Lara De Jong
-
Kimsuky and Lazarus Join Forces in Coordinated Attacks
North Korean hacking groups Kimsuky and Lazarus combine forces. They exploit zero-day vulnerabilities in coordinated attacks, targeting critical sectors worldwide. This marks a shift in state-sponsored threat operations.
·
·
1–2 minutes -
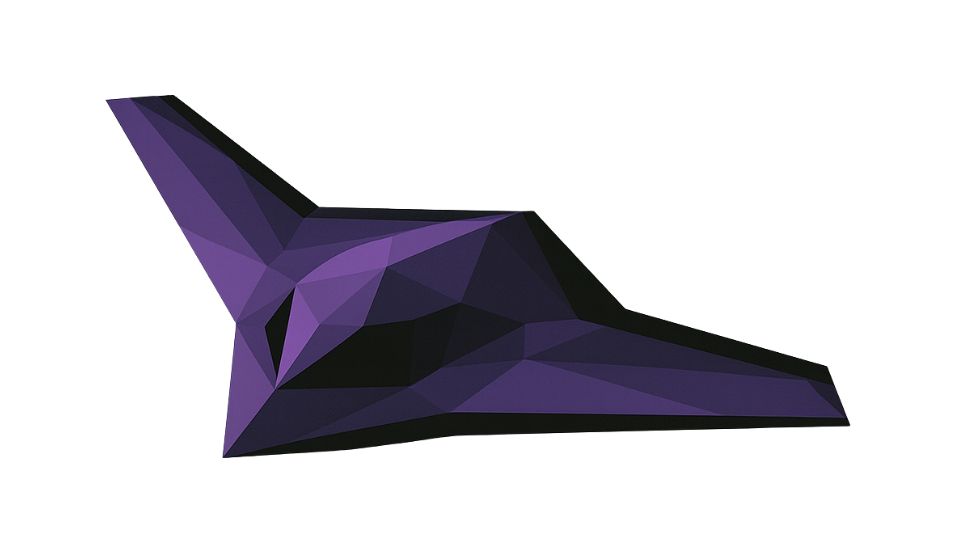
Kratos Opens New Turbojet Engine Production Hub
Kratos Defense opens a new turbojet engine production hub in Michigan. This expansion increases capacity for unmanned aerial systems for the U.S. military and allies. Focuses on affordable mass and…
·
·
2–3 minutes -
ThinPLUS OS Command Injection Vulnerability (CVE-2025-13284)
A critical OS Command Injection vulnerability (CVE-2025-13284) in ThinPLUS allows unauthenticated remote attackers to execute arbitrary commands, posing significant risks to system integrity. TWCERT/CC urges immediate patching.
·
·
2–3 minutes -
IndonesianFoods-worm Floods NPM Registry
A sophisticated self-replicating ‘IndonesianFoods-worm’ has flooded the npm registry with tens of thousands of malicious packages. This aggressive campaign, documented by SourceCodeRed and JFrog, poses a significant threat to the…
·
·
2–3 minutes -
ShadowMQ Flaw Exposes AI Inference Engines to Remote Code Execution
Oligo Security found a recurring ZeroMQ/pickle deserialization flaw affecting multiple AI inference frameworks; several vendors have issued patches.
·
·
2–3 minutes -
Phishing Campaign Targets Travel Websites
A Russian-speaking threat group launched a sophisticated phishing campaign, creating over 4,300 fake travel websites to steal payment information from hotel guests.
·
·
1–2 minutes -
Autonomous Air Systems Explained
Autonomous Air Systems (AAS) advance aerial technology, moving beyond traditional remote-controlled drones to platforms that operate independently. These systems integrate advanced artificial intelligence, machine learning, and sophisticated sensor arrays to…
·
·
2–3 minutes -
Understanding Package Registry Flooding
Package registry flooding is a cyberattack where threat actors overwhelm software package repositories with fake entries to hide malicious content, erode trust, and create vulnerabilities in the software supply chain.…
·
·
3–4 minutes -
FPV Drones in Modern Warfare
Explore the critical role of First-Person View (FPV) drones in modern warfare, their tactical superiority, and their impact on cyber and electronic warfare, including training and counter-drone measures.
·
·
2–4 minutes -
What is Phishing-as-a-Service (PhaaS)?
Phishing-as-a-Service (PhaaS) evolves the cybercrime landscape, mirroring legitimate Software-as-a-Service (SaaS) models. PhaaS offers accessible tools and infrastructure, letting even novices launch sophisticated phishing attacks to steal data and money.
·
·
2–3 minutes