In March 2026, the BadeSaba breach showed how a trusted civilian app could be used to push surrender-style and anti-regime messages during a live regional crisis. That mattered because the app was not just another digital service. It functioned as part of the wider information environment people relied on during a moment of fear, uncertainty, and rapid decision-making.
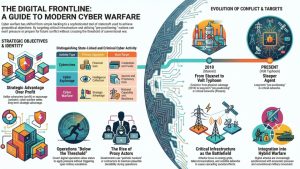
Crisis coordination and public messaging systems are attractive in cyberwarfare because they sit close to human behavior. If attackers can influence the channels people use to receive alerts, guidance, updates, or trusted instructions, they can shape perception and reaction without needing to destroy infrastructure directly. That makes these systems useful when the goal is pressure, confusion, or loss of confidence.
This is why cyberwarfare keeps returning to civilian-facing platforms that influence trust and timing during emergencies. The issue is not only whether a system can be taken offline. It is whether pressure on that system can distort how institutions communicate and how the public interprets events during a crisis. The March 2026 BadeSaba case made that logic visible again.
Why crisis coordination and public messaging systems keep coming back as targets
These systems remain attractive in cyberwarfare because disruption here is both psychological and operational. If a trusted app, alerting channel, or public-facing platform becomes unreliable, the effect does not stay inside one service. It spills into public behavior, institutional credibility, and the speed at which people can verify what is happening around them.
That wider effect is part of the appeal. Attackers do not need to cause physical destruction to create pressure if they can instead interfere with how warnings, guidance, and narratives move through civilian life during a crisis. Even uncertainty about whether a messaging platform can be trusted can slow response and increase confusion.
This fits the broader cyberwarfare pattern we have been documenting across the cluster. In our analysis of spillover, retaliation, and control in the Iran cyberwar, we showed how civilian-facing systems become vehicles for broader geopolitical pressure. Crisis coordination and public messaging systems belong in that category because they shape how people interpret and react to unfolding events.
What makes crisis coordination and public messaging systems strategically useful in cyberwarfare
These targets are strategically useful because they connect digital systems with trust, timing, and decision-making. Public alerting channels, trusted apps, identity-linked platforms, and other civilian-facing systems do more than deliver information. They influence whether people believe instructions, whether institutions can coordinate clearly, and whether a crisis feels manageable or chaotic.
There is also a multiplier effect. When trusted messaging systems are disrupted or manipulated, the damage is not limited to one platform. Confusion can spread into transport, healthcare, public safety, and ordinary civilian behavior because many people rely on those channels to judge what is happening and what they should do next. That gives attackers a way to create wider pressure through a relatively narrow intervention.
We have already seen the broader context for this in our analysis of identity systems becoming targets in the Iran cyberwar and in our article on cyberwarfare exploiting trusted civilian apps. Those pieces show the same underlying logic: attackers often gain leverage by pressuring systems people trust during moments when timing and credibility matter most.
What defenders should prioritize in these systems
For defenders, the priority is not only keeping a platform online. It is understanding which systems support trusted notifications, account integrity, content control, administrative access, and continuity when normal communication channels become unreliable. Those are the layers where a contained cyber incident can become a wider public-behavior problem.
It also helps to think in terms of credibility. Crisis coordination systems are most valuable when people believe them quickly. That means resilience planning has to account for fallback channels, rapid verification, account recovery, abuse of messaging features, and clear communication when a trusted platform may have been manipulated.
The broader lesson is simple: these systems are not targeted only because they deliver information. They are targeted because they shape what people believe and how they respond under pressure. In cyberwarfare, that makes them recurring leverage points during crises.
Crisis coordination and public messaging systems remain pressure points in cyberwarfare
The March 2026 BadeSaba case reinforced a familiar reality: crisis coordination and public messaging systems remain attractive because they combine trust, timing, and public behavior. Attackers do not need to strike a military system directly when disruption or manipulation here can generate pressure across the wider civilian environment.
That is why these systems keep reappearing in cyberwarfare. They offer leverage through credibility, confusion, and response timing. For defenders, the lesson is to treat trusted civilian messaging and coordination systems as part of the broader conflict surface, not just as routine app or platform security problems.