Digital Espionage & Intelligence
Coverage of cyber espionage, intelligence operations, surveillance technologies, information theft, counterintelligence trends, and geopolitical motivations driving covert digital campaigns between nation-states and advanced threat groups.
-
Handala Rebounds After FBI Seizure, Exposing Iran Cyberwar Resilience
After the FBI and DOJ seized Handala-linked domains on March 20, 2026, the Iran-linked group restored its web presence within about a day. The case shows why domain takedowns disrupt visibility faster than capability.
-
Iran Cyberwar: Identity Systems Become the Target
After the March 11, 2026 Stryker cyberattack, evidence shows a shift in the Iran cyberwar: attackers are targeting identity systems and endpoint management platforms to disrupt global operations.
-
Iran Cyberwar Shifts to Spillover, Retaliation, and Control
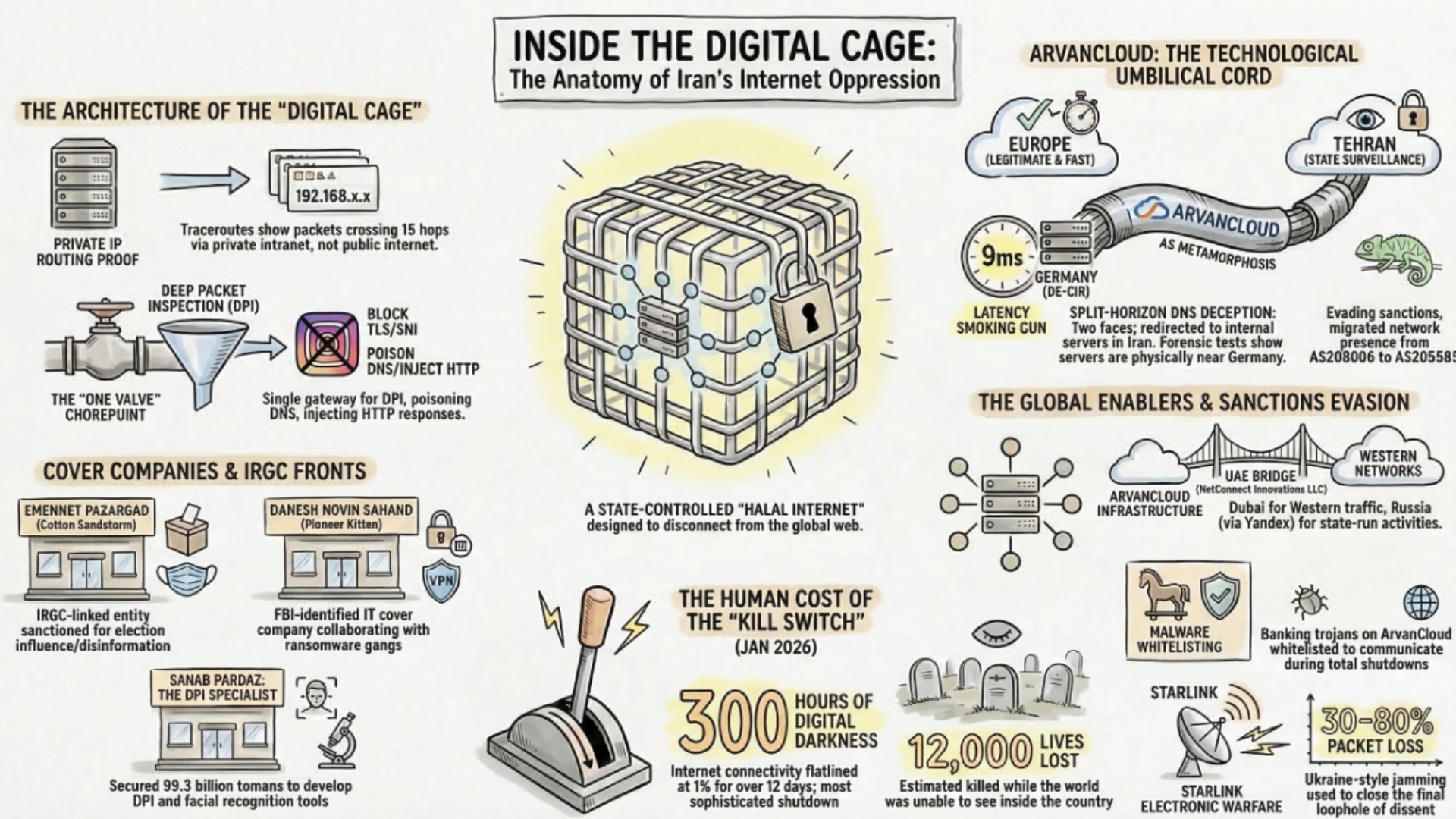
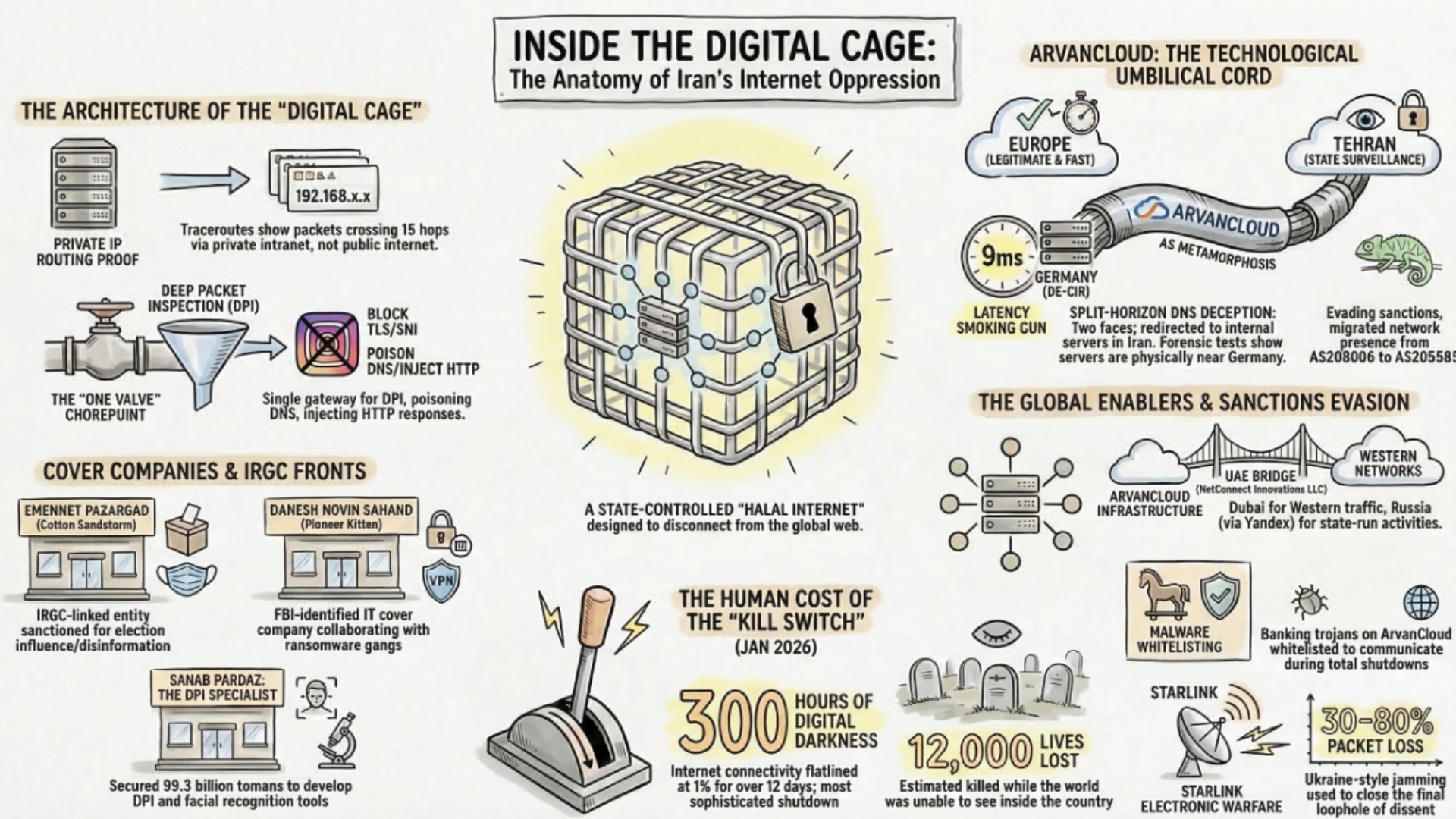
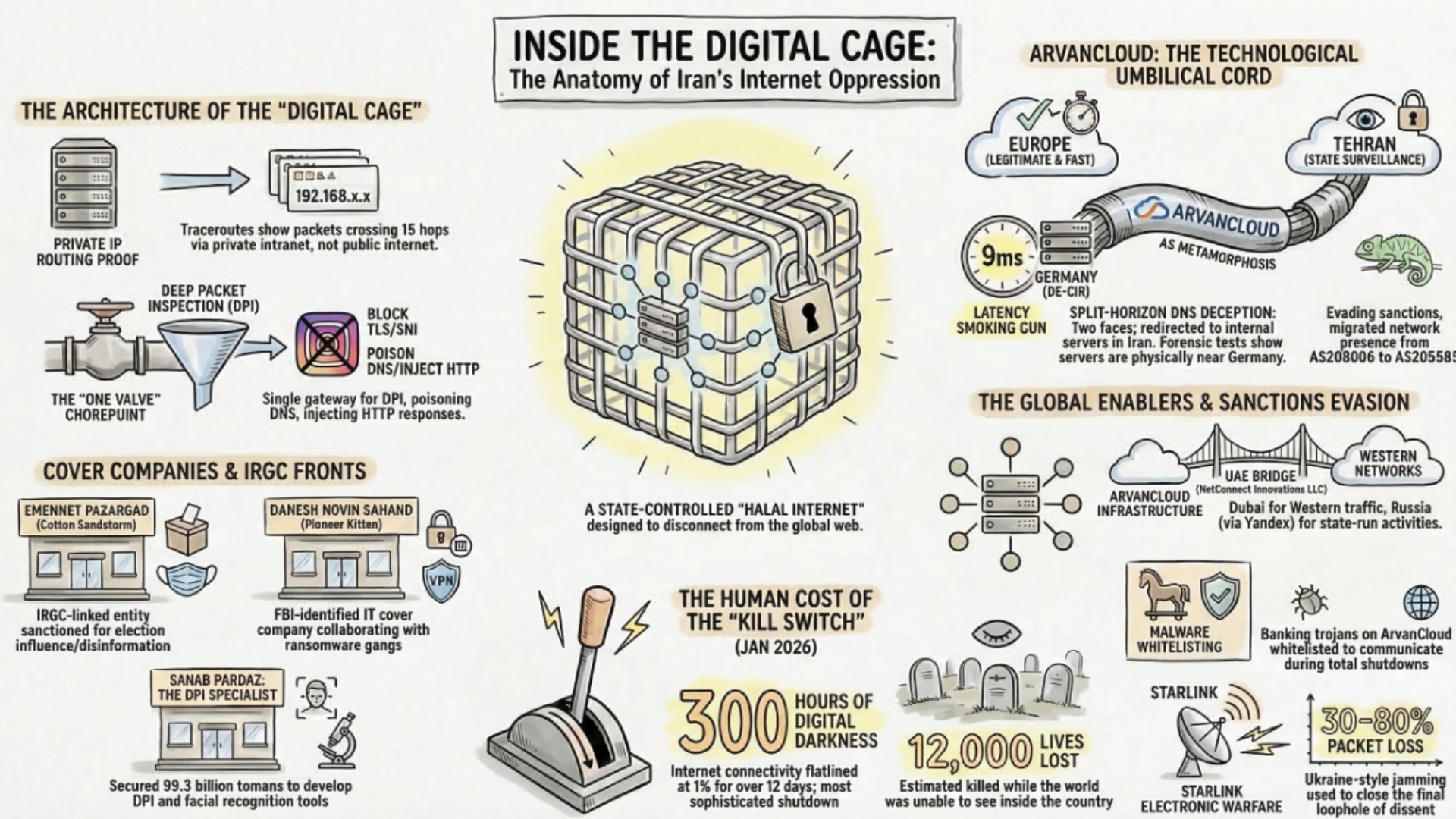
The cyber dimension of the Iran war is no longer limited to isolated attacks. From internal repression and internet shutdowns to suspected Iran-linked retaliation abroad, a multi-layered cyber conflict is emerging with direct implications for healthcare, shipping, and critical infrastructure.
-

Hong Kong Police Can Demand Phone Passwords Under New Security Law
Hong Kong police can now legally demand phone and computer passwords from individuals suspected of breaching the National Security Law (NSL), with refusal leading to up to one year in jail and hefty fines.
-

FBI Seizes MOIS Leak Sites After Handala Attack Hit Hospitals
The FBI and Justice Department seized four domains allegedly tied to Iran’s Ministry of Intelligence and Security, linking the Handala operation to leak-site activity, the 2022 Albania hacks, and the Stryker incident that prosecutors said disrupted hospital communications in Maryland.
-

Dutch Police Employee Critical of Iranian Regime Shot in Schoonhoven
A 36-year-old Dutch police employee of Iranian descent was seriously injured in a shooting in Schoonhoven on March 19. Dutch authorities said the victim had spoken out against the Iranian regime and are investigating all possible scenarios.
-

Lebanon Death Toll Tops 1,000 as Israeli Bombardment Continues
Lebanon’s Health Ministry says Israeli attacks have killed 1,001 people since March 2, including women, children and healthcare workers, as UN and rights groups warn the bombardment may amount to war crimes.
-

Pentagon Seeks $200 Billion for Iran War With No End Date in Sight
Pete Hegseth’s refusal to give a timeframe for the Iran war, alongside a reported $200 billion Pentagon funding request, has sharpened questions over congressional authority, fiscal support and war aims.
-

Trump’s Pearl Harbor Remark Exposes Japan’s Iran War Dilemma
Donald Trump’s Oval Office remark to Japanese Prime Minister Sanae Takaichi exposed the awkward politics of pressuring Tokyo to support Hormuz security operations while the Iran war drives energy and alliance strain.
-

Haifa Refinery Hit as Iran Expands Retaliation to Israeli Energy Sites
An Iranian strike on Haifa’s Oil Refineries Ltd site caused localized power disruption on March 19, extending the energy war from Gulf gas facilities into Israeli infrastructure even as officials said the damage was limited.