Tutorials and Guides
Explore detailed Tutorials and Guides — from simple code install, to advanced projects.
-

Service Account Security: How to Control Privilege, Rotation, Ownership, and Trust Paths
Service account security is more than storing passwords in a vault. This practical guide explains how to control non-human identities, reduce privilege scope, assign ownership, rotate credentials safely, monitor trust paths, and avoid the operational shortcuts that turn service accounts into quiet high-value attack paths.
-

Incident Response Playbook: How to Triage, Contain, Investigate, and Recover
An incident response playbook should do more than list phases on a slide. This practical guide explains how to triage fast, contain without destroying evidence, assign decisions clearly, manage communications, and move from investigation to recovery without creating a second incident.
-

Attack Surface Management: How to Find Exposed Assets, Prioritize Risk, and Reduce Drift
Attack surface management is more than scanning the internet for open ports. This practical guide explains how to discover exposed assets, prioritize the risks that matter, validate findings before escalation, and reduce the constant drift that makes external attack surfaces grow faster than teams realize.
-

What Is Zero Trust? A Practical Guide to Identity, Access, and Network Segmentation
Zero trust is not a single product or a marketing slogan. This practical guide explains what zero trust means, how it changes identity, access, and segmentation decisions, where organizations get it wrong, and how to validate whether a rollout is actually reducing risk.
-

What Are Passkeys? How They Work, Why They Matter, and When to Use Them
Passkeys are a phishing-resistant sign-in method built on public-key cryptography and the FIDO/WebAuthn ecosystem. This practical guide explains how passkeys work, where they improve security over passwords and SMS codes, what their limits are, and how to start using them safely.
-

Shadow AI: The Enterprise Risk You Can’t Ignore
Shadow AI is unsanctioned AI use inside the enterprise. Here’s why it creates real security risk across data exposure, identity, compliance, and AI agents.
-

Critical Vulnerability Triage Playbook: How SOCs Prioritize and Patch Critical CVEs
Vulnerability triage: Practical steps SOCs use to prioritize critical CVEs, assign risk, and speed safe patching.
-
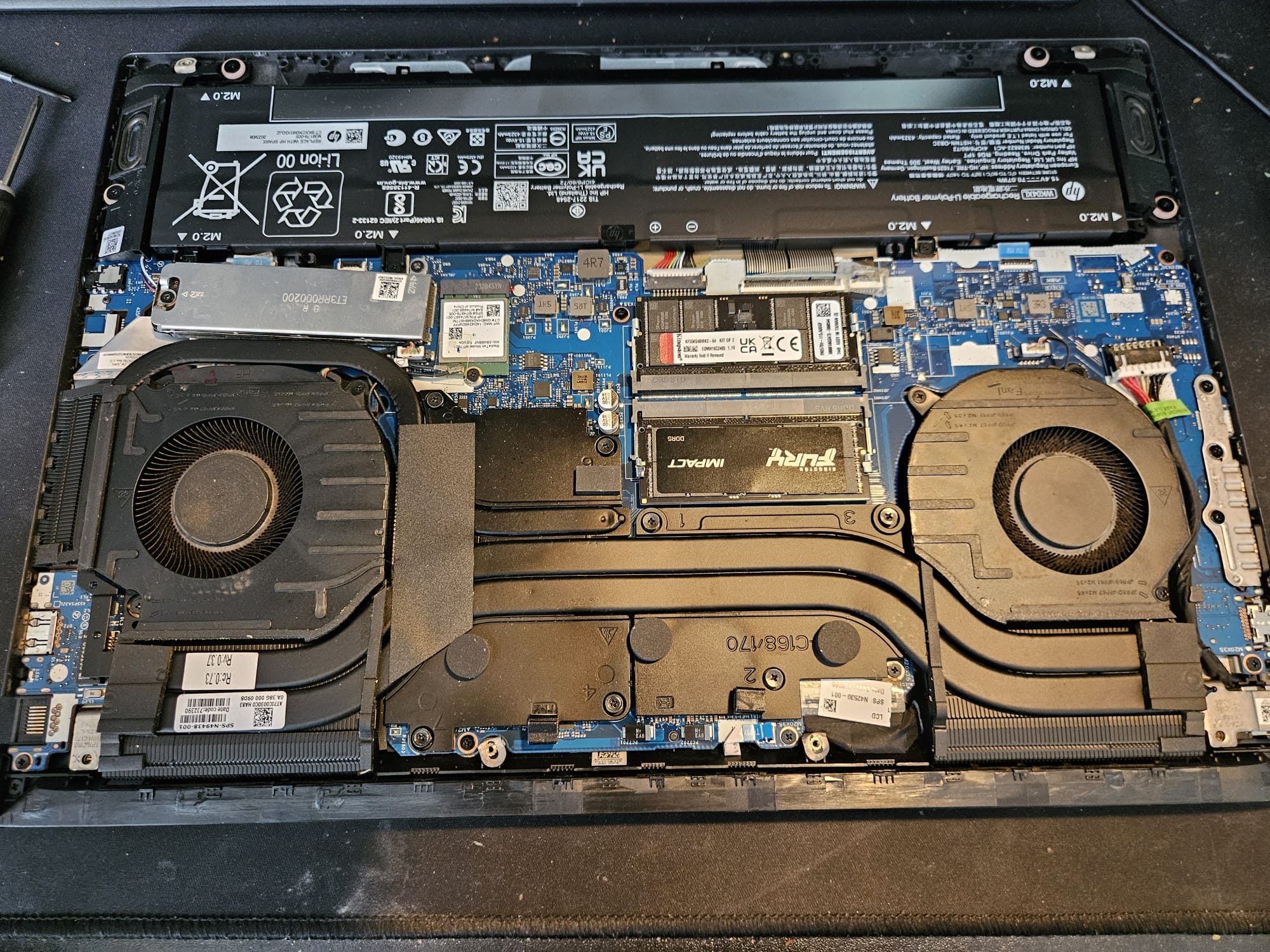
HP Victus 16 Hall Effect Sensor Failure
The HP Victus 16 Hall Effect sensor can fail under heat, causing false lid-closed detection that leads to black screens, flickering displays, sudden shutdowns, and power-on failures that software fixes cannot resolve. A Complete Diagnostic & Permanent Repair Guide for Random Shutdowns Audience note This guide is written for HP Victus Laptop owners: people who…
-

10 Cyber Security Tools for 2025
Cybersecurity tools protect devices, systems, applications, networks, and data from cyber threats. These solutions improve security posture, manage compliance, and maintain reputation, preventing costly fixes.
-

What is EPSS? Exploit Prediction Scoring System
Explainer: what EPSS is and how teams use it to prioritize vulnerabilities.