Search results for: “network security”
Showing results matching your search
Refine your search
-
Critical Security Flaw Discovered in TOZED ZLT T10 Routers, Threatening Network Stability
A significant security vulnerability, identified as CVE-2025-12917, has been found in specific TOZED ZLT T10 network devices, creating a pathway for attackers to launch denial-of-service attacks. The flaw, which affects the device’s core operational stability,…
·
·
2–3 minutes -
US Agencies Propose Ban on TP-Link Networking Devices Over Security Concerns
The US government is reportedly considering a ban on TP-Link networking devices due to national security concerns, following an investigation by federal agencies. This move could significantly impact the consumer networking market, given TP-Link’s dominant…
·
·
2–3 minutes -
Strait of Hormuz Closure Threatens Global Food Security
The closure of the Strait of Hormuz has disrupted the global supply of urea, a key fertilizer, creating a crisis that could lead to widespread food shortages.
·
·
2–3 minutes -
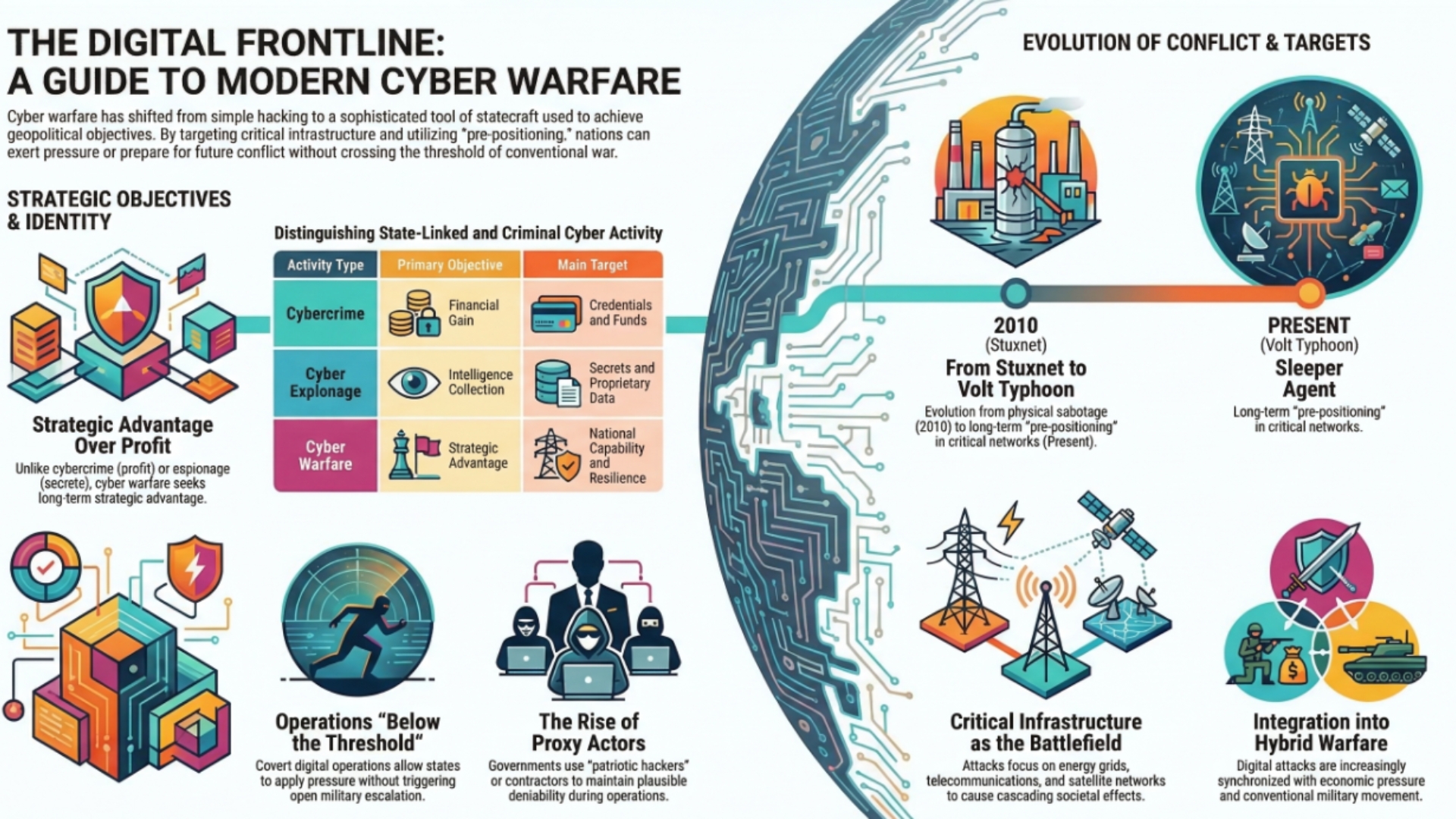
Why Cyberwarfare Forces Firms to Scan Networks Early
The March 2026 cyber alerting around Greek firms showed why cyberwarfare pressure often appears first as defensive scanning, hardening, and spillover preparation rather than immediate visible disruption.
·
·
3–5 minutes -
Top 10 Cyber Escalation Risks Security Leaders Should Understand
A practical evergreen guide to the 10 cyber escalation risks security leaders should understand, with a focus on signaling failure, cumulative pressure, thresholds, and conflict dynamics.
·
·
5–7 minutes -
Top 10 CVE Sources Security Teams Should Check After Reading a CVE
A practical evergreen guide to the 10 reference sources defenders should review after reading a CVE entry so they can prioritize patching with better context, exploit evidence, and remediation guidance.
·
·
5–8 minutes -
Top 10 CVE Fields Security Teams Should Review Before Patching
A practical evergreen guide to the 10 CVE record fields and supporting data points defenders should review before deciding how urgently a vulnerability needs patching.
·
·
5–8 minutes -
Top 10 CVE Items Security Teams Should Patch First in 2026
A defender-focused guide to the 10 types of CVE items that deserve urgent patch attention, based on known exploitation, exposure, blast radius, and real-world remediation risk.
·
·
6–10 minutes -
Greek Firms Scan Networks as Iran War Raises Cyberattack Risk
Greek shipping, banking, transport, telecom, health, and energy firms have begun scanning their systems after a high-priority advisory from Greece’s National Cybersecurity Authority warned of possible Iran-linked cyber activity tied to the wider regional war.
·
·
1–2 minutes -
Service Account Security: How to Control Privilege, Rotation, Ownership, and Trust Paths
Service account security is more than storing passwords in a vault. This practical guide explains how to control non-human identities, reduce privilege scope, assign ownership, rotate credentials safely, monitor trust paths, and avoid the operational…
·
·
10–15 minutes