Search results for: “network security”
Showing results matching your search
Refine your search
-
The 2007 Estonia Cyberattacks and How They Shaped Modern Cyber Defense
The 2007 cyberattacks against Estonia disrupted banks, media, and government systems and reshaped NATO cyber defense policy, turning Estonia into a global cybersecurity leader.
·
·
16–24 minutes -
Aeternum C2 Botnet Abuses Polygon Blockchain to Hide Malware Commands and Evade Takedowns
Security researchers have uncovered a new botnet loader called Aeternum C2 that stores encrypted command-and-control instructions on the Polygon blockchain, making traditional takedown efforts significantly harder and signaling a new evolution in resilient malware infrastructure.
·
·
4–6 minutes -
UAT-10027 Targets U.S. Healthcare with Dohdoor Malware Using DoH C2
Researchers have uncovered a previously undocumented cyber campaign tracked as UAT-10027 targeting U.S. healthcare and education organizations with a new backdoor called Dohdoor that uses DNS-over-HTTPS to evade detection and deploy Cobalt Strike beacons.
·
·
4–6 minutes -
Ransomware Trends 2026: Healthcare, Defense, and Threat Actor Tactics
Ransomware attacks in 2026 continue to disrupt healthcare, with clinic closures and operational outages. Defensive innovations like honeypots and evolving threat actor tactics shape the landscape.
·
·
4–7 minutes -
Fatimion Cyber Team: Inside the Iran-Linked Hacking Group Waging Cyber War Across the Middle East
A pro-Iran cyber group operating out of Iraq has quietly built one of the most persistent hacktivist operations in the Middle East. Known as the Fatimion Cyber Team (فريق فاطميون الالكتروني), this group has been…
·
·
14–22 minutes -
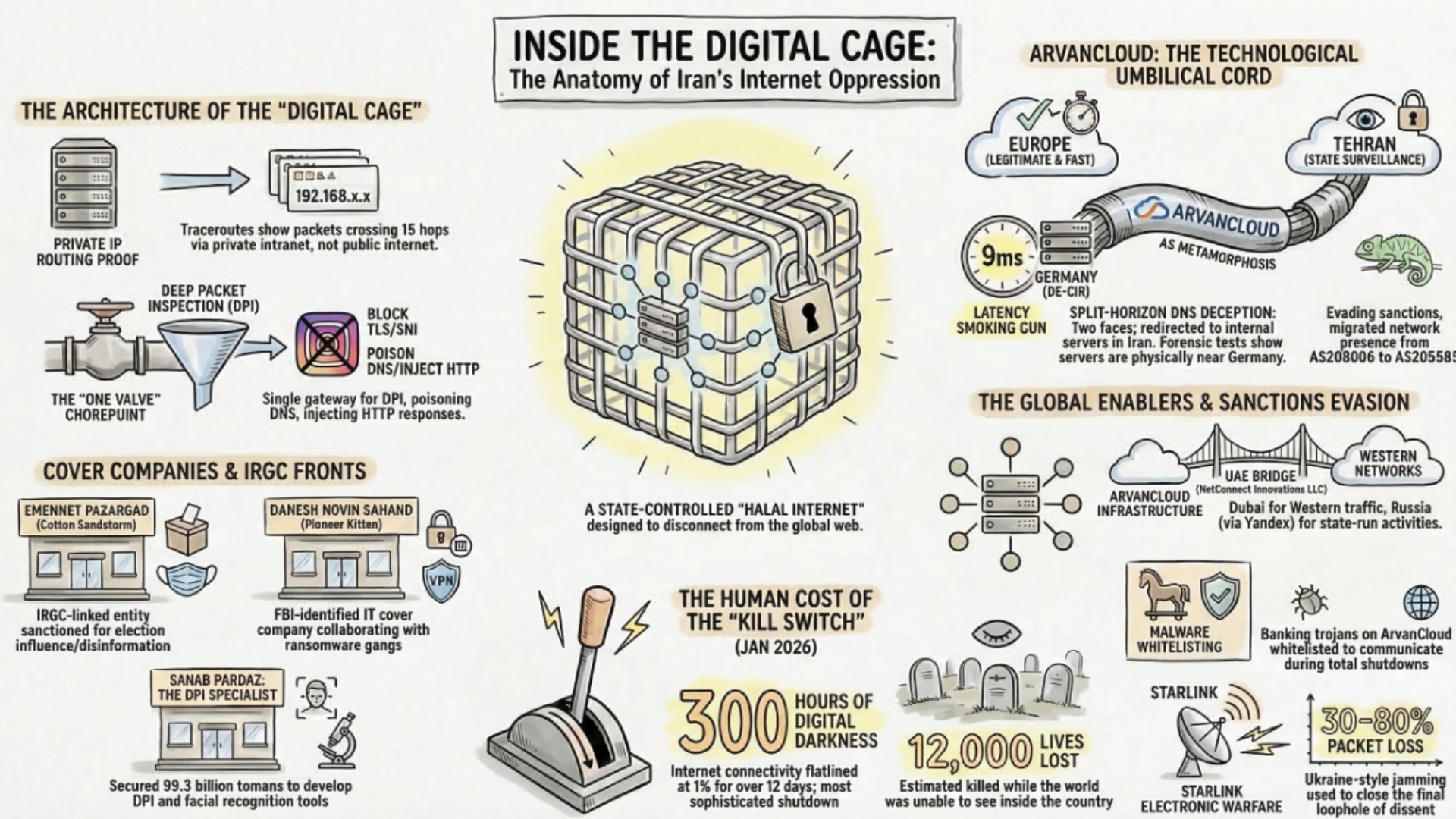
ArvanCloud and Iran’s Digital Oppression Infrastructure
Forensic investigation reveals how ArvanCloud (Noyan Abr Arvan) serves as a critical enabler of Iran’s National Information Network — the regime’s digital cage. BGP routing analysis, latency measurements, and traceroute data expose split-horizon DNS manipulation,…
·
·
17–26 minutes -
CyberStrikeAI: Chinese-Linked AI Attack Platform Compromises 600+ FortiGate Devices Across 55 Countries
An open-source AI-native offensive security tool called CyberStrikeAI, developed by a Chinese coder with ties to the Ministry of State Security, has been deployed by a Russian-speaking threat actor to compromise over 600 FortiGate appliances…
·
·
12–18 minutes -
Cyber & Electronic Warfare · Cyber News & Updates · Digital Espionage & Intelligence · IranRevolution2026 · Operations & Campaigns
Iranian Revolution 2026: Complete Intelligence Briefing — Protests, War, Cyber Operations, and the Fall of Khamenei
Comprehensive intelligence briefing on the Iranian Revolution of 2026 — from the December 2025 protest eruption and regime massacres, through Operation Epic Fury and Operation Roaring Lion, the assassination of Khamenei, the Strait of Hormuz…
·
·
31–46 minutes -
Critical Vulnerability Triage Playbook: How SOCs Prioritize and Patch Critical CVEs
Vulnerability triage: Practical steps SOCs use to prioritize critical CVEs, assign risk, and speed safe patching.
·
·
5–7 minutes -
CISA Adds Two Roundcube Flaws to KEV: What Organizations Must Do
CISA has added two actively exploited Roundcube vulnerabilities to its Known Exploited Vulnerabilities catalog. This post explains the risk, detection steps, and remediation guidance for admins.
·
·
2–3 minutes