Volt Typhoon is one of the most important cyber campaigns in the modern threat landscape because U.S. agencies do not describe it as routine espionage. They describe it as pre-positioning inside critical infrastructure. In a joint February 2024 advisory, CISA, the FBI, and the NSA said PRC state-sponsored actors linked to Volt Typhoon had compromised U.S. critical-infrastructure networks and were seeking to maintain long-term access for disruptive or destructive effects during a future crisis. That makes Volt Typhoon a cyber-warfare story, not just a threat-intelligence label.
Microsoft first publicly detailed the campaign in May 2023, reporting that the actor had been active since mid-2021 and had targeted organizations in Guam and elsewhere in the United States. The sectors Microsoft identified included communications, manufacturing, utilities, transportation, construction, maritime, government, information technology, and education. Guam mattered because it is a critical U.S. military hub in the Pacific, and Microsoft assessed that the campaign’s targeting could support the PRC’s wider strategic goals in the event of regional conflict.
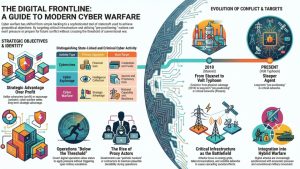
That combination of stealth, infrastructure access, and geopolitical context is why Volt Typhoon now sits at the center of debates about cyber deterrence, resilience, and battlespace preparation. It is also why the campaign belongs alongside cases like Stuxnet and our broader analysis of cyber warfare and strategic digital operations.
What Volt Typhoon Is and Why It Alarmed U.S. Agencies
Volt Typhoon first entered public view in May 2023, when Microsoft disclosed a China-based state actor that had been active since mid-2021 and had targeted critical infrastructure organizations in Guam and elsewhere in the United States. Microsoft said the actor relied heavily on living-off-the-land techniques, which means it used legitimate administrative tools and stolen credentials instead of obvious malware. That tradecraft made the activity harder to detect and helped the operators blend into normal network traffic.
What turned the campaign into a national-security issue was the target set. In its original disclosure, Microsoft said Volt Typhoon hit organizations in communications, manufacturing, utilities, transportation, construction, maritime, government, information technology, and education. U.S. agencies sharpened that warning in a February 2024 joint advisory, which said PRC state-sponsored actors were maintaining access across U.S. critical infrastructure and appeared to be positioning themselves for disruptive or destructive effects during a future crisis. The advisory put special emphasis on communications, energy, transportation systems, and water and wastewater systems.
Guam is central to understanding that warning. The island is a major U.S. military and logistics hub in the Pacific, and any conflict involving Taiwan or wider regional escalation would make its communications and infrastructure strategically important. Microsoft said it assessed with moderate confidence that Volt Typhoon’s Guam targeting could support the PRC’s military objectives in a future crisis. That assessment is one reason the campaign is often described as battlespace preparation rather than classic espionage.
How Volt Typhoon Hid Its Activity
Volt Typhoon stood out not because it used flashy malware but because it minimized its digital footprint. Microsoft said the group focused on post-compromise credential access and network system discovery while using built-in tools to avoid detection. The joint U.S. government advisory reached the same conclusion and described activity designed to blend with legitimate administrator behavior, harvest credentials, and maintain persistence over long periods.
The campaign’s concealment methods became clearer in January 2024, when the U.S. Department of Justice announced that the FBI had disrupted a botnet the PRC actors used to hide their operations. According to the DOJ, the hackers known in the private sector as Volt Typhoon routed activity through hundreds of compromised small office and home office routers infected with KV Botnet malware. Those routers helped obscure the Chinese origin of the intrusions and provided a covert relay layer for follow-on operations against victims in the United States and elsewhere.
That detail matters because it shows Volt Typhoon was not simply scanning for opportunity. It had infrastructure, patience, and a concealment architecture designed to support long-term access. In other words, the campaign combined strategic target selection with quiet tradecraft, which is exactly what makes pre-positioning inside critical infrastructure so dangerous.
The U.S. Response: Disrupting the KV Botnet
U.S. officials did not treat Volt Typhoon as a routine intrusion set. On January 31, 2024, the Department of Justice announced that the FBI had disrupted the KV Botnet, a network of hundreds of compromised small office and home office routers that PRC-linked operators used to conceal their activity. According to the DOJ, the botnet let the hackers relay traffic through U.S.-based devices and hide the Chinese origin of their intrusions. That infrastructure mattered because it gave the operators a covert bridge into follow-on operations against victims in the United States and abroad.
The language U.S. officials used was unusually blunt. FBI Director Christopher Wray said China’s hackers were targeting American civilian critical infrastructure and were “pre-positioning to cause real-world harm” in the event of conflict. Deputy Attorney General Lisa Monaco said the disruption showed the government was using all its tools to counter national-security threats in real time. Those statements are important because they show how Washington framed Volt Typhoon: not as a one-off breach, but as an operational threat to civilian infrastructure.
Why Volt Typhoon Matters Strategically
Volt Typhoon matters because it sits in the gray zone between espionage and wartime preparation. Espionage campaigns usually focus on stealing secrets and preserving access. Volt Typhoon appears to have gone further by targeting sectors that would matter during a military crisis, including communications, energy, transportation, and water. In the March 2024 CISA fact sheet for critical-infrastructure leaders, the U.S. government warned that PRC cyber activity posed an urgent risk because of its potential to disrupt essential services during geopolitical escalation.
This is why analysts often describe Volt Typhoon as pre-positioning or battlespace preparation. The campaign did not need to launch immediate sabotage to be strategically significant. Long-term access inside infrastructure can create coercive leverage before a crisis even starts. In that sense, Volt Typhoon has become one of the clearest modern examples of how cyber operations can prepare the battlefield long before any overt conflict begins.
What Defenders Should Learn From the Campaign
Volt Typhoon also exposed several practical weaknesses in real-world defense. The campaign showed how attackers can blend into networks by abusing valid credentials, built-in administrative tools, and poorly secured edge devices. It also showed why defenders cannot assume that a lack of obvious malware means a lower level of risk. CISA’s living-off-the-land guidance stresses that defenders need stronger visibility into authentication, command-line behavior, credential use, and remote administration activity, especially in critical-infrastructure environments.
For security teams, the lesson is straightforward. A stealthy state actor does not need ransomware or wiper malware to create strategic risk. Quiet access, patient tradecraft, and the right target set can be just as dangerous. That is what makes Volt Typhoon one of the most consequential cyber campaigns to study today.
Volt Typhoon and the Future of Cyber Conflict

Volt Typhoon is important because it gives defenders a modern example of how cyber operations fit into state strategy. The campaign did not need to launch immediate sabotage to become strategically significant. By maintaining quiet access inside communications, transportation, energy, and water-related networks, the operators created the option to impose disruption later. That is why U.S. agencies repeatedly describe the campaign in terms of pre-positioning, resilience, and crisis readiness rather than simple data theft.
The case also helps explain why cyber warfare now includes much more than destructive malware. Campaigns like Volt Typhoon show that strategic effect can begin long before an outage or a wiper attack appears. Long-term access to infrastructure, concealed through living-off-the-land tradecraft and covert relay networks such as the KV Botnet, can shape the battlefield before open conflict begins. That makes Volt Typhoon one of the clearest recent examples of how states can prepare the digital battlespace while staying below the threshold of war.
For readers trying to understand where this fits in the bigger picture, Volt Typhoon is best viewed as a warning about the convergence of espionage, infrastructure access, and coercive potential. It is not just a China-linked intrusion cluster. It is a case study in how modern cyber campaigns can create strategic leverage years before a geopolitical crisis turns visible.