Search Results for: credentials
Why Hackers Target Fortinet VPN
The Fortinet VPN is known for its robust and secure environment. It’s a favorite for businesses across the globe. Why? Simply because it provides a [more…]
Understanding the CVE-2023-27992 Vulnerability in Zyxel NAS Devices
If you are a cybersecurity enthusiast, then you must have heard about the critical vulnerability in Zyxel NAS devices. This flaw could potentially allow unauthorized [more…]
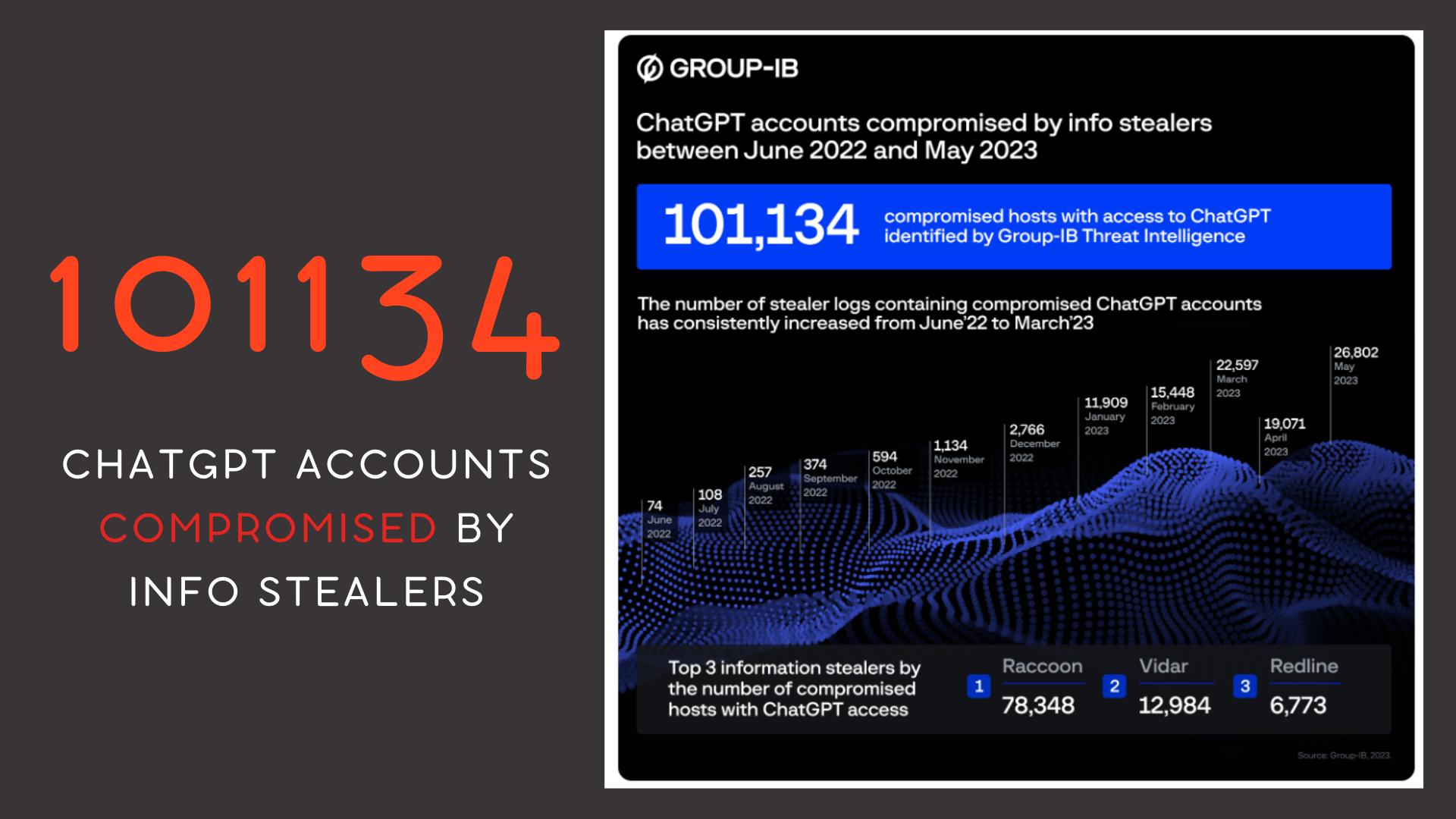
Over 100K ChatGPT Accounts Compromised; APAC Region Heavily Targeted
Cybersecurity firm Group-IB has unearthed evidence of 101,134 infected devices holding stored ChatGPT credentials, with the Asia-Pacific region emerging as a particular hotspot. Data extracted [more…]
Initial Access Brokers: The Underbelly of Cybercrime and Ways to Fortify Your Defense
The “initial access broker“. These cyber operators excel in securing the first critical breach into a system or network. They then commoditize this access, selling [more…]
The How and Why of Remote Desktop Protocol (RDP) Attacks
If you work in IT or cybersecurity, you’re likely familiar with Remote Desktop Protocol (RDP). This useful tool has made remote work and system management [more…]
Honda E-commerce Platform’s API Flaws Exposed
Honda’s e-commerce platform, catering to the power equipment, marine, lawn & garden sectors, recently found itself under scrutiny due to API vulnerabilities. These flaws allowed [more…]
What is BlackCat (Alphv) Ransomware?
BlackCat, otherwise known as ALPHV, has carved its niche in the cyber-threat landscape. Its unconventional Rust programming language and ability to target a wide array [more…]
Critical Vulnerability in Fortigate VPN Servers CVE-2023-27997
Fortinet’s Fortigate VPN servers are currently under the spotlight for a critical vulnerability that potentially enables an unauthenticated attacker to remotely seize control of the [more…]
Responding to Azure Account Breaches
Cybersecurity incidents, particularly breaches of cloud services like Microsoft Azure, can cause significant disruption and financial impact for businesses. This article provides a step-by-step guide [more…]
Understanding LockBit 3.0 Ransomware Threat
LockBit 3.0, aka “LockBit Black,” has been causing waves in the cyber world as a new and sophisticated iteration of the notorious LockBit ransomware. Sharing [more…]