Search Results for: vulnerability
Cl0p MOVEit Cyberattack hits U.S. Federal Agencies
In a disquieting development, a Russian-speaking hacking group infiltrated the email systems of approximately 632,000 U.S. federal employees. The targeted departments included the Defense and [more…]
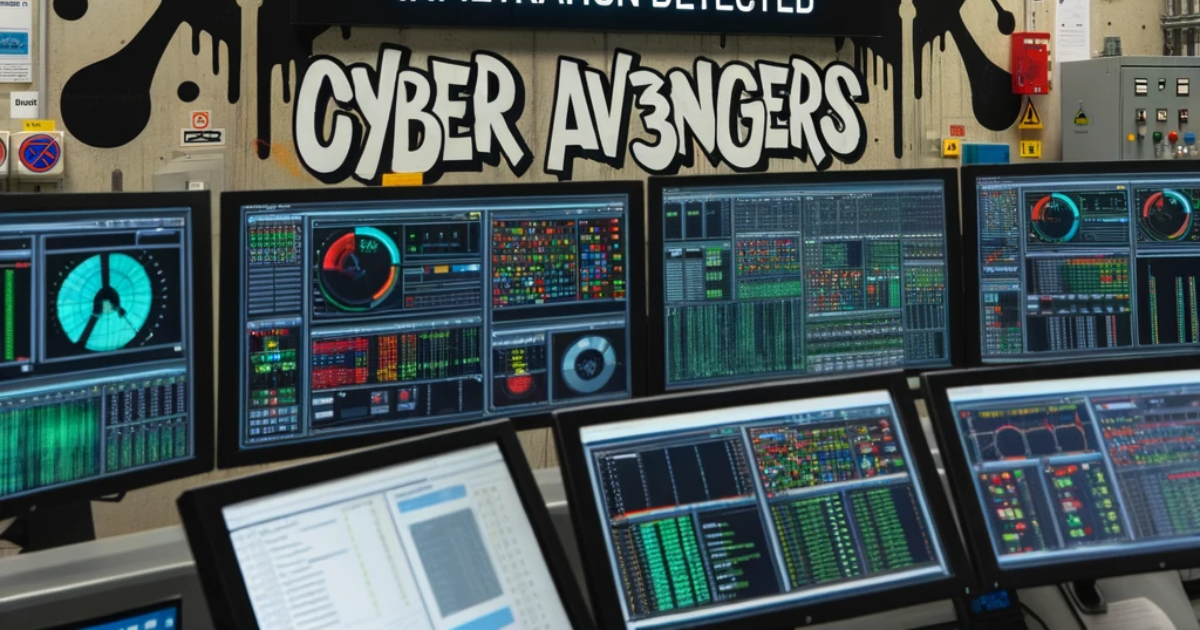
Cyber Av3ngers Claims Infiltration of Israeli Water Treatment Stations Amid Ongoing Conflict
In a significant development amidst the ongoing conflict between Israel and Hamas, the hacking group known as Cyber Av3ngers has claimed responsibility for infiltrating 10 [more…]
7 Essential Applications of Threat Intelligence in Cybersecurity
We all know that cybersecurity threats are becoming increasingly sophisticated and targeted. This necessitates a proactive approach to security, rather than a purely reactive one. [more…]
Penetration Testing for WordPress Websites
WordPress, a content management system (CMS) that powers 810 million websites, is a frequent target for cybercriminals. Whether your WordPress site serves as an e-commerce [more…]
Unprecedented Surge in Cyberattacks on Industrial Operations Suggests Bleak Future
The pre-pandemic era witnessed negligible cyber-sabotage attacks on manufacturing plants. However, the landscape has shifted alarmingly. A recent study reveals that over 150 industrial operations [more…]
Cracking the Code: The Essential Cybersecurity Terminology for Aspiring SOC Specialists in 2024
Introduction Embarking on a career in a Security Operations Center (SOC) demands more than just technical acumen; it requires fluency in the unique language of [more…]
Estonia Turns to China Amidst Baltic Sea Telecom Cable Crisis: A Complex Web of Geopolitics, Security, and Technology
Introduction: The Sudden Crisis in the Baltic Sea In a move that underscores the intricate geopolitics of modern-day cyber-infrastructure, Estonia has reached out to China [more…]
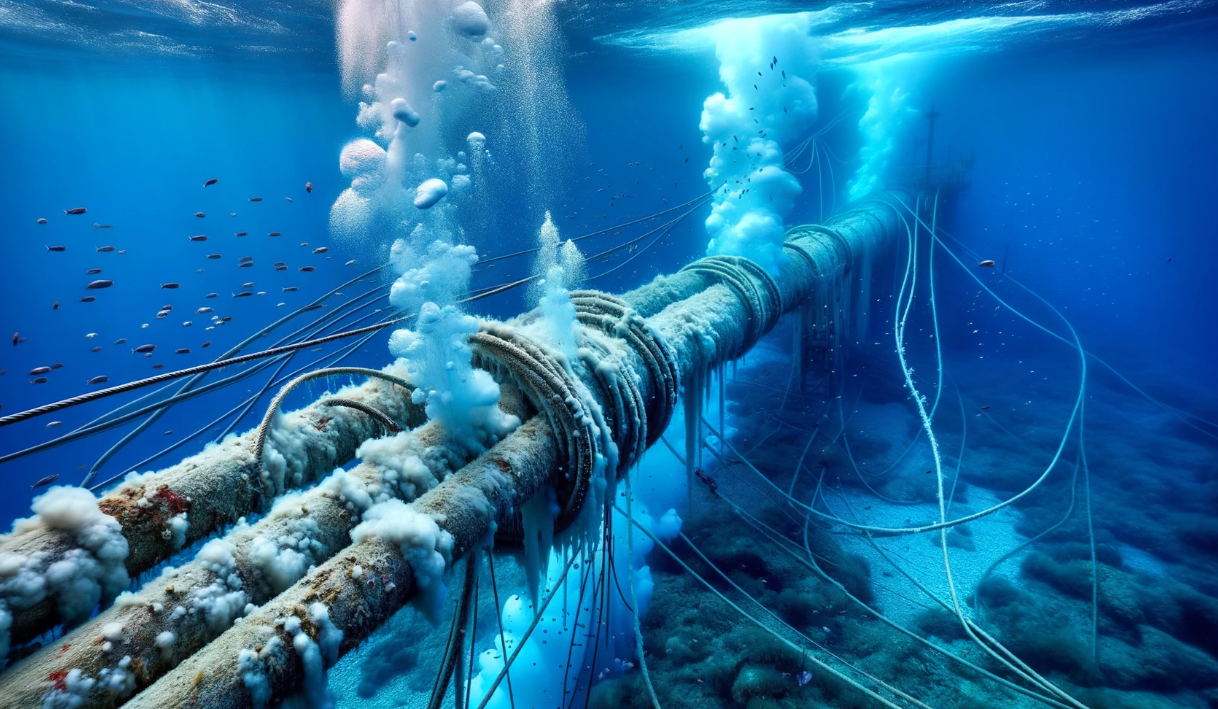
Undersea Infrastructure Under Attack: Unpacking the Finland-Estonia Pipeline Incident
Introduction: A New Kind of Warfare? Damage to an undersea gas pipeline and telecommunications cable between Finland and Estonia has set off alarms across the [more…]
The Strategic Implications of USS Gerald R. Ford Carrier Strike Group’s Arrival in the Eastern Mediterranean
Introduction: A Calculated Move in a Volatile Theater The USS Gerald R. Ford Carrier Strike Group’s recent deployment to the Eastern Mediterranean is an unmistakable [more…]
Unpacking the ‘HTTP/2 Rapid Reset’ Zero-Day: The New Face of DDoS Attacks
Introduction: A New Benchmark for Cyber Havoc Imagine a world where web services can be brought to their knees, not by an army of bots [more…]