Search Results for: malware
Your Eyes on Suspicious RDP Logins
Hello, fellow threat hunters! If you’re here, you’re obviously on the prowl for malicious activities in your network. Today, we’re looking at an old favorite [more…]
How a Single Infected Stick Compromised a European Hospital
If you’re a cybersecurity enthusiast, then you must know about the recent malware attack on a European hospital. Today we delve into how a seemingly [more…]
How To Hide Virtual Machine Detection in VirtualBox
Virtual machines are a cybersecurity professional’s best friend. They provide an insulated environment for testing, vulnerability scanning, and more. But, they’re also a beacon for [more…]
Why Hackers Target Fortinet VPN
The Fortinet VPN is known for its robust and secure environment. It’s a favorite for businesses across the globe. Why? Simply because it provides a [more…]
10 Signals That It Is Time To Find A New Challenge In Cybersecurity
Ever felt like your cybersecurity job has turned into a mundane routine? Has the thrill of solving complex issues turned into a mere task? That’s [more…]
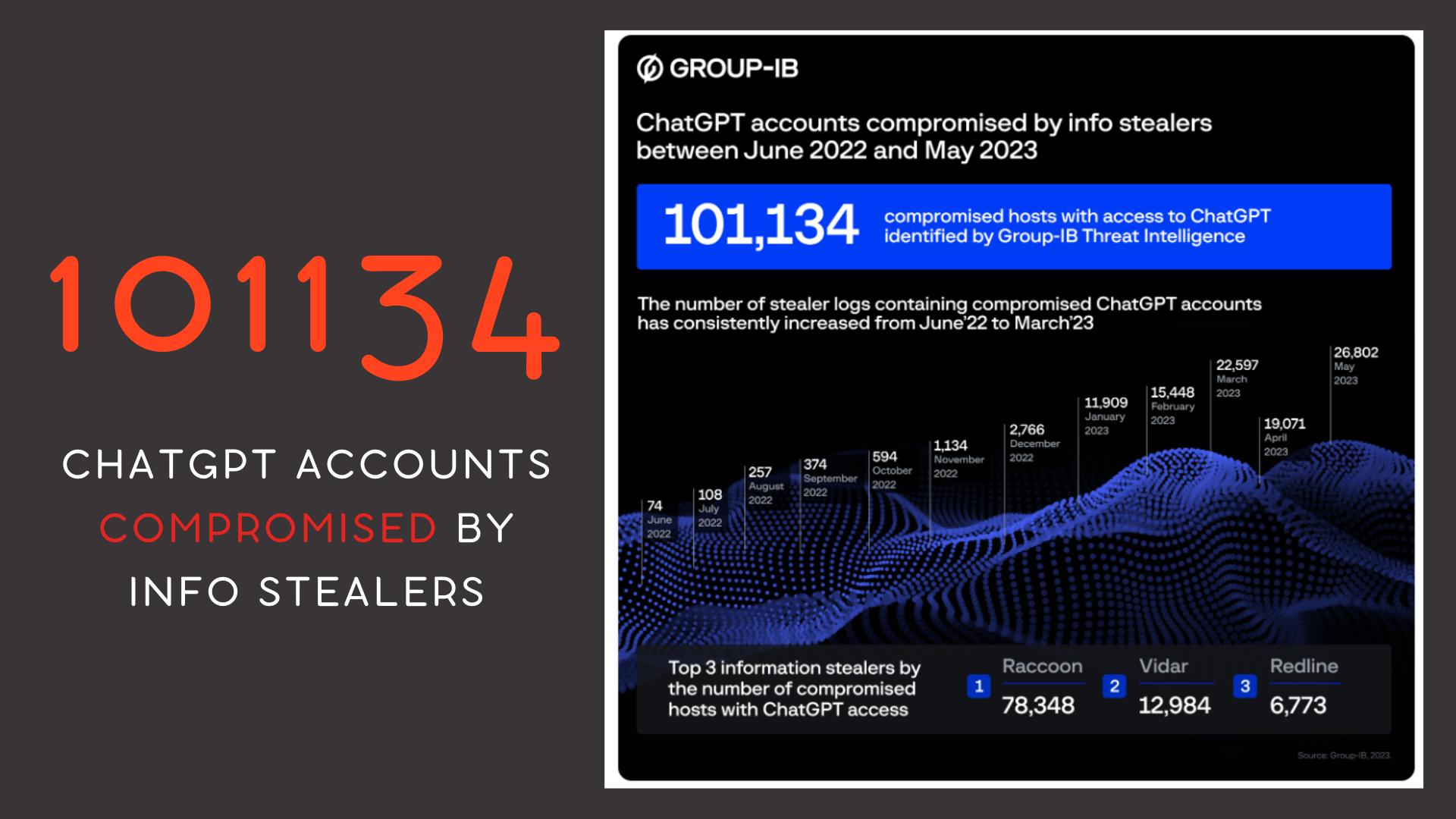
Over 100K ChatGPT Accounts Compromised; APAC Region Heavily Targeted
Cybersecurity firm Group-IB has unearthed evidence of 101,134 infected devices holding stored ChatGPT credentials, with the Asia-Pacific region emerging as a particular hotspot. Data extracted [more…]
Premade YARA rules for hunting
If you’re on the hunt for YARA rules, let me be your guide to some invaluable resources. The directories I’ve rounded up for you here [more…]
The Story of DcRAT, an Emerging Threat
If you’re an avid follower of cybersecurity developments, then you’ll love this piece we’re sharing today. A fascinating tale from the front lines of cybersecurity, [more…]
The YARA User Guide: How to Install and Scan for .onion Strings
The power of YARA is undisputed in the world of cybersecurity, proving to be an essential tool for hunting malware. Here’s a quick guide on [more…]
Ransomware Attack: A Nightmare for IT Teams
When a ransomware attack happens, an IT team’s routine tasks are immediately put on hold. A ransomware attack is a virtual hostage situation where the [more…]