On March 1, 2026, attackers hit Iranian apps and websites after U.S.-Israeli strikes, including BadeSaba, a widely used prayer-times and religious calendar app with more than 5 million downloads. Reports from Reuters, WIRED, and The Wall Street Journal made clear why the incident mattered: the app was not just defaced or taken offline. It was used to push surrender-style and anti-regime messages to ordinary users during a live regional crisis.
That detail changes how the incident should be read. BadeSaba was a trusted civilian app with routine daily reach, which made it useful not only as a technical target but as a channel for influence. The point was not simply to break software. It was to reach people at scale through a platform they already used and trusted.
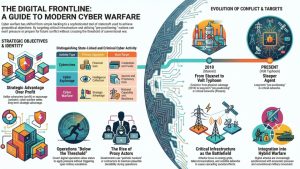
This is an important shift in modern cyberwarfare. More operations now aim to exploit trusted civilian apps, identity systems, and communications platforms because they offer something many military targets do not: direct access to perception, behavior, and public confidence during conflict. The BadeSaba breach is a useful case study because it shows how cyberwarfare can move through everyday digital services, not just government networks or industrial systems.
Why trusted civilian apps work so well as cyberwarfare targets
Trusted civilian apps offer three things attackers want during conflict: reach, credibility, and timing. Reach matters because a popular app already has a large installed audience. Credibility matters because users are more likely to believe or engage with messages delivered through a familiar service than through an unknown website or anonymous channel. Timing matters because those messages can be pushed into daily life exactly when fear, confusion, and uncertainty are already high.
BadeSaba illustrates this clearly. It was not an obscure tool used by a narrow technical audience. It was a mainstream app tied to routine religious practice and daily schedules, which made it part of ordinary civilian life. That made it useful as a delivery channel for coercive messaging during a live crisis.
This is one reason cyberwarfare is no longer only about taking systems down. Sometimes the more effective move is to keep the service recognizable enough that users trust what appears on their screen, while using that trust to shape perception and behavior. In that sense, the app itself becomes both the target and the weapon.
The same broader logic appears in our reporting on identity systems becoming targets in the Iran cyberwar, where civilian-facing platforms became tools of pressure and control rather than just technical assets to disrupt.
Why this matters beyond Iran
The BadeSaba incident matters because the underlying logic is portable. Any trusted civilian app with broad daily use can become attractive during conflict if it gives attackers a way to inject messages, create confusion, or undermine confidence at scale. The target does not need to be a military platform to produce strategic effect.
That is why this kind of operation sits comfortably inside a wider cyberwarfare pattern. It uses civilian-facing infrastructure to shape the environment around a conflict rather than simply to steal data or destroy machines. In practice, that means cyber pressure can move through apps, portals, and identity-linked services long before a government network or military system becomes the headline target.
We have already seen related signs elsewhere in this cluster. In our analysis of why cyberwarfare hits civilian companies first, we looked at how strategically relevant firms become pressure points. In our analysis of spillover, retaliation, and control in the Iran cyberwar, we showed how civilian systems can carry broader geopolitical pressure across sectors and borders.
The lesson is not that every hacked app is an act of cyberwarfare. It is that during periods of real tension, compromises of trusted civilian platforms can serve objectives that are psychological, political, and strategic all at once.
What defenders should watch for
Defenders should treat trusted civilian apps as more than routine consumer software when conflict risk is high. The main question is not only whether an app can be taken offline. It is whether it can be used to push messages, manipulate trust, or create public confusion through an interface people already rely on.
That shifts attention toward account recovery flows, privileged administration, notification systems, content publishing controls, and any feature that can change what users see at scale. In an ordinary security incident, those may look like product-integrity problems. In a conflict setting, they can become channels for pressure and influence.
The BadeSaba case is useful because it shows how little technical destruction may be required to create strategic effect. Attackers do not always need to erase data or cripple infrastructure. Sometimes they only need temporary control over a trusted digital surface and a moment of high public tension.
That is also why it helps to separate these operations from ordinary cybercrime. Our guide on questions to ask before calling an incident cyberwarfare and our article on the differences between cyberwarfare and cyber espionage provide a clearer framework for making that distinction.
Trusted apps are now part of the cyberwarfare surface
The BadeSaba breach showed how a familiar civilian app can be repurposed during conflict to deliver pressure, messaging, and psychological effect at scale. That is why incidents like this deserve more than a narrow app-security reading. They show how cyberwarfare increasingly exploits trusted digital surfaces that people use every day.
For defenders, the lesson is direct: when geopolitical tension rises, popular civilian platforms should be assessed not only as software products but as potential channels for influence. In modern cyberwarfare, the most important target is not always the system itself. Sometimes it is the trust built around it.