In March 2026, Stryker, a major U.S. medical technology company, said a network disruption had affected ordering, manufacturing, and shipping systems across parts of its business. Around the same period, public reporting said an Iranian-linked hacking group had claimed responsibility for the incident, placing the disruption in a much wider geopolitical context than an ordinary corporate cyber event.
That distinction matters. Stryker is not just another private company. It sits inside healthcare delivery and medical supply chains, which means operational disruption can ripple outward into hospitals, providers, and patient care. In its own updates, Stryker said patient-related services and connected medical products were not affected, but the company also confirmed the incident was serious enough to disrupt core business operations while restoration work continued.
There were also technical and policy signals that made the story more significant. Stryker later said investigators, including Palo Alto Networks Unit 42, found that the threat actor used a malicious file to run commands while hiding activity in the environment. Separately, CISA warned organizations to harden endpoint management systems after a major cyberattack against a U.S. organization. Even without a full public technical dossier, the overlap was important because it showed how attacks on enterprise management layers can create real operational pressure on strategically relevant civilian firms.
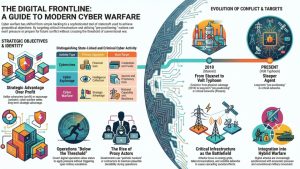
That is why the Stryker incident deserves to be read as more than a one-off breach. Modern cyberwarfare rarely starts with a direct strike on a military network. It often begins with coercive pressure against civilian organizations that are easier to reach, highly visible when disrupted, and deeply connected to national resilience.
Why civilian companies are often the first cyberwarfare targets
The Stryker attack matters because it reflects a pattern security teams have been watching for years: state-linked operators often pressure civilian organizations before anything that looks like open cyber conflict. That approach offers several advantages. It can disrupt supply chains, create public anxiety, test defensive responses, and send a message to governments without directly striking military systems.
In March 2026, Stryker confirmed that a cyber incident disrupted ordering, manufacturing, and shipping systems across parts of its operations. In an official company update, Stryker stated that attackers used a malicious file to execute commands while hiding their activity inside the environment. The company worked with external experts, including Palo Alto Networks Unit 42, to investigate and contain the intrusion. We also covered the government response in our report on CISA’s Microsoft Intune warning after the Stryker cyberattack, which helps show why enterprise management layers matter so much when these incidents hit strategically relevant companies.
What makes this important is not just the disruption itself, but the type of access achieved. By interfering with internal operational systems rather than public-facing services, the attackers were able to create real-world impact on supply chains without directly targeting patients or medical devices. That is a hallmark of modern cyberwarfare pressure: indirect disruption with visible consequences.
For defenders, the lesson is simple: cyberwarfare does not begin only when military networks are hit. It often begins when organizations with strategic relevance become easier, quieter targets.
That is also why it helps to separate true cyberwarfare from other activity. Our guide on the differences between cyberwarfare and cyber espionage explains why disruption and coercive pressure matter more than data theft alone, while our article on questions to ask before calling an incident cyberwarfare offers a more careful classification framework.
Recent events show the same pattern across sectors and borders
The Stryker incident is not important only because of the company involved. It matters because it fits a wider pattern visible across several March 2026 incidents tied to regional escalation.
On March 1, attackers struck Iranian apps and websites after U.S.-Israeli strikes, including BadeSaba, a widely used prayer-times and religious calendar app in Iran with more than 5 million downloads. Reuters first highlighted the disruption, while WIRED and TechCrunch added important context about how the app was used to push anti-regime and surrender-style messages to ordinary users during the strikes. The Wall Street Journal also described BadeSaba as a mass-notification channel that gave the operation broad civilian reach inside Iran. That matters because targeting BadeSaba was not the same as defacing an obscure website. It shows how cyber operations can reach directly into daily civilian life through services people already trust and use routinely. The same logic appears in our reporting on identity systems becoming targets in the Iran cyberwar, where civilian-facing platforms became tools of pressure and control.
Other reporting the same month pointed in the same direction. Greek authorities warned companies in shipping, banking, transport, telecommunications, health, and energy to scan their systems as the Iran war raised cyberattack risks. We covered that development in our report on Greek firms scanning networks as the war raised cyberattack risk, and placed it in a broader pattern in our analysis of how the Iran cyberwar shifted toward spillover, retaliation, and control. Different sources, different countries, and different sectors all pointed to the same strategic pattern: civilian-facing digital systems were being treated as pressure points.
Put together, these events show that cyberwarfare pressure often spreads through civilian infrastructure long before anyone can point to a single decisive strike. It moves through apps, enterprise systems, hospitals, supply chains, and national service providers. That is one reason our article on below-threshold cyber operations states use matters: many of the most consequential operations are designed to stay coercive, disruptive, and politically useful without becoming openly declared war.
What defenders should take seriously when civilian firms become conflict targets
Recent events point to a practical problem for defenders: the first visible sign of geopolitical cyber pressure may be a disruption in ordinary business systems, not a strike against a defense ministry. Reuters reported on March 18, 2026 that Greek organizations in shipping, banking, transport, telecommunications, health, and energy were checking their networks after warnings tied to the Iran war. Those sectors matter because they connect national resilience to civilian operations.
The CISA alert issued on March 18 also matters for the same reason. It warned organizations to harden endpoint management systems after a cyberattack against a U.S. organization. For defenders, that is a reminder that administration layers, cloud management planes, remote tooling, and identity-linked systems can become choke points during a conflict-related intrusion. When those systems are disrupted, downstream business functions can stall quickly.
That pattern fits the warning signs discussed in our article on signs a cyber campaign is pre-positioning for future conflict. It also connects with our coverage of OT and ICS risks in modern cyberwarfare, where disruption can carry direct safety and service consequences.
For security teams, the practical shift is straightforward. Watch for attacks that hit systems governing ordering, scheduling, shipping, communications, remote management, and supply-chain visibility. Those may look like business continuity problems at first. In a period of regional tension, they can also be early indicators of coercive cyber activity.
Why this pattern keeps returning in modern conflict
There is a strategic reason civilian organizations keep appearing at the center of cyber conflict. They are easier to reach than hardened military networks, more visible to the public when disrupted, and often woven into national resilience in ways that governments cannot ignore. A hospital supplier, shipping operator, telecom provider, or logistics platform may be privately owned, but the effects of a serious incident can still ripple across healthcare, trade, communications, and confidence in public stability.
That is what makes the March 2026 Stryker attack more than a single company story. The incident showed how a civilian enterprise can become a pressure point in a larger geopolitical struggle. The same month, civilian apps and websites in Iran were hit after U.S.-Israeli strikes, while Greek organizations in several strategic sectors moved to scan their systems as the war raised cyberattack risks. The targets changed, but the logic stayed the same: use digital pressure where disruption is visible, politically useful, and hard to classify cleanly.
This is also why attribution and deterrence remain so difficult in cyberwarfare. States and state-linked groups can create disruption through civilian systems while preserving ambiguity about intent, proportionality, and threshold. Our coverage of attribution problems in state-linked cyber operations, cyber deterrence problems, and cyber escalation risks helps explain why these incidents are so strategically effective.
The broader lesson is not that every attack on a company is cyberwarfare. It is that during periods of real-world tension, attacks on civilian firms can reveal how cyberwarfare is actually practiced: through pressure, disruption, ambiguity, and leverage against systems people rely on every day.