Category: Threat Hunting
Our “Threat Hunting” category is a dedicated hotspot for insights into the proactive pursuit of potential threats. Plunge into in-depth guides, strategic tips, real-life case scenarios, and the latest trends in this crucial aspect of cybersecurity.
View the IP address of a website behind CloudFlare
When you are a cybersecurity professional, it is sometimes needed to get the real IP address of a website which is using Cloudflare as a [more…]
Unveiling CVE-2017-11882: Microsoft Office’s Vulnerability Exploited by Cybercriminals
In the dynamic landscape of cyber threats, one vulnerability stands out for its potential to wreak havoc across systems and networks. CVE-2017-11882, a critical security [more…]
The Best Guide to Cyber Threat Intelligence Training for Technical Experts
Imagine you’re a guardian, a silent protector in the vast digital universe. Your job? To shield critical data from the clutches of malicious entities. Here, in this [more…]
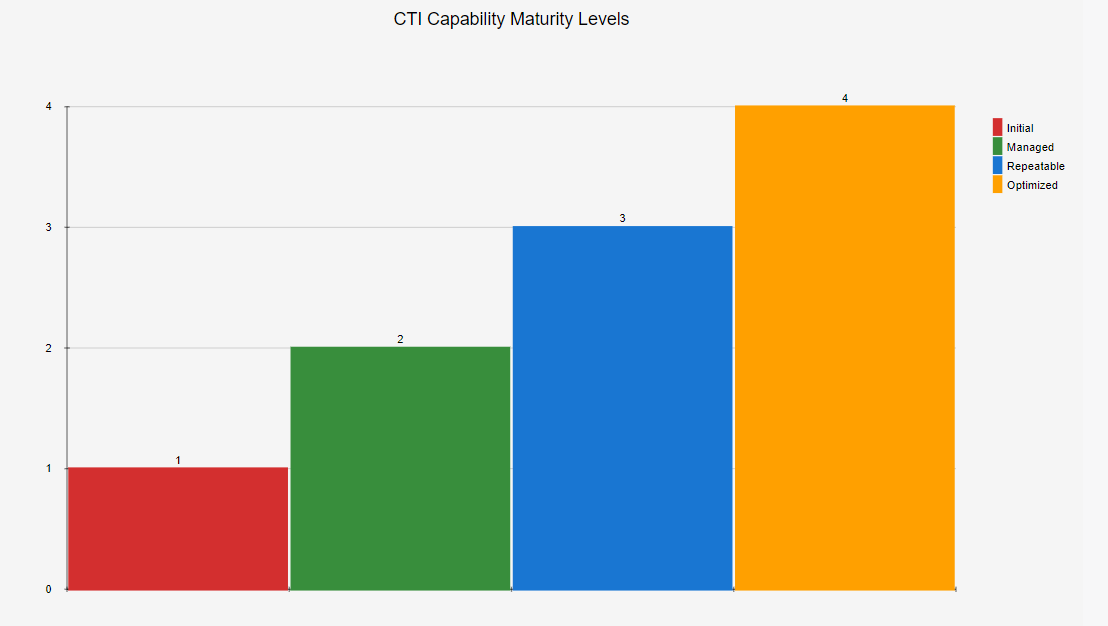
Cyber Threat Intelligence Maturity Model: What It Is and Why It Matters
Think about the digital world as an untamed wilderness; vast, beautiful, yet teeming with potential dangers. That’s where the ‘cyber threat intelligence maturity model’ steps [more…]
CVE-2023-3519: A quick Overview
The recent discovery of the CVE-2023-3519 vulnerability in Citrix systems has raised significant concerns in the cybersecurity community. This article provides a comprehensive overview of [more…]
Who or What Is The Royal Ransomware?
The Royal Ransomware is a cyber threat that first emerged in January 2022. The group behind it was initially known as “Zeon” and later renamed [more…]
What is Storm-0978 (RomCom)?
Storm-0978, this Advanced Persistent Threat (APT) group has been linked to a series of high-profile cyber-espionage campaigns. But who are they, and what are their [more…]
PlugX Remote Access Trojan
The notorious PlugX remote access trojan has been identified adopting a disguise as an open-source Windows debugger tool named x64dbg. This tactic aims to evade [more…]
Cyber Awareness: Recognizing Phishing Attacks
Phishing attacks pose a significant threat to your online security. Cybercriminals employ deceptive tactics to trick individuals like you into revealing sensitive information, such as [more…]
Cyber Awareness: Understanding Cyber Threats
In today’s world, it is vital to be aware of the lurking dangers of cyber threats. In this guide, we will explore the significance of [more…]