Cyber & Electronic Warfare
In-depth coverage of modern cyber and electronic warfare, including offensive capabilities, defensive strategies, jamming, spoofing, information operations, and the evolving integration of digital and electromagnetic conflict.
-

Top 10 OT and ICS Risks in Modern Cyberwarfare
A practical evergreen guide to the 10 OT and ICS risks that matter most in modern cyberwarfare, with a focus on disruption potential, safety, visibility, and strategic leverage.
-

Top 10 Cyberwarfare Doctrine Ideas Security Leaders Should Understand
A practical evergreen guide to the 10 cyberwarfare doctrine ideas security leaders should understand, from deterrence and persistence to escalation, signaling, and strategic ambiguity.
-

Top 10 Attribution Problems in State-Linked Cyber Operations
A practical evergreen guide to the 10 hardest attribution problems in state-linked cyber operations, with a focus on ambiguity, false flags, proxies, timing, and strategic interpretation.
-
Iran Cyberwar: Identity Systems Become the Target
After the March 11, 2026 Stryker cyberattack, evidence shows a shift in the Iran cyberwar: attackers are targeting identity systems and endpoint management platforms to disrupt global operations.
-
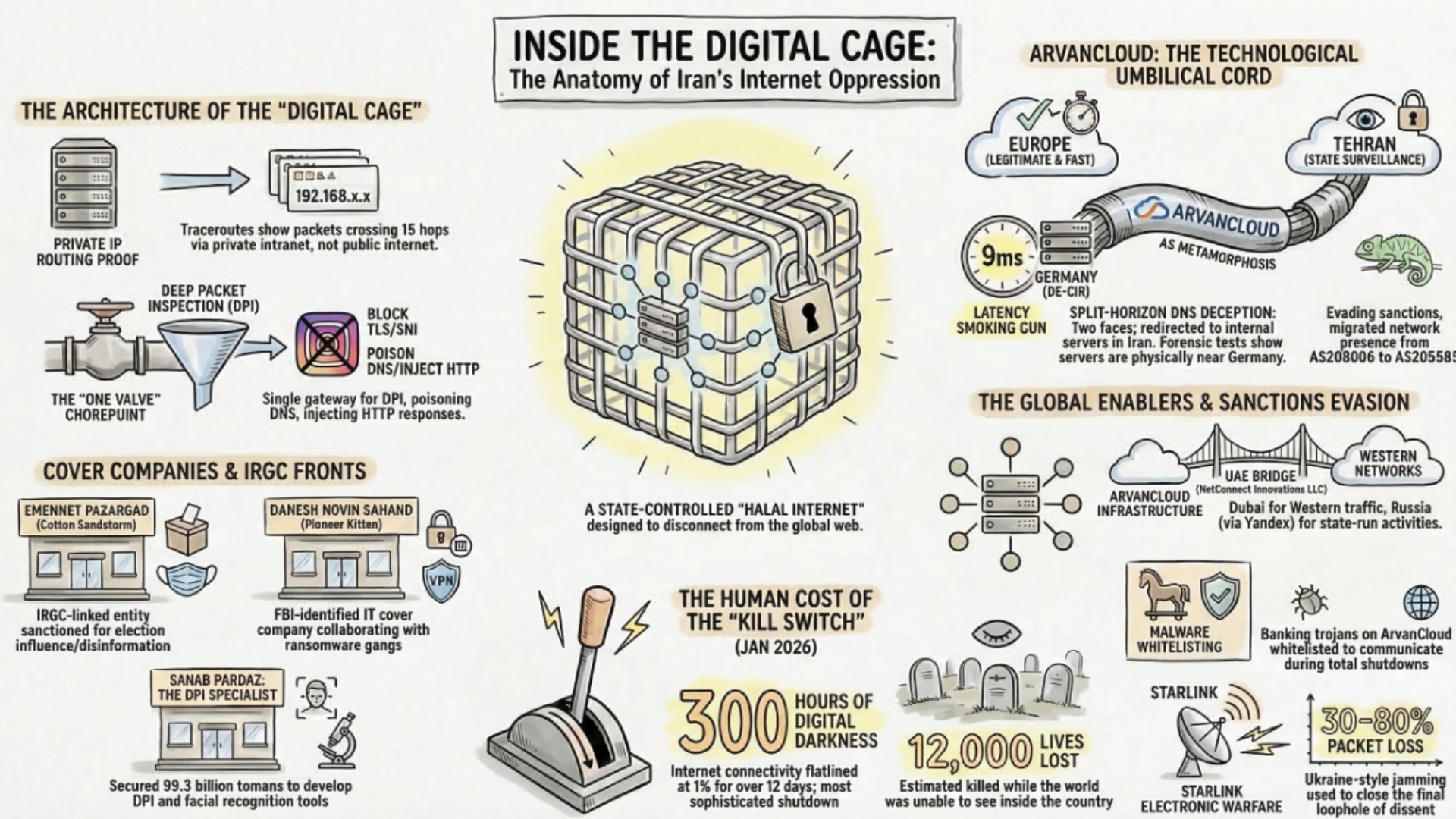
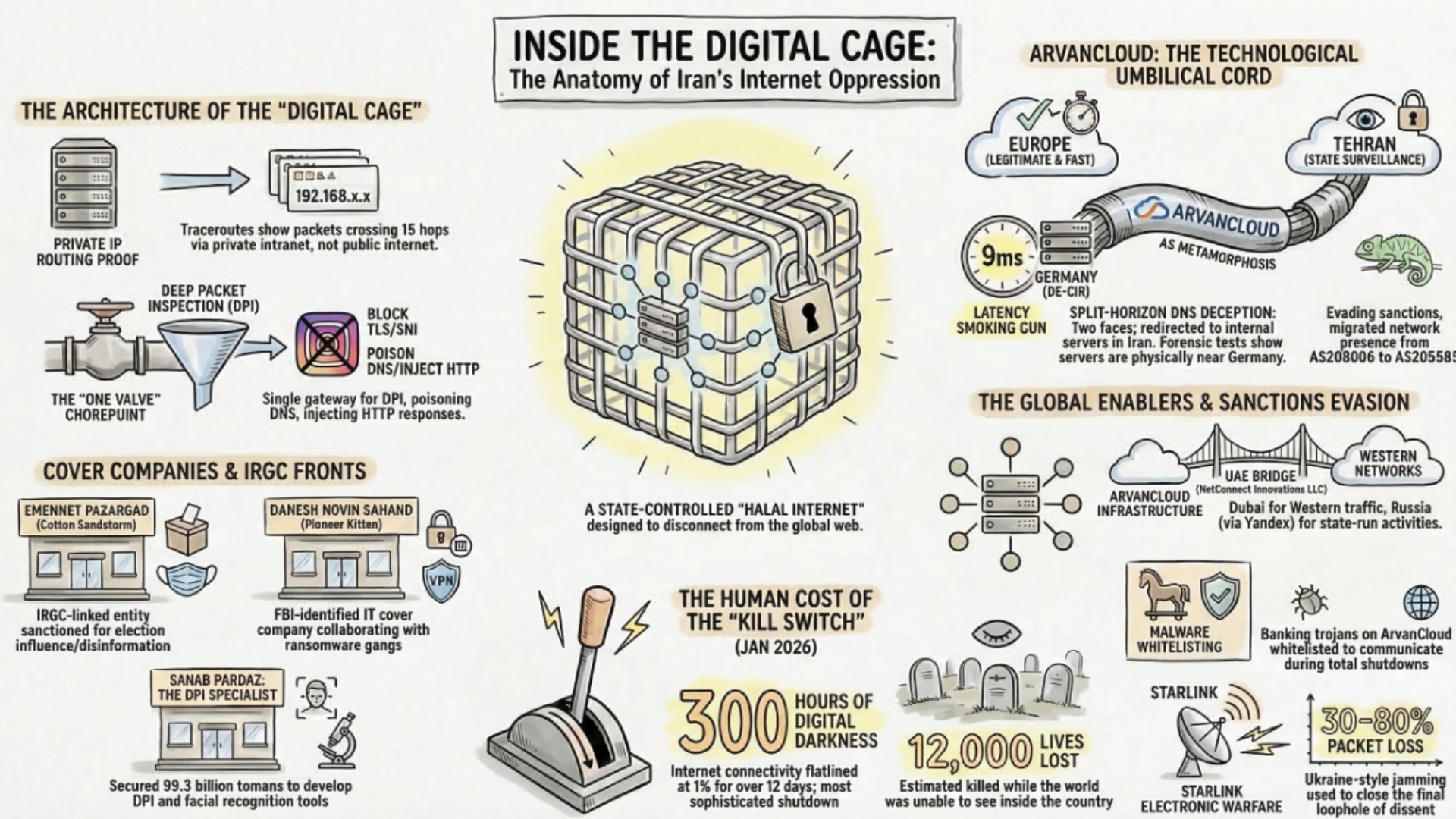
Iran Cyberwar Shifts to Spillover, Retaliation, and Control
The cyber dimension of the Iran war is no longer limited to isolated attacks. From internal repression and internet shutdowns to suspected Iran-linked retaliation abroad, a multi-layered cyber conflict is emerging with direct implications for healthcare, shipping, and critical infrastructure.
-

Top 10 Critical Infrastructure Sectors Most Exposed in Cyberwarfare
A practical evergreen guide to the 10 critical infrastructure sectors most exposed in cyberwarfare, with a focus on strategic value, disruption potential, and systemic impact.
-

Top 10 Below-Threshold Cyber Operations States Use
A practical evergreen guide to the 10 ways nation states use cyber operations below the threshold of war to coerce, signal, prepare, and apply pressure without triggering open conflict.
-

Top 10 Differences Between Cyberwarfare and Cyber Espionage
A practical evergreen guide to the 10 differences between cyberwarfare, cyber espionage, and cyber sabotage, with a focus on objectives, target selection, effects, and strategic meaning.
-

Top 10 Signs a Cyber Campaign Is Pre-Positioning for Future Conflict
A practical evergreen guide to the 10 signs a state-linked cyber campaign may be pre-positioning inside critical infrastructure or strategic networks for future disruptive use.
-

Gulf States Create Safe Sea Corridor as Hormuz Risk Rises
Bahrain, Japan, Panama, Singapore, the United Arab Emirates, and the International Chamber of Shipping agreed on March 18 to create a safe sea corridor to protect seafarers and commercial traffic as risks rise around the Strait of Hormuz and the wider Gulf.