In March 2026, Stryker, a major U.S. medical technology company, said a cyber incident had disrupted ordering, manufacturing, and shipping systems across parts of its business. Around the same period, public reporting said an Iranian-linked group had claimed responsibility for the attack. Those details matter because Stryker does not sit at the edge of healthcare. It sits inside the supply and operational systems that help hospitals, providers, and care networks keep functioning.
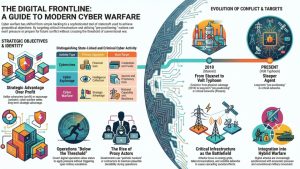
That is why incidents like this deserve more than a narrow corporate-security reading. Modern cyberwarfare often returns to healthcare and medical supply chains because they offer a combination attackers value: high visibility, civilian dependence, and the ability to generate pressure without striking a military network directly. In Stryker’s own updates, the company said patient-related services and connected medical products were not affected, but the disruption still hit core business operations that matter to the wider healthcare ecosystem.
This pattern extends beyond one company. Public reporting in March also tied Iranian cyber actors to attacks that hit hospitals, reinforcing a broader point: healthcare-adjacent targets can produce strategic effect because disruption lands in a sector people immediately recognize as critical. That makes the Stryker case a useful way to explain why cyberwarfare keeps returning to healthcare and medical supply chains during periods of real-world tension.
Why healthcare and medical supply chains keep coming back as targets
Healthcare remains attractive in cyberwarfare because it combines operational importance with public sensitivity. A disruption in this sector is immediately legible to the public, politically difficult to ignore, and capable of producing pressure far beyond the organization that was initially hit. Attackers do not need to breach a defense ministry to create strategic effect if they can interfere with systems tied to care delivery, medical logistics, or hospital operations.
Medical supply chains are especially exposed because they sit between manufacturers, distributors, providers, and patients. When ordering, manufacturing, or shipping systems are disrupted, the impact can travel outward quickly even if patient-facing systems remain online. That was part of the lesson from the Stryker incident. The company said patient-related services and connected medical products were not affected, but the disruption still hit operational functions that matter to the wider healthcare ecosystem.
This is also why healthcare-adjacent companies deserve attention, not only hospitals themselves. In our analysis of why cyberwarfare hits civilian companies first, we showed how strategically relevant private firms can become pressure points during conflict. Healthcare suppliers fit that pattern well because they are civilian entities with real downstream consequences when operations are disrupted.
What makes healthcare strategically useful in cyberwarfare
Healthcare targets are strategically useful because disruption here produces immediate human and political resonance. A cyber incident affecting a hospital, medical supplier, or healthcare service provider is easier for the public to understand than a breach inside a back-office government network. That visibility gives attackers a way to create pressure, fear, and urgency without needing to conduct a dramatic strike against a military system.
There is also a classification advantage for attackers. Incidents touching healthcare can be described as cybercrime, hacktivism, retaliation, or sabotage depending on the evidence available, which helps preserve ambiguity. That ambiguity matters in cyberwarfare because it can slow response, complicate attribution, and create room for escalation without a clean threshold crossing.
We have seen similar logic elsewhere in this cluster. In our report on the FBI seizure of sites linked to attacks that hit hospitals, the healthcare angle mattered because the targets amplified public consequence. In our analysis of critical infrastructure sectors most exposed in cyberwarfare, we showed why sectors tied to daily dependence remain attractive pressure points during conflict.
What defenders should prioritize in this sector
For defenders in healthcare and adjacent supply chains, the key question is not only whether patient systems are directly hit. It is whether ordering, distribution, scheduling, manufacturing, or identity-linked systems can be disrupted in ways that create downstream stress across care delivery. Those are the layers that can turn a single corporate incident into a sector-wide pressure point.
That means security teams should pay particular attention to administration platforms, remote management, order-processing systems, supplier connectivity, and recovery paths that support continuity when normal operations are interrupted. In a conflict setting, these functions are not just IT plumbing. They are part of the operational surface that keeps care ecosystems moving.
The broader lesson is simple: healthcare cyber defense cannot be limited to hospitals alone. It has to include the manufacturers, software providers, distributors, and service firms that keep medical systems supplied and functioning. That is what makes medical supply chains such a recurring cyberwarfare target during periods of geopolitical tension.
Healthcare remains a pressure point in modern cyberwarfare
The March 2026 Stryker incident and the hospital-linked Handala case point to the same conclusion: healthcare and medical supply chains remain attractive because they sit close to civilian life, public confidence, and operational continuity. Attackers do not need to strike a military target directly when disruption in this sector can generate visible pressure on its own.
That is why healthcare keeps reappearing in cyberwarfare. It offers strategic leverage through systems that are civilian, essential, and difficult to separate cleanly from everyday resilience. For defenders, the lesson is to treat the wider healthcare ecosystem as part of the conflict surface, not just the hospital network itself.