Search results for: “ransomware”
Showing results matching your search
Refine your search
-
INTERPOL operation takes down 45,000 malicious IPs and leads to 94 arrests
INTERPOL says Operation Synergia III dismantled more than 45,000 malicious IP addresses and servers used in phishing, malware, and ransomware activity, resulting in 94 arrests across 72 countries and territories.
·
·
2–3 minutes -
Threat actors mass-scan Salesforce Experience Cloud using modified AuraInspector tool
Salesforce says threat actors are increasingly targeting publicly accessible Experience Cloud sites with a customized AuraInspector tool to exploit overly permissive guest-user configurations and gain access to sensitive information.
·
·
1–2 minutes -
China-linked UAT-9244 used TernDoor, PeerTime, and BruteEntry in South American telecom attacks
Cisco Talos says China-linked threat actor UAT-9244 has targeted telecommunications providers in South America since 2024, using the TernDoor, PeerTime, and BruteEntry implants across Windows, Linux, and edge devices in a campaign it says is…
·
·
1–2 minutes -
Stryker Cyberattack: Iran-Linked Handala Claims Wiper Attack
Iran-linked Handala claims a wiper attack on Stryker, with early reports pointing to possible Microsoft Intune abuse and major operational disruption.
·
·
4–7 minutes -
Volt Typhoon: China’s Critical Infrastructure Pre-Positioning Campaign
Volt Typhoon is a China-linked intrusion campaign that U.S. agencies say targeted communications, energy, transportation, and water systems while using stealthy living-off-the-land tradecraft and compromised routers to hide its activity.
·
·
6–9 minutes -
What Is Cyber Warfare? Definition, Doctrine, and Real-World Examples
Cyber warfare refers to state-driven digital operations designed to disrupt, spy on, or damage an adversary’s infrastructure, military systems, or decision-making capabilities.
·
·
14–21 minutes -
UAT-10027 Targets U.S. Healthcare with Dohdoor Malware Using DoH C2
Researchers have uncovered a previously undocumented cyber campaign tracked as UAT-10027 targeting U.S. healthcare and education organizations with a new backdoor called Dohdoor that uses DNS-over-HTTPS to evade detection and deploy Cobalt Strike beacons.
·
·
4–6 minutes -
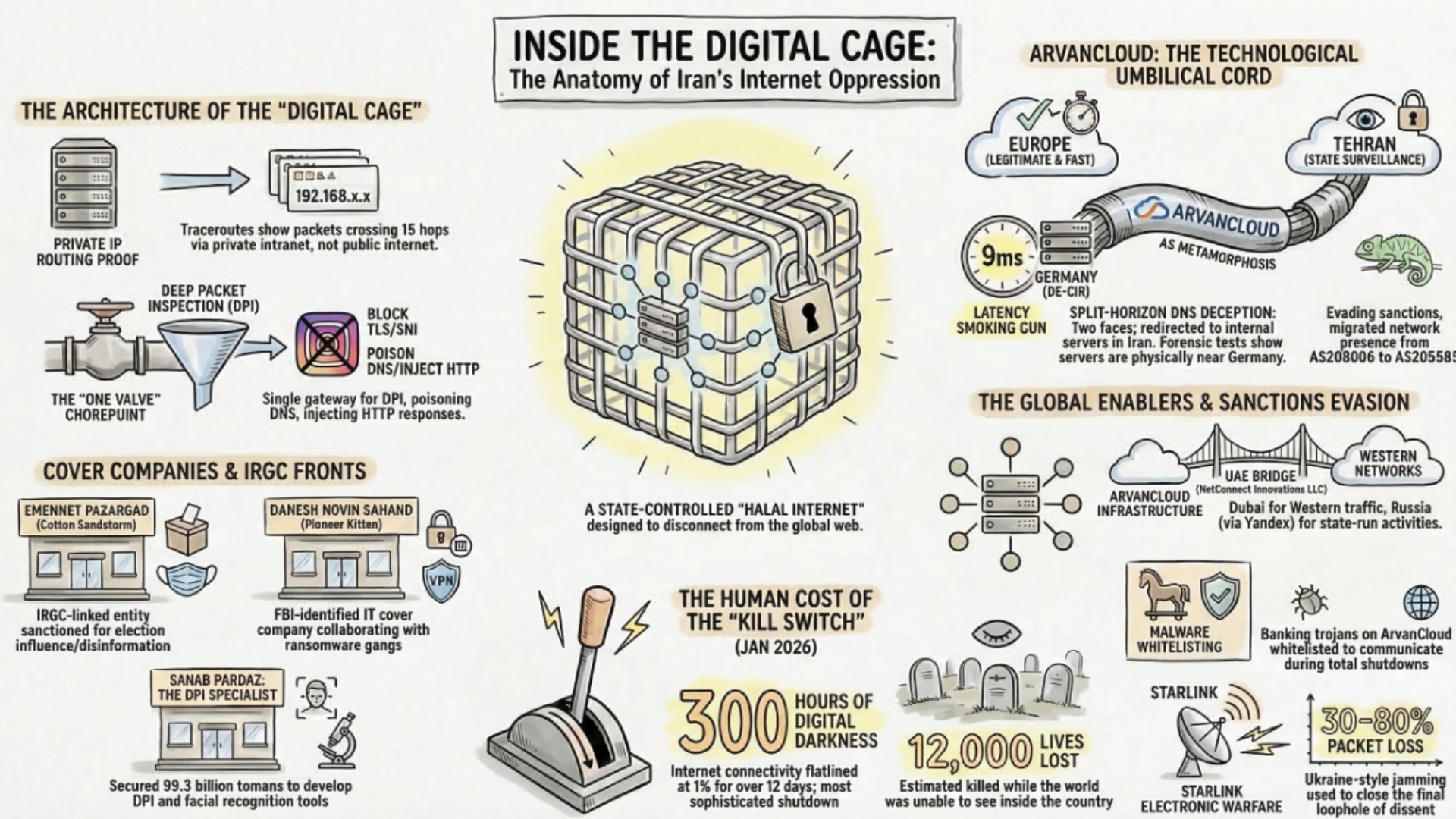
ArvanCloud and Iran’s Digital Oppression Infrastructure
Forensic investigation reveals how ArvanCloud (Noyan Abr Arvan) serves as a critical enabler of Iran’s National Information Network — the regime’s digital cage. BGP routing analysis, latency measurements, and traceroute data expose split-horizon DNS manipulation,…
·
·
17–26 minutes -
CyberStrikeAI: Chinese-Linked AI Attack Platform Compromises 600+ FortiGate Devices Across 55 Countries
An open-source AI-native offensive security tool called CyberStrikeAI, developed by a Chinese coder with ties to the Ministry of State Security, has been deployed by a Russian-speaking threat actor to compromise over 600 FortiGate appliances…
·
·
12–18 minutes -
Cyber & Electronic Warfare · Cyber News & Updates · Digital Espionage & Intelligence · IranRevolution2026 · Operations & Campaigns
Iranian Revolution 2026: Complete Intelligence Briefing — Protests, War, Cyber Operations, and the Fall of Khamenei
Comprehensive intelligence briefing on the Iranian Revolution of 2026 — from the December 2025 protest eruption and regime massacres, through Operation Epic Fury and Operation Roaring Lion, the assassination of Khamenei, the Strait of Hormuz…
·
·
31–46 minutes