A pro-Iran cyber group operating out of Iraq has quietly built one of the most persistent hacktivist operations in the Middle East. Known as the Fatimion Cyber Team (فريق فاطميون الالكتروني), this group has been carrying out DDoS attacks, website defacements, database exfiltrations, and coordinated information operations since August 2023. On March 5, 2026, the group launched its most aggressive campaign to date — a large-scale cyber offensive against Kuwait that took down government portals, the national news agency, the Kuwaiti military website, and the Ministry of Health, while dumping over 23,000 user records from the government-linked ATV application. Flashpoint independently confirmed the DDoS attack on the Kuwait News Agency, tracking the group as part of the broader cyber front of Operation Epic Fury — the US-Israeli military campaign against Iran that began on February 28, 2026.
This is not a fringe group operating in isolation. The Center for Strategic and International Studies (CSIS) has named the Fatimion Cyber Team as a key player in Iran’s coordinated hacktivist ecosystem. SecurityScorecard’s STRIKE team identified the group as one of the standout threat actors in its analysis of 250,000 Telegram messages from over 178 hacking collectives during the June 2025 Israel-Iran twelve-day war. CrowdStrike has observed a surge in claimed activity from Iran-aligned hacktivist groups including Fatimion in the wake of the current conflict.
This investigation is based on a complete export of the Fatimion Cyber Team’s primary Telegram channel, comprising over 5,000 messages spanning from the channel’s creation on August 6, 2023 through March 5, 2026. Every claim, operation, media asset, and organizational pattern documented below is drawn directly from the group’s own communications — cross-referenced against external threat intelligence reporting from Flashpoint, SecurityScorecard, CSIS, and CrowdStrike.
Who Is the Fatimion Cyber Team?
The Fatimion Cyber Team was established on Telegram on August 6, 2023 under the name “فريق فاطميون الالكتروني — Fatimion cyber team.” Within hours, the channel had its name briefly changed to “فريق احتياطي” (backup team) before reverting, suggesting operational security awareness from the outset. The group identifies itself as a volunteer collective of Iraqi Shia hacktivists with no formal state affiliation — a claim it has repeated multiple times when Gulf media linked it to Iranian intelligence agencies.
Despite the volunteer framing, the group’s operational alignment tells a different story. Fatimion consistently amplifies statements from Kataib Hezbollah leadership — particularly its Secretary-General Abu Hussein al-Humaidawi and security official Abu Ali al-Askari. It also cross-posts content from Harakat al-Nujaba, Sabereen News, and other channels within Iran’s “axis of resistance” information ecosystem. This pattern places Fatimion squarely within the coordinated pro-Iran cyber threat landscape described by CSIS as extending “beyond hacktivism.” CSIS analysis specifically names the Fatimion Cyber Team alongside Cyber Fattah and Cyber Islamic Resistance as groups that “conducted reconnaissance, DDoS campaigns, website defacements, and data theft operations coordinated with military developments on the ground” — patterns indicating orchestration rather than organic hacktivist activity.

Operational Timeline: From Iraqi Targets to Regional Cyber Warfare
August-September 2023: Launch and Early Attacks
The group’s first operational claim came within 48 hours of the channel’s creation. On August 8, 2023, Fatimion’s “Special Operations Team” (فريق العمليات الخاصة) announced it had “destroyed the third server of Iraq Post” — an Iraqi government postal service. Subsequent posts from the same week claimed ongoing cyber attacks against Iraqi institutions, accompanied by audio propaganda files titled “سنضربكم أينما نشاء” (We will strike you wherever we wish).

By late August 2023, the group had already experienced its first platform takedowns, with Iraqi National Security and the Ministry of Communications deleting its secondary Telegram channel. Rather than retreating, Fatimion used the takedown as propaganda, pinning the censorship report and issuing threats: “This will not pass without consequence.”
During September 2023, the target set expanded. Fatimion began claiming operations against ISIS-affiliated social media accounts on Twitter, Instagram, and Telegram — framing these as defensive actions against Takfiri extremists. The group also launched what it called an anti-blackmail bot, offering to find and delete leaked personal photos and videos while extracting information about the publishers.
October 2023-Early 2024: Pivot Toward Israel and the Broader Region
Following the outbreak of hostilities in October 2023, Fatimion rapidly expanded its target set. The group announced attacks against Israeli infrastructure with the hashtag #الكيان_الصهيوني_يحتضر (The Zionist entity is dying) and claimed to have breached internal Israeli systems. Arab states normalizing ties with Israel also became targets, marking a significant escalation from local Iraqi operations to regional cyber warfare.

Throughout late 2023 and into 2024, the channel alternated between claims of offensive cyber operations and practical community services. Bot infrastructure — particularly @Fatimion313_bot — offered account recovery, technical support, and platform issue assistance for followers within the resistance axis. Giveaways, alternative channel announcements, and pinned messages maintained audience retention even as platforms repeatedly shut down Fatimion’s accounts.
Mid-2024: Battlefield Messaging and Escalation
By mid-2024, Fatimion’s messaging had evolved to include real-time battlefield claims. Posts referenced missile and drone strikes against targets in Eilat, Haifa, Tel Aviv, and US military installations like the Conoco base in Deir ez-Zor, Syria. The channel served as both a cyber operations bulletin board and an amplifier for kinetic military claims from allied groups — blurring the line between cyber and physical warfare in its messaging. This dual role mirrors the operational model of other regional hacktivist groups tracked by CyberWarZone, though Fatimion’s integration with militia networks makes it significantly more dangerous than typical DDoS-focused collectives.
Sabereen News, a well-known pro-militia Iraqi Telegram channel, regularly had its content forwarded by Fatimion. Content from “المدعي العام” (The Prosecutor) and “اناشيد المقاومة” (Resistance Nasheeds) was also cross-posted, reinforcing the interconnected nature of the pro-Iran information ecosystem.

Late 2025: Technical Evolution and Data Leak Operations
By November 2025, Fatimion demonstrated increasing technical sophistication. The channel published detailed OPSEC guidance for followers, including explanations of Wi-Fi Sensing technology, router security hardening (WPA3, transmit power reduction, RF shielding film, Hidden SSID), and warnings about surveillance via compromised routers. One notable thread alleged that Israel had planted modified routers in Beirut’s southern suburbs for intelligence collection — a claim the group framed as a “cyber analysis by Fatimion’s team.”
The group also waded into Iraqi domestic politics. It called for no second term for Prime Minister al-Sudani, questioned government officials’ loyalty, and accused members of Iraq’s digital transformation team of promoting normalization with Israel. When the Iraqi National Security Service arrested individuals responsible for leaking Iraq’s national database, Fatimion covered the story extensively, positioning itself as both watchdog and enforcer.
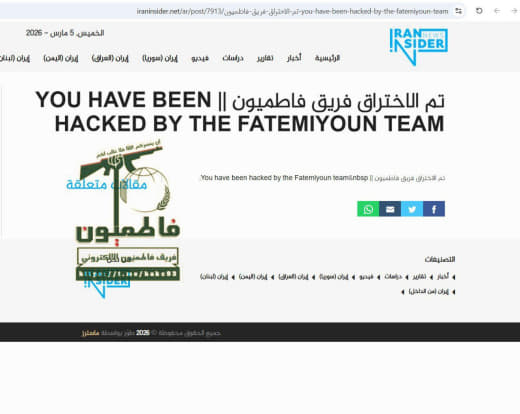
In December 2025, the group claimed to have breached databases belonging to Syria’s post-Assad transitional government, including Ministry of Transport data and mapping systems. Around the same time, Fatimion’s X (Twitter) account — with 30,000 followers — was deleted at what the group described as a government request. After five days of communication with the platform, the team claimed it successfully recovered the account — an unusual feat that suggests social engineering capability.
January-March 2026: Iranian Opposition Hacks and the Kuwait Campaign
On January 9, 2026, Fatimion announced a cyber attack against Iranian opposition media outlets, which it described as “run by Zionist intelligence agencies.” The group claimed to have hacked news agencies that operate from abroad to spread “chaos and incitement” within Iran — a move consistent with the broader pattern of cyber warfare surrounding the Iranian Revolution of 2026. This operation earned 321 paid reactions — the highest recorded in the channel’s history — suggesting significant supporter mobilization. The timing was no coincidence: Iran was under a nationwide internet blackout at the time, and pro-regime hacktivist groups were mobilizing to counter opposition narratives online.

The most significant activity in the dataset occurred on March 5, 2026. In a rapid-fire sequence of over 30 messages posted within two hours, Fatimion claimed a coordinated cyber offensive against Kuwait. Targets included:
- The Kuwait News Agency (KUNA) — taken offline
- The Kuwaiti National Assembly (parliament) website
- The Kuwaiti Army’s official website
- The Ministry of Health website
- Kuwait’s e-government digital portal
- The ATV Kuwaiti state television application — from which 23,553 user records were exfiltrated and published in three PDF files (names, emails, passwords, phone numbers)
Fatimion also claimed access to data of 40,000 Kuwaiti citizens after breaching a government system, and announced it would continue publishing databases. Kuwait reportedly declared a state of cyber alert in response, with Sabereen News and other allied channels confirming the attacks originated from the Iraqi group.
On the same day, the group referenced a Flashpoint intelligence report that attributed a DDoS attack on the Kuwait News Agency to the Fatimion Cyber Team, citing confirmation from IEN (Industrial Equipment News) — demonstrating the group’s awareness of international threat intelligence coverage. Flashpoint’s own Operation Epic Fury tracker independently confirmed this, listing the “Fatemiyoun Electronic Team” as having “conducted a denial-of-service attack against the Kuwaiti News Agency website” and separately noting the group “claimed disruption targeting Gulf states perceived as US-aligned, including Bahrain and Qatar-linked targets.”
The Kuwait campaign did not occur in a vacuum. It unfolded during Operation Epic Fury — the US-Israeli military campaign launched against Iran on February 28, 2026 following the killing of Supreme Leader Khamenei. As kinetic strikes hit Iranian missile sites and Tehran’s state apparatus, Iran’s hacktivist proxy network activated across the cyber domain. Flashpoint tracked a coordinated #OpIsrael campaign involving pro-Iranian and pro-Russian actors, with Fatimion specifically targeting Gulf states that host US military bases — Kuwait being among them, with Camp Arifjan and Ali Al Salem Air Base both having been targeted by Iranian missile strikes days earlier.
Organizational Structure and Infrastructure
Internal Divisions
Fatimion operates with at least two named internal units visible in its communications:
- Special Operations Team (فريق العمليات الخاصة): responsible for offensive cyber operations including DDoS, defacement, and data exfiltration. Claims of server destruction, database theft, and site takedowns are consistently attributed to this unit.
- Intelligence Team (الفريق الاستخباري لفاطميون): produces investigative video content, including reports on Israeli presence in Iraqi Kurdistan and alleged Mossad-linked intelligence services operating in Erbil.
Bot and Automation Infrastructure
The group maintains dedicated Telegram bots that serve multiple functions:
- @Fatimion313_bot: originally promoted for technical support, platform issue assistance, and account recovery services.
- @Fatimion310_bot: the current primary contact bot, through which supporters who donate via Telegram Stars can receive free services including app activations, cyber consultations, server rentals (16GB RAM Linux servers for one month), and IT support.
- An anti-blackmail bot announced in August 2023 that locates and deletes leaked personal media while extracting publisher identities.
Channel Resilience and Redundancy
Fatimion maintains multiple Telegram channels as backup infrastructure, anticipating platform takedowns. The group has cycled through at least three known channel links (t.me/hak993, t.me/hkr313, and a private invite link) and has issued repeated guidance to followers about where to migrate when channels are removed. Content restrictions are sometimes temporarily applied to avoid mass-reporting, then lifted once the threat passes.
Propaganda and Information Operations
Audio and Video Assets
One of the most distinctive features of Fatimion’s operation is its systematic reuse of audio propaganda. A limited set of nasheeds (religious/military songs) are reposted continuously, sometimes daily, across the channel’s entire lifespan. Key assets include:
- “سنضربكم أينما نشاء” (We will strike you wherever we wish) — a 46-second audio clip circulated from the channel’s first week through 2025
- “وعد الآخرة” (Promise of the Hereafter) — produced by the Fatimion team, reposted during escalation periods
- “نحن جنود العباس” (We are the soldiers of al-Abbas) — sourced from Sabereen News
- “حي على الحرب” (Come to war) — the most recently shared audio, posted March 5, 2026 alongside the Kuwait campaign
Archival video compilations from 2019 and 2020 are periodically republished to demonstrate operational longevity. These include claimed operations against Mossad-linked platforms, embassy-connected “electronic armies,” and Zionist media outlets. Newer video production includes professionally edited tributes to martyred commanders and documentary-style “intelligence reports” about alleged Israeli activities in Kurdistan.
Religious and Ideological Framing
The group’s name derives from the Fatimiyya tradition in Shia Islam, referencing Lady Fatima al-Zahra. Messaging consistently ties cyber operations to religious duty, with slogans like “نحن ابناء فاطمة الزهراء” (We are the children of Fatima al-Zahra) and hashtags such as #فاطميون_حتى_الظهور (Fatimion until the Appearance — referring to Shia eschatology). Quranic verses and hadiths accompany major operational claims, framing attacks as divinely sanctioned resistance.
Martyr commemorations form a significant portion of channel content. The assassination of Qasem Soleimani and Abu Mahdi al-Muhandis is referenced annually, and tributes to fallen fighters — including figures like Haitham Ali al-Tabatabaei, Muhammad Afif, and others — are posted with high-production video content that generates some of the channel’s highest engagement metrics.
Engagement Metrics and Audience Analysis
Across 5,035 messages, Fatimion consistently maintains high engagement. Posts regularly receive 80 to 200+ emoji reactions, with peak posts exceeding 300 reactions. The introduction of Telegram’s paid reactions (Stars) in late 2025 revealed a monetized supporter base, with some posts receiving over 100 paid reactions. The January 2026 Iranian opposition hack received 321 paid reactions — the dataset’s highest figure — indicating significant mobilization during offensive operations.
Common reaction patterns show audience alignment with the group’s messaging: the 🫡 (salute) emoji is heavily used on operational claims, ❤ dominates commemorative content, 😡 appears on posts highlighting perceived injustice, and 😢 accompanies martyrdom tributes. This consistent emoji distribution across thousands of posts suggests an authentic, ideologically motivated audience rather than bot-driven engagement.
Network Connections and Allied Groups
The Telegram export reveals a tightly integrated information network. Fatimion regularly forwards content from and amplifies the following channels:
- Sabereen News (صابرين نيوز): one of the most prominent pro-militia Iraqi Telegram channels; confirmed Fatimion’s Kuwait attack
- Shia Shield (الدرع الشيعي): a channel focused on exposing perceived threats to the Shia community; content frequently cross-posted
- Kaf (كاف): shared martyrdom announcements forwarded by Fatimion in March 2026
- Abu Ali al-Askari’s statements: the security official of Kataib Hezbollah, whose political and military directives are treated as authoritative by the channel
The relationship with Kataib Hezbollah deserves particular attention. Fatimion published the full text of a January 5, 2026 statement by Secretary-General al-Humaidawi — a lengthy political address covering Iraqi sovereignty, weapons policy, and regional security. Publishing such statements in full, rather than excerpting, suggests a closer operational relationship than the group publicly acknowledges.
Flashpoint’s March 2026 tracking of Operation Epic Fury’s cyber dimension places Fatimion within a broader coalition of active threat groups. During the same period, NoName057(16) — a pro-Russian group — joined with Cyber Islamic Resistance in a coordinated #OpIsrael campaign targeting Israeli defense and municipal entities. The Handala Team claimed a breach of Saudi Aramco infrastructure.
The FAD Team (described as Iraq’s “Resistance Hub”) conducted SQL injection attacks and PII exposure across US and non-US targets. PalachPro signaled coordination with Iranian hackers. Fatimion’s Kuwait offensive was one front in this multi-group, multi-country cyber campaign — a level of coordination that underscores the organized nature of the threat.
Threat Assessment: What Makes Fatimion Dangerous
The Fatimion Cyber Team represents a distinct category within the pro-Iran cyber threat landscape. Unlike state-sponsored APT groups such as APT42 or APT34, Fatimion operates as a hacktivist-militia hybrid — combining the ideological motivation and public visibility of hacktivism with the organizational backing and target selection of state-aligned militias. As cybersecurity leaders have warned, these groups represent an increasingly dangerous threat precisely because they operate in a gray zone between state direction and independent action.
That gray zone is precisely what makes attribution — and response — so difficult. CrowdStrike’s Adam Meyers noted in March 2026 that while his firm had “observed a surge in claimed activity from Iran-aligned and sympathetic hacktivist groups,” much of the activity was “claim-driven rather than evidence-backed.” Google Threat Intelligence Group’s John Hultquist warned that Iran would target “the U.S., Israel, and Gulf Cooperation Council countries with disruptive cyberattacks,” cautioning that Iran “frequently fabricates and exaggerates” attack effects to boost psychological impact. In Fatimion’s case, however, the Telegram data reveals both genuine capabilities and a pattern of exaggeration — making independent verification of each claim essential.
Several capabilities stand out from the dataset:
- Database exfiltration at scale: the March 2026 Kuwait operation demonstrated the ability to breach government-connected applications and extract tens of thousands of user records including passwords
- Multi-target coordination: the Kuwait campaign hit at least six distinct government targets within a two-hour window, suggesting pre-planned infrastructure and possible botnet resources
- Cross-domain operations: Fatimion simultaneously conducts offensive cyber operations, OPSEC training for followers, intelligence-style reporting, and community services — a breadth unusual for hacktivist groups
- Platform resilience: repeated account deletions on X and Telegram have failed to disrupt operations; the group maintains backup channels and has demonstrated the ability to recover permanently banned accounts
- Operational awareness: the group monitors and shares international threat intelligence reports that mention it, suggesting English-language media monitoring capability
Connection to Iran’s Broader Cyber Operations
While Fatimion claims independence, its operational pattern fits within the broader structure of Iran-aligned cyber operations documented by multiple intelligence firms. The group’s activities align with what CyberWarZone previously reported about Iran’s use of proxy cyber groups to maintain plausible deniability while projecting force in the digital domain.
Its targeting priorities mirror Iran’s geopolitical interests: Iraqi domestic opponents, Israeli infrastructure, Arab states normalizing relations with Israel, Iranian opposition media, and Gulf states perceived as hostile to the resistance axis. The consistent amplification of Kataib Hezbollah leadership statements — a group widely understood to receive Iranian support — further undermines the volunteer narrative. CSIS research details how Iran has increasingly deputized hacktivist proxies in state actions without state attribution, and the CyberAv3ngers case — where US Treasury sanctioned IRGC officials who had posed as hacktivists — demonstrates that the progression from “volunteer hacktivist” to confirmed state proxy is a well-documented pattern in the Iranian context.
SecurityScorecard’s STRIKE team provided perhaps the most compelling structural evidence during the June 2025 twelve-day war between Israel and Iran. Their analysis of 250,000 Telegram messages from over 178 active hacking groups found that the Fatimion Cyber Team was among “several key groups” that stood out in the ecosystem. The research revealed that “the patterns in attack timings, target selection, and exchange of vulnerabilities and attack scripts across groups suggest orchestration rather than organic hacktivist activity” — a finding that directly challenges Fatimion’s self-characterization as independent volunteers.
The Fatimion Cyber Team fits into what analysts describe as Iran’s layered cyber doctrine: the IRGC and MOIS operate state-sponsored APT groups (APT33, APT35 within the IRGC; APT34/OilRig and MuddyWater within the MOIS) for sensitive espionage and destructive operations, while hacktivist proxies like Fatimion handle high-visibility attacks that serve propaganda objectives and test adversary defenses. As CSIS notes, when Iran wants deniability and widespread influence, it uses hacktivist personas; when it needs sophisticated access, it deploys dedicated APT groups. The blurred lines allow resources and intelligence to flow between these layers — a structure Iran has used to scale operations while remaining resilient to disruption. Iranian-linked APT activity such as the SmudgedSerpent campaign targeting US policy experts operates at the sophisticated end of this spectrum, while Fatimion occupies the high-visibility, deniable end.
Indicators of Compromise and Technical Footprint
Based on the Telegram export, defenders and threat intelligence teams should monitor the following indicators associated with the Fatimion Cyber Team:
- Telegram channel IDs: channel1970086460 (primary), with backup channels at t.me/hak993 and t.me/hkr313
- Bot identifiers: @Fatimion313_bot, @Fatimion310_bot
- Attack patterns: DDoS campaigns targeting multiple government subdomains in rapid succession; database exfiltration followed by staged PDF dumps; defacement with Arabic-language messages and religious imagery
- Timing patterns: operations frequently launch during evening hours (Iraqi time) and cluster around politically significant dates — anniversaries of the Soleimani assassination, religious commemorations, and in response to perceived provocations
- Allied amplification channels: Sabereen News (channel1491094605), Shia Shield (channel3148465603), and Kaf (channel1072345716) — attacks claimed by Fatimion are rapidly confirmed and amplified through this network
Conclusion: A Growing Threat That Demands Attention
Over 30 months and more than 5,000 messages, the Fatimion Cyber Team has evolved from an obscure Iraqi Telegram channel into a recognized threat actor cited by Flashpoint, CSIS, SecurityScorecard, CrowdStrike, and Google Threat Intelligence Group. Its March 2026 campaign against Kuwait — involving simultaneous DDoS attacks on government infrastructure and the public release of stolen databases, independently confirmed by Flashpoint’s Operation Epic Fury tracking — represents a significant escalation in both capability and ambition.
The group’s combination of offensive cyber operations, community services, OPSEC education, and deep ideological integration with Iran’s resistance axis makes it more than a typical hacktivist collective. For cybersecurity defenders in the Middle East and beyond, understanding Fatimion’s operational patterns, infrastructure, and network connections is essential for anticipating and mitigating the next wave of attacks.
Organizations in the Gulf region, particularly government agencies and media outlets, should treat the Fatimion Cyber Team as an active and persistent threat. The data examined for this article leaves no doubt: this group is operational, expanding its capabilities, and showing no signs of slowing down.
This analysis is based on a complete Telegram channel export containing 5,035 messages from August 2023 through March 2026. All claims attributed to the Fatimion Cyber Team are sourced directly from the group’s own communications and have not been independently verified unless otherwise noted.