Latest
More To Read
You Are Right, ChatGPT is Down
At the moment of writing, numerous users on X are sharing their discomfort of not being able to access the popular LLM service ChatGPT. Joseph [more…]
Learn How To Find Recently Opened Windows 10 Folders
Windows 10 meticulously records your every move, but to the untrained eye, these records are mere whispers in a sea of digital noise. Now, let’s [more…]
The Undeniable Cybersecurity Communication Problem
Have you ever pondered why some cybersecurity leaders thrive under pressure, seamlessly steering their teams through the digital tempests, while others falter? It’s not just [more…]
Cyber Threat Dissection: Anatomy of a Malware Attack
The Essence of Malware A silent war persists beneath the surface of our daily internet sojourns. At its core, this war is fueled by a [more…]
What’s the Buzz About Threat Intelligence Management?
Decoding Threat Intelligence Management Ever caught wind of what threat intelligence management really is? Let’s unpack that. The Essence of Intelligence Management in Cybersecurity Imagine [more…]
The Undercover Network: Socks5Systemz Botnet
Have you heard about this new botnet that’s been lurking in the shadows? Let me paint you a picture. Imagine a digital hydra–you cut off [more…]
30% Surge in Fraudulent Webshops
The Netherlands – So, have you heard about the latest cyber sweep in the Netherlands? Over a thousand fraudulent webshops were yanked off the net [more…]
Palo Alto’s $625 million Bold Move in the Israeli Tech Arena
Is Palo Alto Networks becoming the kingpin of cyber chess? Let me paint you a picture: It’s like Palo Alto Networks is sitting at a [more…]
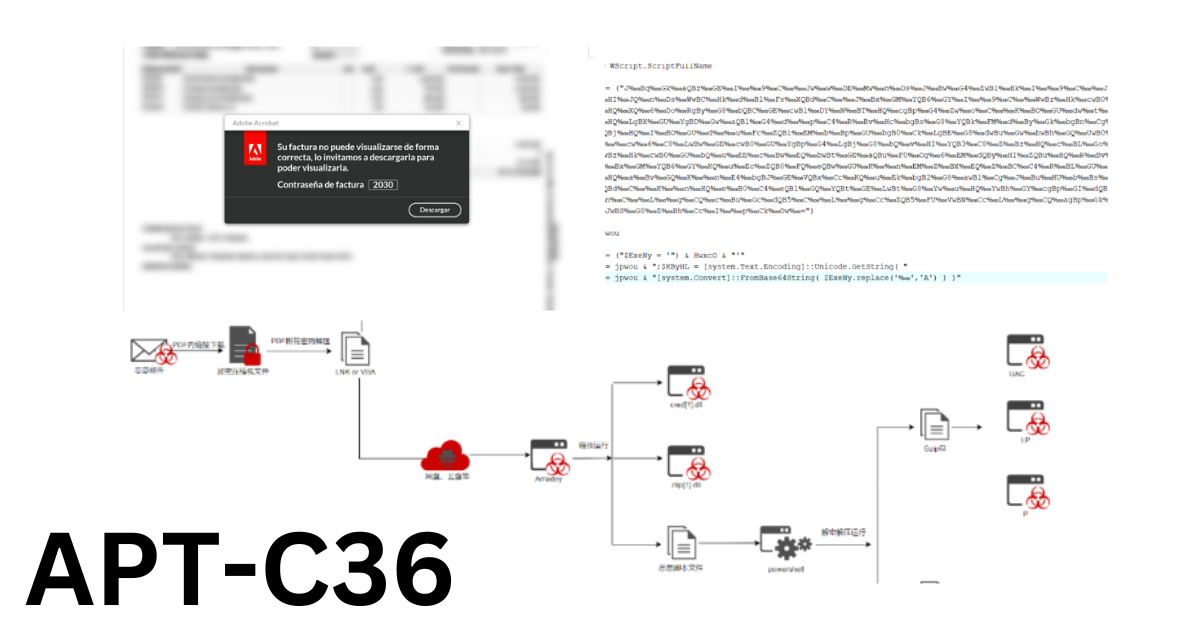
Relentless Cyber Espionage Campaign APT-C-36 Plagues Colombia
Have you caught wind of APT-C-36, the digital shadow lurking across South America? APT-C-36, dubbed Blind Eagle, is not your average cyber adversary. This Advanced [more…]
How to Restart the MySQL Service on Ubuntu (2024)
Imagine you’re at the wheel of a Linux-powered beast. You’ve been cruising along, and suddenly, you hit a snag – your MySQL database is giving [more…]