Search Results for: credentials
Microsoft Warns of Phishing Attacks by Storm-0978 Group Targeting Defense and Government Entities
Microsoft has raised an alert about an ongoing phishing campaign conducted by the cybercriminal group known as Storm-0978. The threat actor, also referred to as [more…]
Cyber Awareness: Understanding Cyber Threats
In today’s world, it is vital to be aware of the lurking dangers of cyber threats. In this guide, we will explore the significance of [more…]
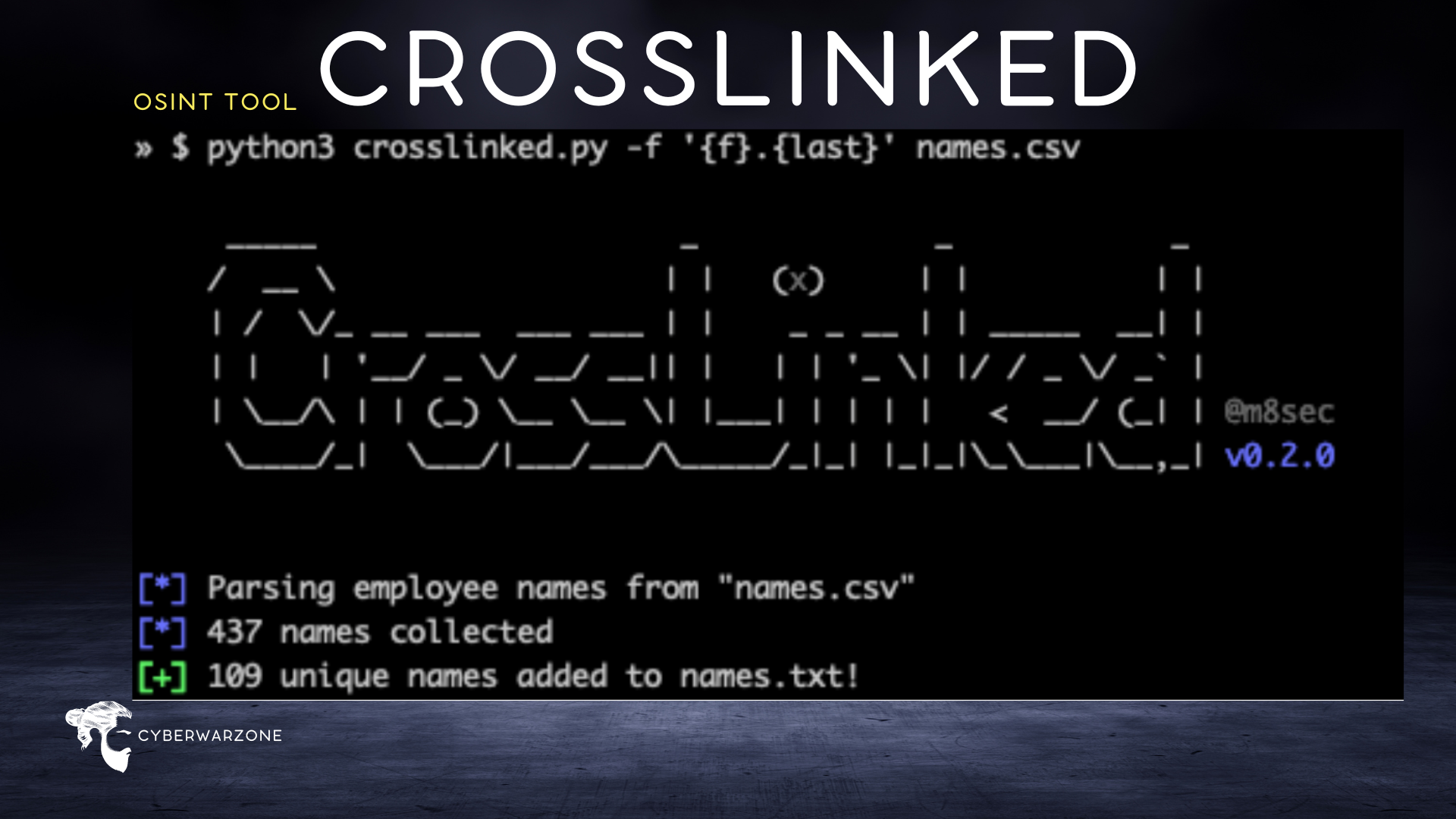
CrossLinked: An Effective OSINT Tool for Pentesters
Open Source Intelligence (OSINT) plays a crucial role in gathering valuable information about potential targets. For pentesters, having access to accurate and relevant data is [more…]
What is Ransomware-As-A-Service (RaaS)
Today, we’re diving into the world of Ransomware-as-a-Service (RaaS). It’s as ominous as it sounds, a cybercrime model where tech miscreants provide ransomware to their [more…]
Top Cybersecurity Tools Of 2023
Let’s explore the top cybersecurity tools of 2023 that every threat hunter and cybersecurity professional should have in their arsenal. A Quick view Kali Linux: [more…]
Major Maritime Ransomware Attacks
If you’re seeking an in-depth exploration of ransomware attacks’ history within the maritime industry, you’re in the right spot. Here, we recount the most consequential [more…]
Understanding the Azorult malware
Azorult is one of those sneaky villains in the world of cybersecurity, a potent piece of malware, that leaves a path of digital destruction in [more…]
Inside Mimikatz: The Go-To Tool for Cyber Attackers Explained
Since its debut in 2011, Mimikatz, designed by French security researcher Benjamin Delpy, has caused sleepless nights for many in the cybersecurity field. Originally created [more…]
Security Event IDs for Threat Hunters
Join us as we unravel the secrets of threat hunting, diving deep into various event IDs that expose hidden risks and potential cyber threats. From [more…]
FileZilla Forensics with Python
Incident responders and cybersecurity enthusiasts, this one’s for you. If you’ve ever faced challenges in tracing data exfiltration via FileZilla, this tool will ease your [more…]