Search results for: “law enforcement”
Showing results matching your search
Refine your search
-
ThreatsDay Bulletin: AI Malware, Voice Bot Flaws, Crypto Laundering, IoT Attacks — and 20 More Stories
This week’s cybersecurity bulletin highlights the re-emergence of Mirai-based botnets targeting IoT devices, a surge in sophisticated phishing attacks leveraging AI, and efforts by Singapore to curb government impersonation scams. It also covers privacy upgrades…
·
·
2–3 minutes -
What is Operation Endgame?
Operation Endgame is a major international law enforcement initiative aimed at disrupting and dismantling significant cybercrime infrastructure globally, targeting widespread malware families, botnets, and other illicit tools.
·
·
2–3 minutes -
Russian Initial Access Broker Pleads Guilty in US for Yanluowang Ransomware Attacks
A Russian initial access broker (IAB) pleaded guilty in the United States for facilitating at least seven Yanluowang ransomware attacks, demanding $24 million from American organizations. This case highlights the crucial role of IABs in…
·
·
1–2 minutes -
Domestic Breach Prompts Russian Crackdown on Meduza Stealer Group
Russian law enforcement detained three individuals on October 30, 2025, suspected of developing and selling the Meduza Stealer malware, following an investigation prompted by a breach of a Russian government organization. These arrests in Moscow…
·
·
2–3 minutes -
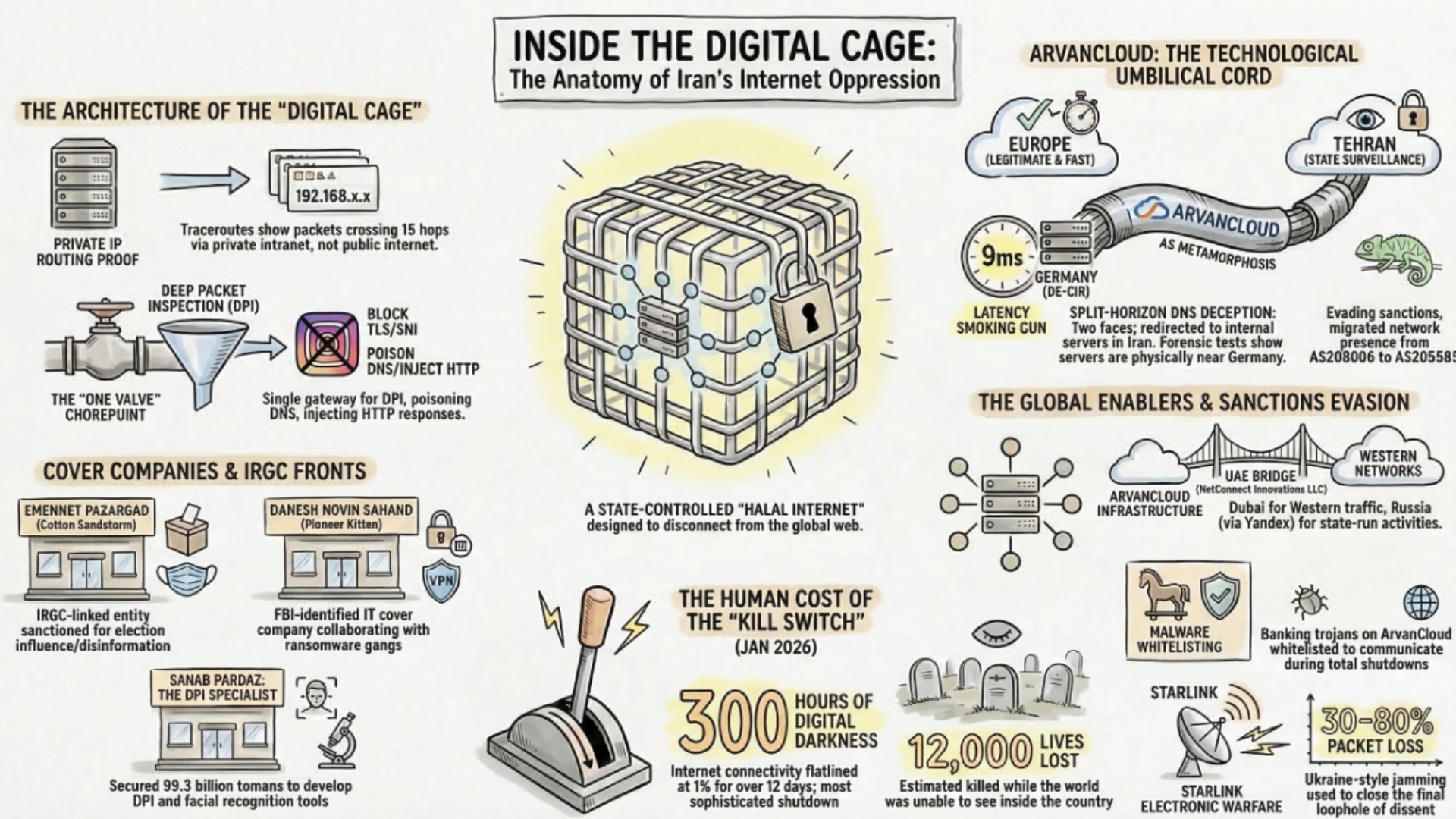
Cyber & Electronic Warfare · Digital Espionage & Intelligence · IranRevolution2026 · Operations & Campaigns
Iran Cyberwar Shifts to Spillover, Retaliation, and Control
The cyber dimension of the Iran war is no longer limited to isolated attacks. From internal repression and internet shutdowns to suspected Iran-linked retaliation abroad, a multi-layered cyber conflict is emerging with direct implications for…
·
·
8–12 minutes -
INTERPOL operation takes down 45,000 malicious IPs and leads to 94 arrests
INTERPOL says Operation Synergia III dismantled more than 45,000 malicious IP addresses and servers used in phishing, malware, and ransomware activity, resulting in 94 arrests across 72 countries and territories.
·
·
2–3 minutes -
Aeternum C2 Botnet Abuses Polygon Blockchain to Hide Malware Commands and Evade Takedowns
Security researchers have uncovered a new botnet loader called Aeternum C2 that stores encrypted command-and-control instructions on the Polygon blockchain, making traditional takedown efforts significantly harder and signaling a new evolution in resilient malware infrastructure.
·
·
4–6 minutes -
Dutch Police Hack iPhones: Unpacking Real-Time Surveillance Capabilities
Recent reports from AD and Security.NL reveal that Dutch police have employed advanced hacking techniques to gain real-time access to suspects’ iPhones. This unprecedented level of surveillance allows law enforcement to monitor a suspect’s phone…
·
·
3–5 minutes -
Resecurity honeypot trap sparks breach debate
Resecurity says the breach claims against it touched only a synthetic-data honeypot, while the attackers insist they stole real records. We break down how the decoy was built, what telemetry it produced, and the controls…
·
·
5–7 minutes -
LastPass Breach Leads to Ongoing Crypto Theft
TRM Labs blockchain investigation links $35+ million in cryptocurrency thefts to the 2022 LastPass breach. Attackers crack master passwords offline, extract private keys, drain wallets via CoinJoin mixing, and launder funds through Russian exchanges.
·
·
7–10 minutes