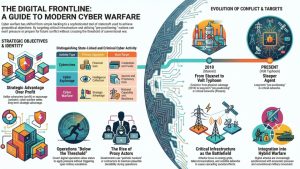
Cyber warfare has become a defining feature of geopolitical competition in the digital age. Governments now rely on cyber operations to gather intelligence, disrupt adversaries, and prepare the digital battlefield long before conventional military conflict begins. Unlike traditional cybercrime, which focuses on financial gain, cyber warfare is tied directly to national strategy, political influence, and military objectives.
State-sponsored cyber operations can target critical infrastructure, government networks, telecommunications systems, and private-sector organizations that support national security or economic stability. These operations may remain hidden for months or years as attackers quietly establish access, collect intelligence, and position themselves to cause disruption when tensions escalate.
For security professionals and analysts, understanding cyber warfare requires more than identifying malware or intrusion techniques. It requires understanding how digital operations fit into broader strategic competition between states.
Cyber warfare is not just about hacking systems—it is about shaping political outcomes, gaining strategic advantage, and weakening an adversary’s ability to respond in times of crisis.

What Cyber Warfare Actually Means
Cyber warfare refers to the use of digital operations by states or state-aligned actors to achieve strategic objectives against an adversary. These operations can involve espionage, disruption, psychological influence, or the degradation of critical infrastructure. Unlike ordinary hacking or financially motivated cybercrime, cyber warfare is tied to national interests and geopolitical competition.
In practice, cyber warfare is rarely a single dramatic attack. Instead, it is usually a sequence of operations designed to create strategic advantage over time. Adversaries may first infiltrate government or corporate networks, quietly collect intelligence, and map infrastructure dependencies. That access can later be used to disrupt services, manipulate information, or support military operations during a crisis.
Cyber warfare operations typically target systems that influence national power. This includes telecommunications infrastructure, satellite networks, energy grids, logistics platforms, defense contractors, and government agencies. Compromising these systems can create leverage during geopolitical disputes without requiring traditional military confrontation.
Because cyber operations can be conducted remotely and covertly, they allow states to apply pressure below the threshold of open conflict. This characteristic makes cyber warfare a persistent tool of state competition rather than a capability used only during wartime.
Cyber Warfare vs Cybercrime vs Cyber Espionage
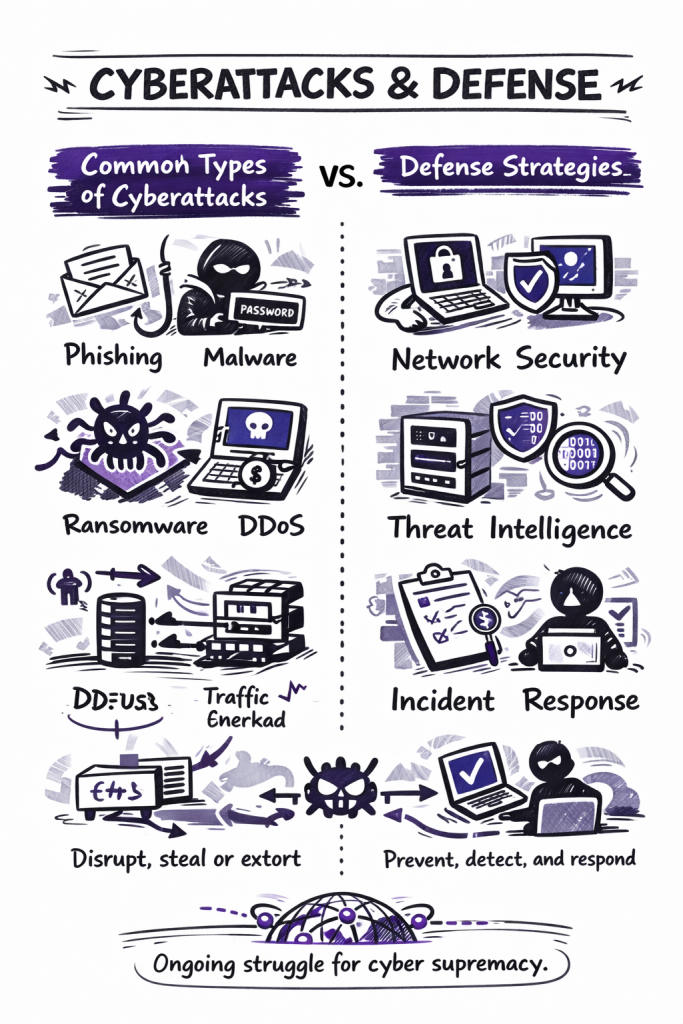
These categories often overlap technically, but they serve different purposes. Cybercrime is usually driven by profit. Threat actors steal credentials, deploy ransomware, drain accounts, or sell access because the objective is financial return. Even when the intrusion is sophisticated, the end goal is typically money rather than strategic state advantage.
Cyber espionage is different. Its purpose is intelligence collection. State-linked operators may compromise ministries, telecom providers, defense contractors, journalists, or dissident networks to steal information quietly over long periods. The operation may never become visible to the public, and the actor may avoid disruption entirely in order to preserve access.
Cyber warfare goes further. It uses digital operations to generate strategic effects tied to conflict, coercion, deterrence, or battlefield preparation. The objective is not merely to steal data or make money. It is to weaken an adversary, shape decisions, impose costs, or prepare conditions for escalation. In that sense, cyber warfare targets capability and resilience rather than just information or revenue.
A useful distinction is this: cybercrime seeks profit, cyber espionage seeks secrets, and cyber warfare seeks strategic advantage. For defenders, this difference matters because the response to a financially motivated intrusion is not the same as the response to a campaign that may be linked to geopolitical pressure or state conflict.
Who Conducts Cyber Warfare
Cyber warfare is usually carried out by state institutions, state-directed contractors, intelligence services, military cyber units, or proxy groups that operate in alignment with national interests. In some cases, governments rely on formal command structures with clear operational discipline. In other cases, they benefit from looser ecosystems of patriotic hackers, front companies, or criminal actors who provide plausible deniability.
Military cyber units often focus on battlefield support, disruption of adversary systems, and operational preparation. Intelligence services typically emphasize access, persistence, espionage, and covert influence. These missions can overlap. A network compromise that begins as intelligence collection may later become the foundation for disruption or sabotage if tensions escalate.
Proxy actors are especially important in modern cyber conflict. A state may not openly claim responsibility for an operation, but it can still benefit from the effects created by affiliated groups. This model complicates attribution and allows governments to pressure rivals without crossing the political threshold associated with overt military action.
For analysts, identifying who benefits from an operation can be as important as identifying the malware or infrastructure involved. Cyber warfare is not defined only by the intrusion itself. It is also defined by the strategic context, the intended effect, and the actor’s relationship to state power.
The History of Cyber Warfare
Cyber warfare evolved gradually as governments recognized that computer networks were becoming both strategic assets and potential targets. Early activity centered on espionage and access operations. Over time, states and state-linked actors expanded those activities into disruption, sabotage, and influence campaigns designed to produce broader strategic effects.
Early Cyber Conflict Incidents
One of the earliest large-scale cyber conflict events occurred in 2007, when Estonia experienced a wave of distributed denial-of-service attacks that hit government institutions, banks, and media outlets. The incident showed how digital operations could disrupt a highly connected society without conventional military force.
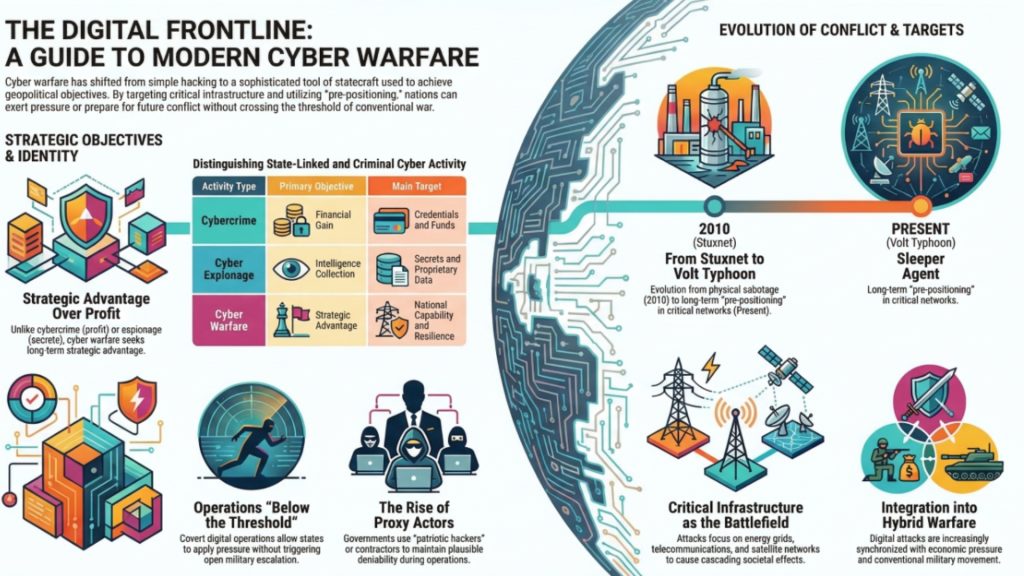
Cyber conflict escalated further with the discovery of Stuxnet in 2010. The malware targeted Iranian nuclear enrichment facilities and physically damaged industrial centrifuges. Stuxnet remains the clearest early example of a cyber operation producing physical effects inside critical infrastructure.
Subsequent incidents reinforced the strategic significance of cyber operations. The 2015 and 2016 attacks against Ukraine’s power grid disrupted electricity distribution and demonstrated that attackers could manipulate industrial control systems remotely. In 2017, the NotPetya outbreak caused global disruption across logistics companies, multinational enterprises, and government networks, showing how a destructive operation could generate strategic and economic effects far beyond its initial target set.
Modern Cyber Warfare Incidents (2018–Present)
Since 2018, cyber operations have become more tightly integrated with geopolitical crisis management, military planning, and infrastructure pressure. Rather than appearing as isolated sabotage events, they increasingly function as part of a wider contest for strategic access and operational advantage.
In February 2022, just before Russia launched its full-scale invasion of Ukraine, attackers disrupted the Viasat KA-SAT satellite network. The operation disabled thousands of satellite modems used by Ukrainian government and military users and also caused collateral disruption in parts of Europe. The attack demonstrated how cyber operations can degrade communications infrastructure at the opening stage of a conventional military campaign.

During the same conflict, destructive malware families such as WhisperGate, HermeticWiper, and CaddyWiper targeted Ukrainian government and organizational networks. These campaigns prioritized disruption over profit and illustrated how wiper malware fits naturally into wartime cyber operations.
Russian-linked operators also attempted another attack against Ukraine’s electricity infrastructure in 2022 using the Industroyer2 framework. Ukrainian defenders reportedly detected and contained the operation before it caused large-scale outages, but the attempt reinforced the continuing importance of energy systems in cyber conflict.
Other regional confrontations have also highlighted cyberwarfare dynamics. Security reporting and government statements have linked operations affecting water systems, shipping, logistics, and other strategic targets to the long-running shadow conflict between Iran and Israel. These incidents show how states can use cyber means for signaling, disruption, and coercive pressure without crossing immediately into open military escalation.
More recent campaigns tied to Chinese state actors have drawn attention to a different model: strategic pre-positioning inside critical infrastructure and communications networks. Activity associated with groups such as Volt Typhoon has been described by government agencies as an effort to maintain access inside infrastructure that could become relevant during a future crisis.
Separate U.S. government statements on PRC targeting of commercial telecommunications infrastructure have reinforced the importance of telecom networks as strategic terrain. Not every such intrusion should be labeled cyber warfare; some are better classified as espionage or battlespace preparation. Even so, they show how modern cyber conflict increasingly depends on persistent access established well before any visible confrontation begins.
Taken together, these developments show that cyber warfare is no longer defined only by isolated sabotage events. It now includes communications disruption, destructive malware, infrastructure targeting, influence support, and long-term pre-positioning designed to shape the battlefield before a crisis escalates.
For a deeper analysis of how these events unfolded and how they reshaped NATO and European cyber defense thinking, see our detailed breakdown of the 2007 Estonia cyberattacks and how they shaped modern cyber defense.
Types of Cyber Warfare Operations
Cyber warfare encompasses a wide range of digital operations designed to achieve strategic effects against an adversary. These activities extend far beyond simple network intrusions. In most cases, state-linked campaigns combine several techniques that support intelligence collection, disruption, and influence.
Major categories of cyber warfare operations include:
- Cyber espionage campaigns targeting government institutions and strategic industries
- Disruption and denial attacks designed to degrade services or communications
- Infrastructure sabotage operations targeting industrial systems and utilities
- Information and influence operations intended to shape public perception
- Strategic pre-positioning campaigns that establish long-term access to critical networks
Espionage Operations
Many cyber campaigns conducted by states begin with intelligence gathering. Threat actors infiltrate government networks, defense contractors, telecommunications providers, or research institutions to collect sensitive information. This intelligence can reveal diplomatic strategy, military capabilities, or technological development.
Disruption and Denial Operations
Disruption operations aim to temporarily degrade services or prevent systems from functioning normally. Distributed denial-of-service (DDoS) attacks are a common example, where attackers overwhelm online services with traffic and render them unavailable. Although these disruptions are often temporary, they can undermine public trust and complicate crisis response.
Infrastructure Sabotage
More advanced cyber warfare operations target industrial control systems and operational technology environments. By manipulating industrial processes, attackers may damage equipment, halt production, or interrupt essential services such as electricity or water distribution. These attacks represent one of the most serious forms of cyber conflict because they can create physical consequences.
Information and Influence Operations
Cyber campaigns may also involve influence operations designed to manipulate public perception or political discourse. Attackers may steal sensitive communications and selectively release them, conduct coordinated disinformation campaigns, or amplify polarizing narratives across digital platforms.
In practice, cyber warfare campaigns rarely rely on a single tactic. Intelligence collection often enables later sabotage operations, while influence campaigns can amplify the psychological impact of technical disruptions.

Cyber Weapons and Destructive Malware
Some cyber warfare operations rely on highly specialized malware designed to achieve strategic effects. These tools are often referred to as cyber weapons because they are built specifically to sabotage infrastructure, manipulate industrial systems, or disrupt critical services.
The most widely cited example is Stuxnet, discovered in 2010. The malware targeted industrial control systems used in Iran’s nuclear enrichment program and caused physical damage to uranium centrifuges. Stuxnet demonstrated that cyber operations could move beyond espionage and produce real-world destruction.
Later incidents expanded the understanding of cyber weapons. The Industroyer malware family targeted electricity distribution infrastructure in Ukraine, while the Triton malware focused on industrial safety systems used in petrochemical facilities. These attacks showed how cyber operations could interfere with industrial processes and potentially endanger human safety.
Destructive malware has also been used in broader strategic campaigns. The NotPetya attack in 2017 initially appeared to be ransomware but functioned as a wiper that permanently destroyed data on infected systems. The malware spread rapidly across corporate networks and caused billions of dollars in economic damage worldwide.
These examples illustrate how cyber weapons differ from traditional malware used in cybercrime. Rather than seeking financial gain, these tools are designed to degrade infrastructure, disrupt economic activity, or impose strategic costs on adversaries.
Nation-State Cyber Warfare Units
Most major powers now maintain dedicated cyber units responsible for conducting offensive and defensive operations in digital space. These organizations operate within military structures, intelligence services, or specialized government agencies and form a core component of modern national security strategy.
The United States established U.S. Cyber Command (USCYBERCOM) to coordinate cyber operations across the military. The command oversees cyber mission teams that conduct defensive operations to protect military networks while also supporting offensive operations against adversary infrastructure when authorized.
Russia has integrated cyber capabilities within military intelligence structures, particularly units linked to the GRU. Several cyber campaigns attributed to Russian actors have targeted government institutions, election infrastructure, and critical systems in other countries.
China has also developed significant cyber capabilities through the People’s Liberation Army and associated intelligence organizations. These units conduct espionage campaigns targeting intellectual property, technology development, and strategic industries.
Other nations, including Iran and North Korea, have invested heavily in cyber capabilities as a way to offset conventional military disadvantages. Cyber operations allow these states to project power, gather intelligence, and influence geopolitical outcomes without engaging in direct military confrontation.
The expansion of national cyber units demonstrates that cyberspace is now considered an operational domain alongside land, sea, air, and space. As a result, cyber capabilities are increasingly integrated into broader military planning and national defense strategies.
Critical Infrastructure as a Cyber Warfare Battlefield
Modern societies depend heavily on interconnected digital infrastructure. Energy grids, telecommunications networks, transportation systems, financial platforms, and water utilities all rely on networked technologies to function efficiently. This dependence makes critical infrastructure a primary target during cyber conflict.
Cyber warfare operations targeting infrastructure can have cascading effects across entire economies. Disrupting a power grid can interrupt manufacturing, telecommunications, healthcare services, and emergency response systems. Even temporary outages may cause significant economic losses and undermine public confidence.
Industrial control systems (ICS) and operational technology (OT) environments are particularly attractive targets for advanced cyber actors. These systems manage physical processes such as electricity generation, pipeline operations, water treatment facilities, and transportation networks. If compromised, attackers may be able to manipulate equipment, halt production processes, or damage machinery.
Several high-profile cyber incidents have demonstrated the risks associated with infrastructure targeting. Attacks against Ukraine’s power grid showed how adversaries could remotely manipulate electricity distribution systems. Other campaigns have focused on oil pipelines, maritime logistics, and satellite communications.
Because infrastructure networks are essential to national stability, governments increasingly treat their protection as a core element of national defense.
Cybersecurity programs for critical infrastructure now involve close coordination between private industry, government agencies, and international partners.
The Future of Cyber Warfare
Cyber warfare is entering a new phase shaped by persistent geopolitical competition, infrastructure infiltration campaigns, and rapid advances in artificial intelligence. Unlike earlier cyber operations that focused primarily on espionage or isolated sabotage events, modern cyber strategy increasingly emphasizes long-term access to strategic systems and the ability to disrupt them during periods of crisis.
One of the most significant developments is the rise of pre-positioning operations. Intelligence agencies have warned that state-linked threat actors are attempting to infiltrate critical infrastructure networks such as energy grids, telecommunications systems, transportation infrastructure, and satellite communications. These campaigns appear designed to establish dormant access that could be activated during a future conflict. Activity associated with groups such as Volt Typhoon illustrates how cyber operations may be used to quietly prepare the digital battlefield years before any military confrontation occurs.
Artificial intelligence is also transforming both offensive and defensive cyber capabilities. Machine learning systems can assist in vulnerability discovery, automated reconnaissance, and large-scale analysis of network telemetry. Offensive actors may use AI tools to accelerate malware development, improve social engineering campaigns, and automate portions of intrusion workflows. At the same time, defenders are increasingly deploying AI-driven detection systems to identify anomalous behavior across large enterprise networks.
Another emerging dimension involves software supply chain compromise. Rather than attacking a target directly, adversaries may infiltrate widely used software platforms or development environments in order to gain access to thousands of downstream organizations simultaneously. These operations can create systemic risk across entire sectors, particularly when critical infrastructure operators rely on the affected software.
Strategically, cyber warfare is becoming closely linked to the concept of cyber deterrence. Governments increasingly view cyber capabilities as tools for signaling strength, imposing costs, and shaping adversary behavior without crossing the threshold of conventional military conflict. As a result, cyber operations are likely to remain a persistent feature of geopolitical rivalry rather than an occasional wartime tactic.
For defenders, the key implication is that cyber conflict is becoming continuous.
Organizations operating critical systems must assume that sophisticated actors may attempt to establish long-term access to networks and infrastructure. Strengthening visibility across operational technology environments, improving supply chain security, and coordinating intelligence sharing between governments and private industry will be essential for managing the risks associated with future cyber warfare campaigns.
Cyber Warfare Doctrine, Attribution, and Legal Thresholds
One reason cyber warfare remains difficult to define is that not every serious cyberattack qualifies as warfare. Security incidents vary widely in intent, scale, target selection, and strategic effect. A ransomware operation may cause major disruption without being an act of war. A long-term espionage campaign may compromise highly sensitive systems without crossing the threshold into cyber warfare. The distinction depends on who is behind the operation, what objective they are pursuing, and how the activity fits into broader geopolitical or military competition.
In strategic terms, cyber warfare is usually associated with state action or state-directed activity intended to produce coercive, disruptive, or destructive effects against an adversary. That can include degrading military command systems, disrupting national infrastructure, shaping crisis conditions, or preparing the battlespace before conventional conflict. This is why analysts often distinguish between cyber operations, cyber warfare, and cyber war.
- Cyber operations happen continuously.
- Cyber warfare describes the use of digital means for warfare-like strategic objectives.
- Cyber war implies a broader and more sustained conflict between states in which cyber operations form a central part of the confrontation.
Attribution is central to that analysis. In conventional conflict, identifying the attacker is often straightforward. In cyberspace, attackers can route operations through compromised infrastructure, leased servers, proxy groups, or criminal intermediaries. That ambiguity gives states room to apply pressure without immediate public attribution or overt military escalation. It also means defenders and policymakers must assess not only malware and infrastructure, but also timing, targeting, victimology, operational tradecraft, and geopolitical context.
Legal thresholds add another layer of complexity. International law does not treat every intrusion as an armed attack.
Many cyber operations fall into a gray zone below the threshold of open war, even when they are serious, persistent, and strategically significant. The result? cyber conflict often unfolds in a contested space between espionage, coercion, sabotage, and military signaling.
This means the most important question is not simply whether a system was compromised, but whether the operation appears designed to create strategic effects that align with state doctrine or conflict dynamics.
This definitional ambiguity is one of the reasons cyber warfare remains such an important analytical topic. It forces security teams, journalists, and policymakers to move beyond technical indicators alone and examine intent, proportionality, escalation risk, and the role of national strategy in digital operations.
Hybrid Warfare and the Role of Cyber Operations
Cyber warfare rarely occurs in isolation. In modern conflicts it is often integrated into broader strategies known as hybrid warfare, where multiple instruments of national power are used simultaneously to influence or weaken an adversary. These instruments may include cyber operations, information warfare, economic pressure, diplomatic coercion, and conventional military activity.
Hybrid warfare strategies seek to exploit ambiguity and operate below the threshold of open war. Cyber operations are particularly valuable in this context because they can disrupt communications, leak sensitive information, or undermine public trust while still allowing governments to deny direct involvement.
One common hybrid warfare tactic involves combining cyber intrusions with information operations. For example, attackers may steal documents or communications from political organizations and then release selected materials publicly in order to influence political debates or undermine public confidence in institutions.
Cyber operations may also support conventional military activity. Disrupting satellite communications, targeting logistics systems, or degrading air-defense networks can create operational advantages during kinetic military campaigns. The cyber attack against the Viasat satellite network at the beginning of Russia’s 2022 invasion of Ukraine illustrated how digital operations can be synchronized with military actions.
Because hybrid warfare blends multiple forms of pressure, cyber operations are increasingly used to shape strategic conditions long before a crisis escalates into open conflict. This integration of cyber capabilities into broader geopolitical competition is one of the defining characteristics of modern cyber warfare.