Got a Thirst for Breaking Things Securely? Let’s Talk Pen Testing and Kali Linux
What’s this Pen Testing Buzz I Keep Hearing?
You’ve stumbled across the term ‘penetration testing’, right? But what the heck is it? Picture this: you’re a digital locksmith, testing locks, but instead of locks, it’s computer systems, and instead of keys, you’ve got your hacker toolbox.
Pen testing is like a simulated cyber break-in, where the good guys (that’s us, pal) check for open ‘windows’ and ‘doors’ in networks and applications. The goal? To beef up security before the bad guys get a chance to sneak in.

And Kali Linux? What’s the Deal There?
Ah, Kali Linux, the Swiss Army knife for cybersecurity buffs. It’s not your everyday operating system; it’s more like a collection of lock picks for the digital locksmiths I just mentioned.
Kali is stacked with over 600 tools for testing and securing networks. It’s the go-to for ethical hackers, and it’s all about testing those cyber defenses to the max.
Also read
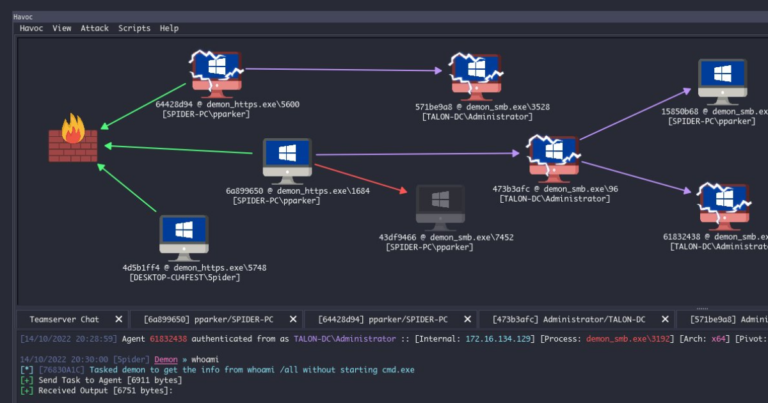
- So, have you heard about Havoc, the new tool in the cyber arsenal?
- Top Shelf Tools: The Best Eight of Kali Linux
- Best CyberSecurity Software Tools For 2024
- Top 10 web development tools
- CISA Unveils Logging Made Easy: The One-Stop Solution for Windows-Based Systems
Top Shelf Tools: The Best Eight of Kali Linux
Now, let’s get to the meat of the matter. You’re thirsty for knowledge on the crème de la crème of Kali Linux tools for this year. Buckle up, ’cause here we go.
1. Fluxion – The Wi-Fi Whisperer
Wi-Fi’s everywhere, and where there’s Wi-Fi, there’s a way in for hackers. Fluxion’s the tool that tests how tight your wireless security really is. It’s clever, using a mix-and-match of techniques to coax out those Wi-Fi passwords without brute-forcing its way through.
2. John the Ripper – The Name’s Ripper, Password Ripper
Sounds like a character from a thriller, doesn’t it? John the Ripper‘s the go-to guy for cracking passwords. It’s like a stress test for your password’s strength, across multiple platforms. Whether you’re rocking Linux or chilling with Windows, John’s got you covered.
3. Lynis – The Digital Detective
Think of Lynis as your cybersecurity consultant, running the rule over your system, leaving no stone unturned. It’s all about compliance, auditing, and finding those chinks in your armor. It’s thorough, trust me.
4. Metasploit Framework – The Remote Control Rogue
Remote’s the buzzword nowadays, and Metasploit’s the answer to testing how hack-proof remote systems are. It’s a playground for ethical hackers, giving them the tools to emulate the baddies, find weaknesses, and help secure them. It’s potent, and it’s free.
5. Nikto – The Web Watchman
Web servers are juicy targets, and Nikto’s the lookout, scanning for vulnerabilities that could let attackers in. It’s all about getting the lay of the land, finding out what’s what on a web server, and flagging up the no-nos.
6. Nmap – The Network Navigator
The old guard, Nmap, has been around the block, mapping out networks, and finding out who’s home on the internet. It’s about understanding the battlefield before you even step foot on it. Ports, services, what’s up and what’s down – Nmap tells you all.
7. Skipfish – The Web Recon Ranger
If you’re hitting web apps, Skipfish is your scout. It maps out the terrain, looking for traps and tripwires in web applications. It’s fast, it’s thorough, and it’s got a knack for finding the spots where attackers might slip through.
8. Social Engineering Toolkit – The Digital Con Artist
Last but not least, SET is for those who like to play mind games. It’s all about trickery, getting into heads and networks by fooling people. Phishing, spoofing, you name it – SET’s got a trick for it.
Becoming a Cybersecurity Maestro

So you wanna be a cybersecurity expert? Dive into these tools, get your hands dirty, and you’ll be on your way. Remember, with great power comes great responsibility. Use these tools wisely, learn the ropes, and maybe I’ll see you in the field. Cheers to that!



























+ There are no comments
Add yours