasploit. So, [more…]
What You Need To Know About The Pyramid of Pain
Demystifying the Pyramid of Pain The Pyramid of Pain is not just a flashy term; it’s a conceptual framework that security analysts and threat hunters [more…]
Penetration Testing for WordPress Websites
WordPress, a content management system (CMS) that powers 810 million websites, is a frequent target for cybercriminals. Whether your WordPress site serves as an e-commerce [more…]
The Growing Risk of Initial Access Brokers and the Role of MDR and MSSP in Mitigating Threats
Introduction: Who Are the Invisible Hands Behind Ransomware Attacks? Ever wondered who sets the stage for those notorious ransomware attacks that cripple businesses and drain [more…]
Responding to “Your Rates Are Too High”: A Guide for Cybersecurity Firms
Introduction: Getting things right Are you grappling with how to respond when a long-time client says, “Your rates are too high”? This is a common [more…]
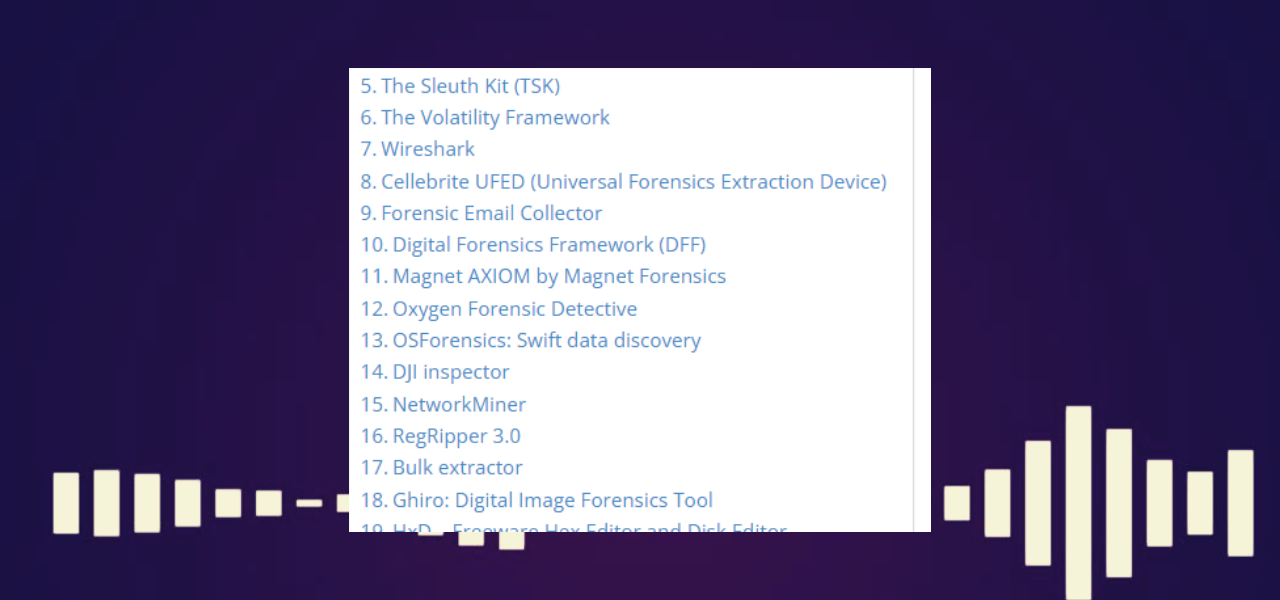
Top Digital Forensics Tools (2023)
Wondering which digital forensics tools are making waves in the cybersecurity landscape? You’ve come to the right place. In this guide, we walk you through [more…]