Search Results for: apple
Top Cybersecurity Penetration Testing Tools for 2023 (Handpicked)
Introduction: Why Are Penetration Testing Tools Indispensable? In a digital landscape fraught with evolving cyber threats, the question is no longer if an attack will [more…]
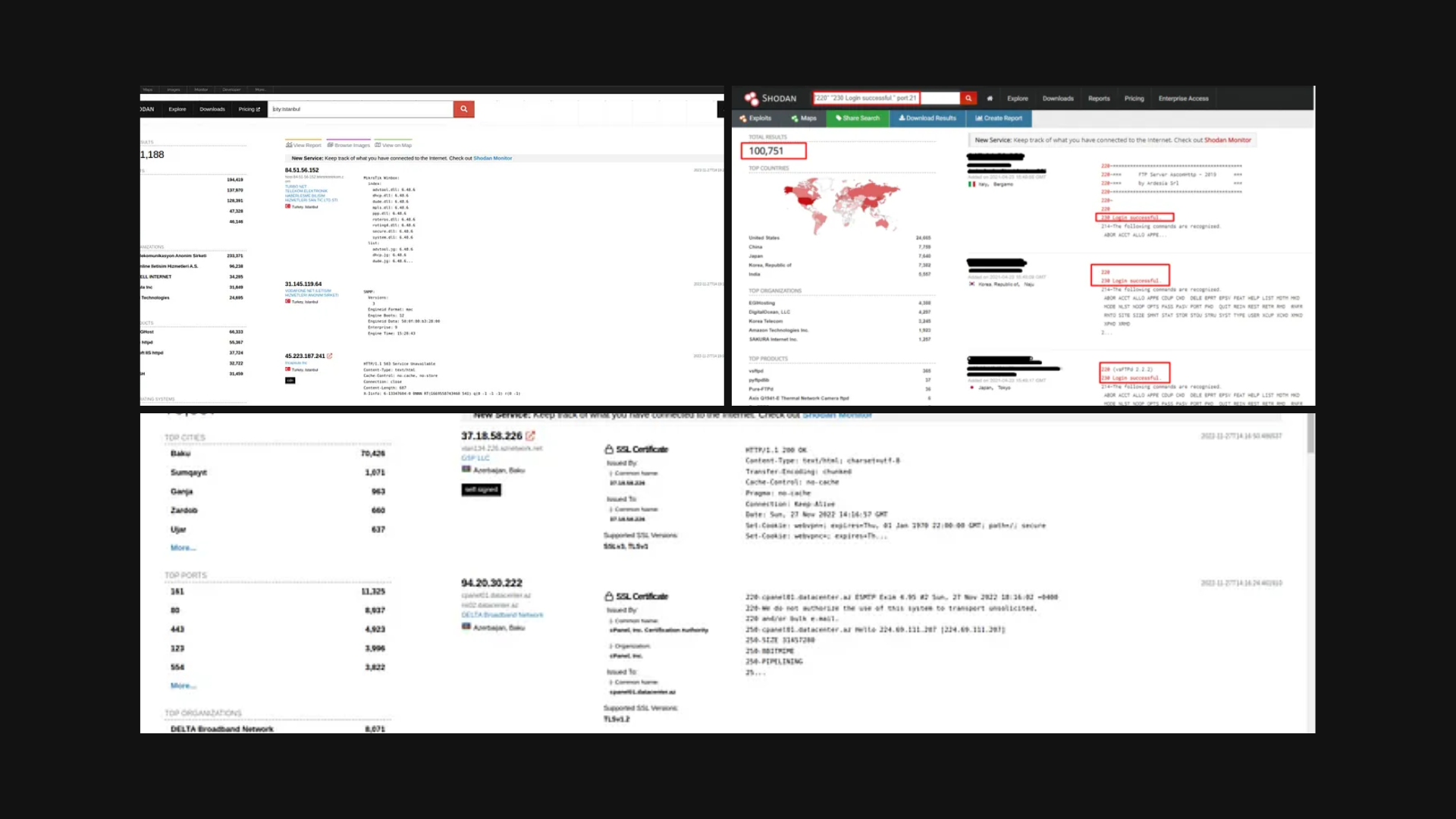
Meet Shodan The Hacker Search Engine
Ever wondered if there’s a search engine that does more than find coffee shops or movie times? What if we told you there’s one that [more…]
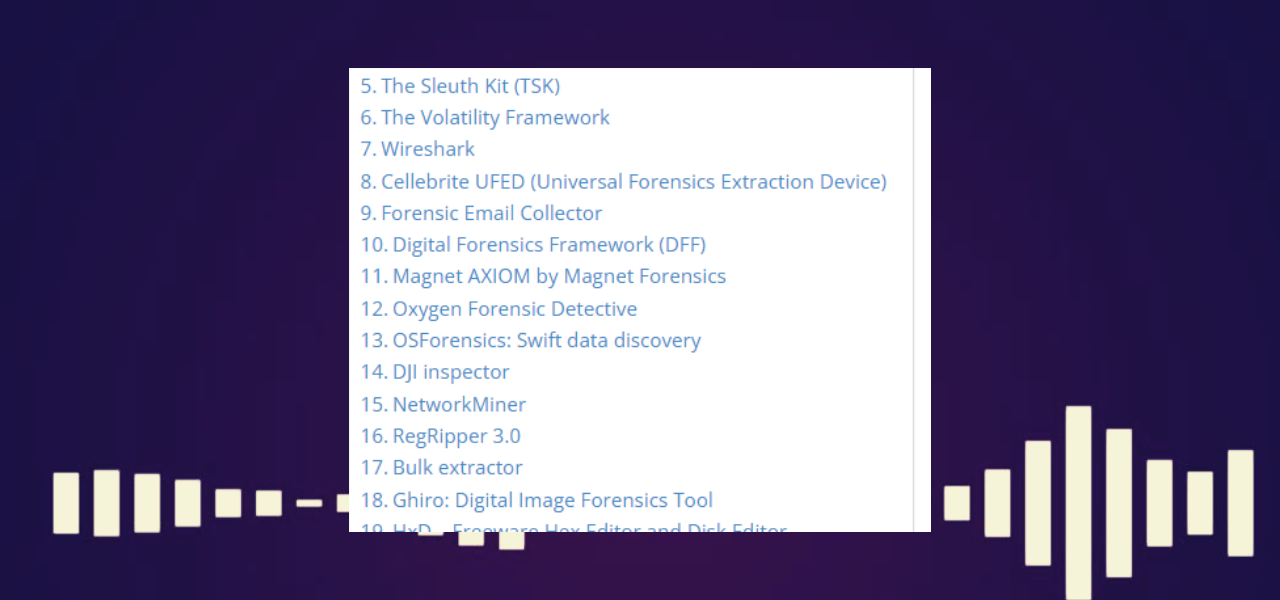
Top Digital Forensics Tools (2023)
Wondering which digital forensics tools are making waves in the cybersecurity landscape? You’ve come to the right place. In this guide, we walk you through [more…]
Five Families Cybercrime Syndicate Strikes Ortambo District in South Africa
What’s the Latest? The Ortambo district in South Africa has fallen victim to a cyberattack carried out by the notorious hacking collective known as the [more…]
Predator Spyware: The Silent Predator Turning Phones Into Surveillance Tools (with video)
Don’t you ever wonder how safe your smartphone really is? In a world where governments seem to be ramping up surveillance, there is a player [more…]
Predator Spyware: The Tale of Ahmed Eltantawy
Don’t you think your phone is your personal sanctuary? A place where your secrets and plans are safe? Citizen Lab’s recent findings beg to differ. [more…]
PhishBuster: Scan for Phishing Pages
In our last blog post, we delved into DirBuster and its utility in pinpointing particular phishing pages. In this installment, we’ll shift our attention to [more…]
How Long Does It Take a Company To Recover From a Ransomware Attack?
As we grapple with the rising tide of cyberattacks, the question isn’t if, but when, will your organization be targeted. Ransomware is one such threat, [more…]
Effortlessly Craft Advanced Python Web Requests
If you’re a cybersecurity enthusiast, you must be familiar with the power of Python. This versatile language, with its wealth of libraries, makes even complex [more…]
Secure a Smile: Top 45 Gift Ideas for Cybersecurity Professionals
Looking for the perfect gift for your cybersecurity-loving friend or family member? We’ve got you covered with our top picks for gifts that cater to [more…]