The cyberwar surrounding the Iran conflict has moved beyond isolated website hacks and into something broader, messier, and far more consequential. Since the opening phase of the 2026 escalation, the digital front has developed along three tracks at once: pressure on Iranian digital services and information channels inside the country, retaliatory or claimed retaliatory attacks abroad, and a widening defensive alert posture across healthcare, shipping, finance, logistics, and government networks that fear becoming collateral targets.
That pattern matters because it does not resemble the simplistic “cyber Pearl Harbor” narrative that often dominates public debate. What is unfolding instead is a campaign built on disruption, coercion, and psychological pressure. Apps used by Iranian audiences have been compromised. Internet connectivity inside Iran has dropped sharply during key moments of the war. Iran-linked actors have been publicly tied to destructive or highly disruptive activity abroad. Meanwhile, Western cyber agencies are warning that the greatest immediate risk may be spillover into organizations with regional operations, suppliers, contractors, or exposed endpoint management systems.
This article takes that wider view. Rather than retelling one incident, it maps how the Iran war’s cyber dimension is functioning in practice: as a layered contest involving regime control, external retaliation, infrastructure exposure, and information operations. Attribution still remains uneven in several cases, and some claims by threat actors are impossible to independently verify in real time. But the broader operational picture is clear. The cyber front is no longer peripheral to the conflict. It is now one of the principal ways pressure is being applied, absorbed, and redistributed across borders.
For readers tracking the wider campaign, Cyberwarzone has already documented the CISA warning issued after the Stryker cyberattack and the broader Iran Revolution 2026 intelligence briefing, both of which provide important context for how this cyber front has evolved.
Inside Iran, cyber operations are being used to suppress, disrupt, and control the population
Verified reporting indicates that the first wave of cyber activity during the escalation targeted Iranian-facing digital services. Applications, news platforms, and communication channels experienced compromise or disruption within hours of the initial strikes. At the same time, network monitoring data showed sharp declines in national connectivity, consistent with deliberate restriction or infrastructure stress.
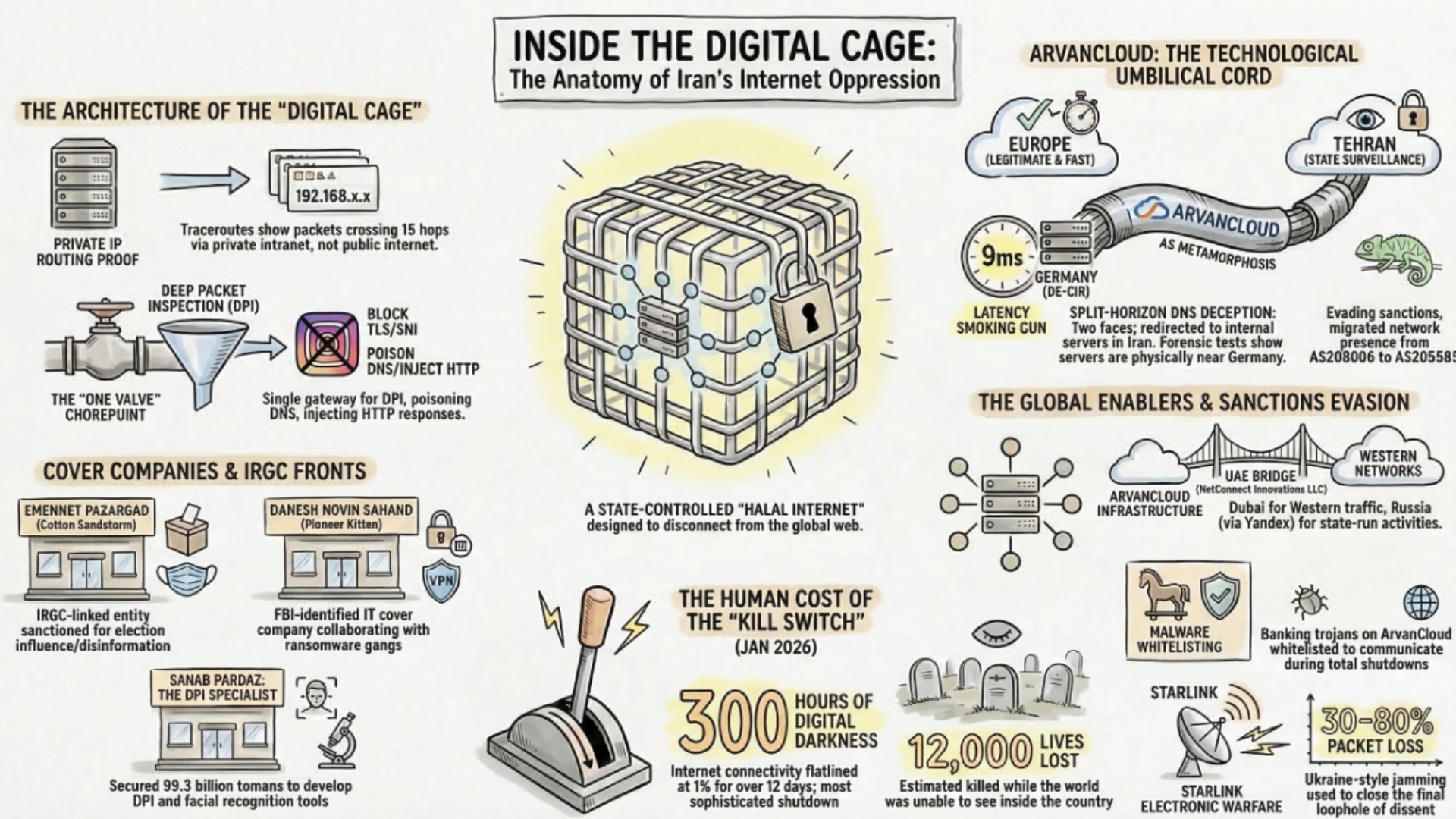
This pattern aligns with how the Iranian regime has historically treated the internet: not as neutral infrastructure, but as a controllable domain. The same systems used to filter, throttle, and monitor traffic during protests are now being leveraged under wartime conditions. The outcome is not just technical disruption. It is informational isolation.
In practical terms, this means civilian populations are cut off from independent reporting, while state-controlled narratives fill the gap. That dynamic is not incidental. It is operational. The regime’s survival model depends on controlling the flow of information during moments of instability. Cyber operations targeting Iranian platforms, combined with regime-imposed restrictions, create a contested information environment where truth becomes difficult to verify in real time.
From an operator’s perspective, this is one of the most overlooked elements of the conflict. Cyber effects inside Iran are not only about attacking infrastructure. They are about shaping perception, limiting coordination among civilians, and reducing the ability of the population to organize or communicate freely under pressure.
Outside Iran, the most serious risk is retaliatory disruption against civilian and commercial targets
The clearest recent example is the March 11 cyberattack on Stryker, a U.S. medical device and services company. Public reporting tied the disruption to the Iran-linked persona Handala, which claimed the operation as retaliation linked to wartime events in Iran. Stryker disclosed global disruption to parts of its Microsoft environment, followed by downstream impact on ordering, manufacturing, and shipping.
That sequence is operationally important. It shows how an attack on enterprise identity, endpoint management, or remote-access workflows can produce immediate real-world disruption without touching connected medical products directly. Hospitals may still feel the impact through delayed deliveries, postponed procedures, and degraded supply-chain visibility. In a conflict setting, that kind of pressure creates headlines, anxiety, and political effect even when the target is not a military system.
This is one reason analysts should avoid reducing the Iran cyberwar to flashy claims of critical infrastructure sabotage. The more plausible and more repeatable play is pressure against civilian-adjacent organizations whose disruption cascades outward. Medical logistics, maritime brokers, airport suppliers, customs platforms, payment processors, and industrial distributors all fit that model. The target is not only data. The target is tempo.
Iran-linked operators and aligned personas have long mixed intrusion, data theft, leak operations, defacement, and destructive activity. What stands out in the current phase is the willingness to claim retaliatory intent in near real time. That public signaling turns every attack into both an operational event and an information operation, amplifying fear well beyond the initial victim.
Spillover risk is now the defining feature of the Iran cyberwar
Government advisories and incident-response reporting point in the same direction: the most immediate danger is not a single catastrophic attack, but distributed spillover across organizations indirectly tied to the region. Companies with suppliers, partners, cloud dependencies, or personnel linked to Middle Eastern operations are now operating inside an expanded threat surface.
This risk is amplified by the technical pathways being used. Endpoint management systems, identity platforms, and remote administration tooling create high-leverage entry points. When compromised, they allow attackers to move laterally at speed, disrupt operations, and in some cases deploy destructive payloads or simulate them through access denial. The Stryker case, combined with subsequent hardening guidance from U.S. authorities, highlights how enterprise IT—not industrial control systems—can be the initial point of failure.
One operational mistake organizations repeatedly make is assuming geographic distance provides safety. In practice, supplier relationships, shared SaaS environments, and federated identity models erase that boundary. A logistics partner in the Gulf, a development team with regional access, or a managed service provider operating across jurisdictions can all serve as indirect exposure points.
Another overlooked failure scenario involves over-reliance on detection over containment. In fast-moving campaigns, by the time alerts are triggered, attackers may already have persistence across multiple systems. The organizations that recover fastest are those that can isolate identity systems, revoke tokens, and rebuild trust chains quickly—not those that rely solely on perimeter monitoring.
For defenders, the implication is clear. The Iran cyberwar is not something to observe from a distance. It is something to model operationally inside your own environment. That means mapping dependencies, stress-testing identity infrastructure, and preparing for disruption that may arrive through partners rather than direct targeting.
Cyber operations are being paired with psychological warfare and narrative shaping
One of the defining features of the current phase is how closely technical intrusion is tied to messaging. Groups claiming alignment with Iranian interests or opposition to them are not operating quietly. They are publishing claims, releasing screenshots, naming targets, and framing attacks as retaliation or resistance in near real time.
This behavior changes the impact profile of each incident. A disruption that might otherwise remain contained inside a corporate network becomes a public signal. The claim itself becomes part of the operation. In the Stryker case, for example, the attribution claim and its timing amplified the perceived scale and intent of the attack, regardless of the still-limited public technical detail about the payload.
There is also a second layer that receives less attention: false or exaggerated claims. In previous Iran-linked campaigns, operators have blended real intrusions with inflated narratives to create strategic confusion. That creates a verification gap for defenders, journalists, and governments. Overreaction can be as damaging as underreaction, particularly when critical infrastructure operators are forced to make rapid decisions under uncertainty.
Inside Iran, the same dynamic intersects with state control. External cyber incidents, internal restrictions, and state messaging all feed into a single contested information space. Civilians receive fragmented, delayed, or manipulated information, while external observers struggle to distinguish verified incidents from influence operations.
The result is a cyber battlespace where perception is actively managed alongside access. Technical compromise and narrative control are no longer separate domains. They are executed together, often by the same actors or within the same campaign cycle.
The operational reality: fragmented attacks, exaggerated claims, and real-world consequences
Recent verified incidents and threat intelligence reporting show a consistent pattern: disruption is real, but claims are often inflated. The March 11 attack on Stryker disrupted ordering, manufacturing, and logistics systems across a global enterprise, with the company confirming operational impact but no compromise of patient devices or services. At the same time, the group claiming responsibility asserted large-scale data destruction and exfiltration figures that remain unverified.
This gap between confirmed impact and claimed impact is not noise. It is part of the operating model. Iran-linked personas such as Handala blend intrusion with narrative amplification. They publish screenshots, logos, and statements designed to extend the perceived reach of an attack. In some cases, destructive techniques such as wiper-style behavior are used. In others, access disruption alone is enough to create cascading effects across supply chains.
Threat intelligence reporting indicates that dozens of hacktivist groups have become active since the start of the war, many operating with loose alignment to Iranian state interests. These groups rely on phishing, credential theft, remote access tools, and exposed services rather than highly sophisticated zero-day exploitation. The volume of activity creates pressure, even when individual attacks are limited in scope.
One contrarian observation stands out: the most effective operations so far are not the most technically advanced. They are the ones that combine timing, visibility, and operational leverage. Disrupting identity systems, remote management platforms, or internal communications during a high-tension geopolitical moment produces disproportionate impact compared to isolated technical exploits.
For defenders and analysts, this requires a shift in evaluation. The question is no longer whether a single attack is catastrophic. The question is how repeated, overlapping disruptions—some verified, some exaggerated—accumulate into systemic pressure across civilian infrastructure.
What comes next: sustained cyber pressure, not a single decisive strike
Recent developments confirm that the cyber dimension of the Iran war is not converging toward a single high-impact attack. Instead, it is expanding into sustained, distributed pressure across civilian systems. The March 11 attack on Stryker disrupted manufacturing, ordering, and shipping operations globally, while Iran-linked actors publicly framed the operation as retaliation tied to battlefield events. U.S. authorities responded by urging organizations to secure endpoint management systems, highlighting how enterprise IT environments are becoming primary targets rather than traditional critical infrastructure.
At the same time, law enforcement actions such as domain seizures targeting groups like Handala have had limited long-term impact. The group restored its online presence within days, reinforcing a pattern observed across multiple Iran-linked campaigns: infrastructure takedowns slow operations temporarily but do not eliminate capability. This persistence is enabled by decentralized tooling, disposable infrastructure, and a hybrid model combining state direction with proxy execution.
There is also a structural constraint shaping the battlefield. Early cyber operations accompanying the initial strikes disrupted Iranian communications and contributed to widespread connectivity degradation inside the country. That disruption limits the regime’s ability to coordinate large-scale external cyber operations in the short term, even as it continues to repress domestic communication channels. The result is an asymmetric environment where smaller, faster, and more opportunistic attacks dominate.
For defenders, the most realistic scenario is not a sudden collapse of infrastructure, but a prolonged period of instability. Repeated disruptions to supply chains, identity systems, and enterprise platforms create cumulative effects. Each incident may be containable in isolation. Together, they increase operational friction across sectors that depend on continuous availability.
This is the defining characteristic of the current cyberwar. It is not designed to deliver a single decisive outcome. It is designed to apply constant pressure—on systems, on organizations, and on populations already under strain from the broader conflict.