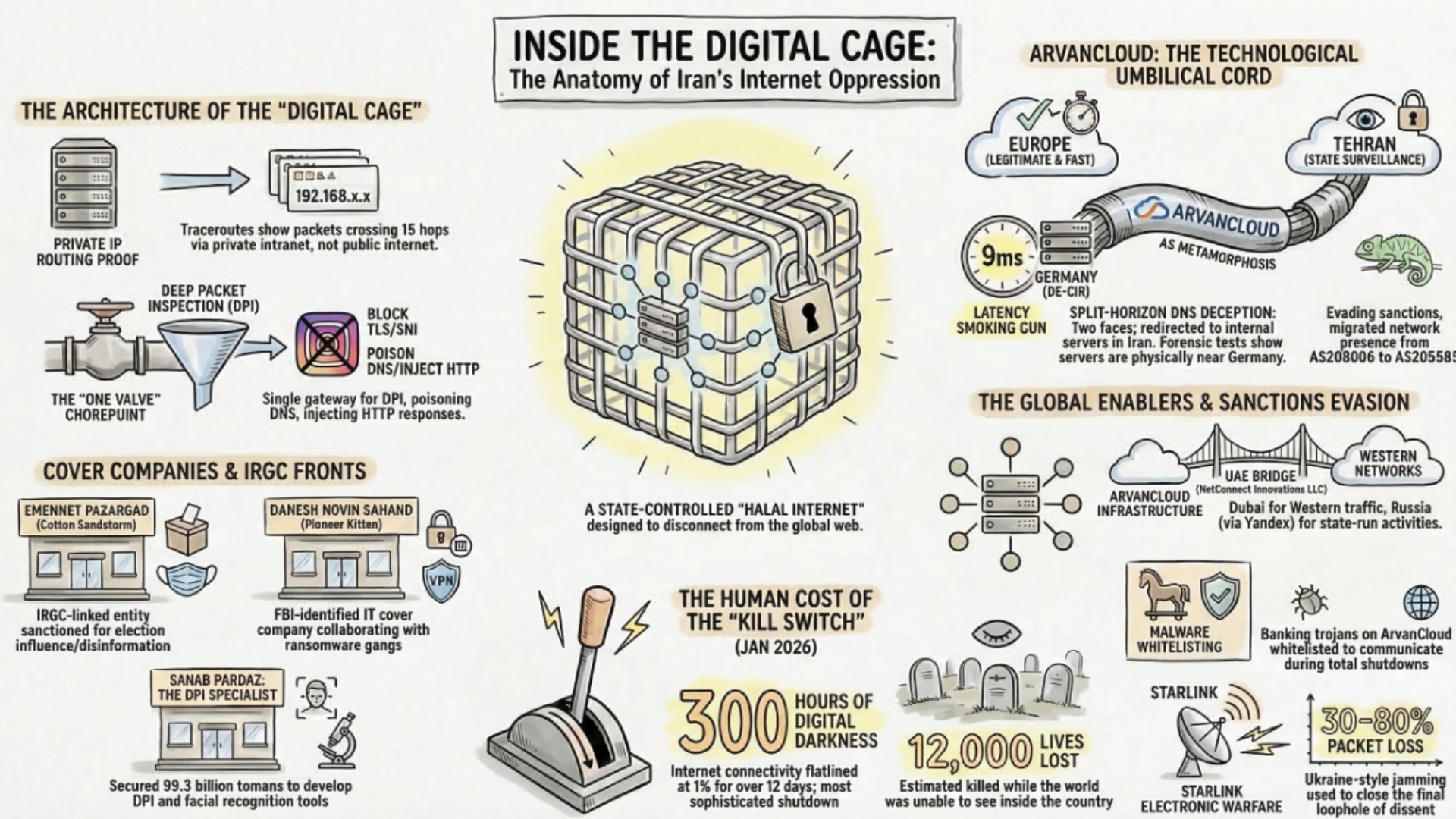
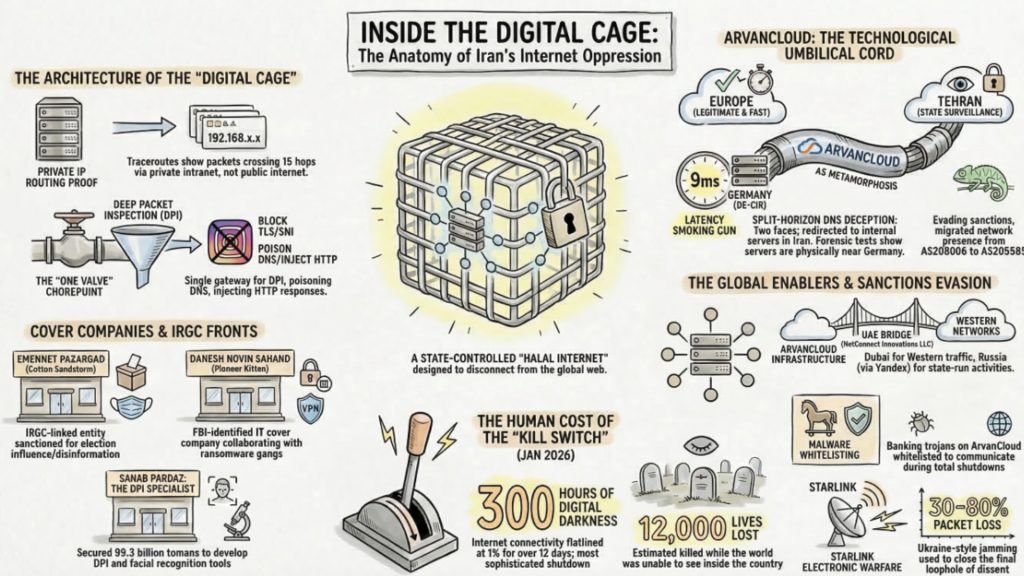
Iran has constructed one of the most sophisticated digital censorship and surveillance infrastructures in history — a system that rivals China’s Great Firewall in ambition and increasingly surpasses it in ruthlessness of deployment. At the center of this architecture sits the National Information Network (NIN), often referred to as the “Halal Internet” or the regime’s “Digital Cage.”
This system goes far beyond content filtering. It is a redundant, self-sufficient ecosystem engineered to allow the regime to sever Iran’s connection to the global internet entirely, while keeping state services, banks, and propaganda channels operational domestically.
Implementing such a system would not be possible without specialized service providers like ArvanCloud (Noyan Abr Arvan) and their obscured partner networks.
This forensic analysis — based on BGP routing tables, latency measurements, and traceroute data — reveals the evidence for this collaboration and maps the global network of enablers that make Iran’s digital oppression technically possible.
Inside Iran’s National Information Network and Kill Switch
Tehran’s stated goal is sovereignty over cyberspace. Technically, this means decoupling Iranian infrastructure from global Tier-1 providers.
Functionally, the NIN operates like a closed transit system: while the open internet offers users freedom to navigate to any destination worldwide, the NIN only permits travel on predefined, state-controlled routes.
Forensics of Internal Isolation: Private IP Routing
Critical evidence for the NIN’s existence emerges from traceroute analyses conducted inside Iran. When measuring services like the search engine zarebin.ir or the state messenger ble.ir,
data packets are routed almost exclusively via IP addresses in the 192.168.x.x range — addresses defined by RFC 1918 as private, non-publicly routable.
These private addresses normally appear only within home networks or corporate LANs. The fact that they span 15 hops across a nationwide backbone physically proves that users never reach the public internet.
They are trapped within a gigantic, hermetically sealed intranet.
In contrast, a traceroute to the same ArvanCloud nameserver k.ns.arvancdn.ir from outside Iran reveals a completely different path:
Tracing route to k.ns.arvancdn.ir [185.143.232.253]
1 19 ms 10.5.0.1
2 27 ms cs0-fra15.de.as25369.net [193.124.21.1]
3 87 ms ae10.10.rt0-fra15.de.as25369.net [5.226.136.54]
4 21 ms et-2-5-1.cr7-fra2.ip4.gtt.net [154.14.144.189]This dual reality is the foundation of the Kill Switch. When the regime withdraws its BGP announcements to Western providers like GTT or Arelion, the connection to the outside world collapses. But because critical state services are hosted within the NIN, they remain operational. Citizens can still pay taxes and access state propaganda apps — they simply cannot reach Instagram, WhatsApp, or independent news sources. This is precisely what occurred during the January 2026 internet blackout, when connectivity dropped to approximately 1% of normal levels for over 300 hours.
The Stealth Blackout Model
A 2025 arXiv study revealed a new censorship model: Iran kept BGP announcements alive globally while severing real connectivity — an “imperceptible shutdown.”
Active measurements documented four simultaneous censorship layers operating at a single national gateway:
- DNS Poisoning: Over 90% of blocked domains resolved to 10.10.34.34 — a private IP blackhole hosting a generic block page.
- HTTP Filtering: DPI inspected Host headers and URL paths, injecting 403 responses or TCP RST packets for blacklisted keywords.
- TLS/SNI Blocking: Censors read the SNI field of TLS handshakes, aborting connections to services like Telegram and Instagram.
- Protocol Whitelist: Only DNS, HTTP, and HTTPS pass the border gateway. All other protocols — SSH, VPNs, OpenVPN — are silently dropped by DPI.
This “censorship-in-depth” rendered traditional VPN usage nearly impossible and triggered a 707% spike in VPN search demand.
As Northeastern’s Josep Jornet explained: “Think of it like a house with only one main water valve. Even if there are many faucets inside, the government holds the main valve.”
Split-Horizon DNS: The Two Faces of ArvanCloud
As a CDN and DNS provider, ArvanCloud employs a potent technique known as Split-Horizon DNS to manage its dual-facing infrastructure.
DNS — the Domain Name System — is the internet’s phone book. ArvanCloud operates the nameservers for virtually all critical Iranian state services. Forensic analysis reveals a massive discrepancy:
- From Europe: A DNS request for ble.ir (a state-sponsored messenger) returns an IP in Frankfurt or Paris (e.g.,
185.143.232.253) - From Tehran: The identical request redirects to an internal IP at Respina Networks or Mobinnet
Such dual-response system serves two strategic purposes:
External Facade: ArvanCloud presents itself as a modern cloud provider with global reach. European servers in Frankfurt and Paris make services appear fast and legitimate, while also providing DDoS protection.
Internal Control Layer: Domestically, users are directed to servers under total surveillance by security organs. Since traffic never leaves the country, international data protection standards do not apply, and intelligence services can intercept communications at network nodes.
DPI at the Border: More Than DNS
The split-horizon strategy represents only one layer. Academic research confirms the border gateway runs deep packet inspection on all layers simultaneously.
TTL-based path analysis shows all interference — DNS poisoning, HTTP injection, TLS resets — originates at a unified “filternet” chokepoint operated by TCI at the national border, not at individual ISPs. One valve controls all traffic.
ArvanCloud: The Regime’s Strategic Bridge to the Outside World
Sanctioned entity ArvanCloud (Noyan Abr Arvan) functions as the regime’s technological umbilical cord.
Even under international sanctions — including designation by the US Treasury’s OFAC (June 2023), the UK OFSI (September 2023),
and Australian DFAT (September 2023) — the company has maintained its infrastructure through a complex web of camouflage identities and partners.
AS Metamorphosis: From AS208006 to AS205585
ArvanCloud originally operated under Autonomous System Number AS208006. Following the massive 2022 Mahsa Amini protests and subsequent sanctions, a new entity emerged:
AS205585 (Noyan Abr Arvan Co. – Private Joint Stock), registered April 21, 2022 under RIPE.
BGP analysis confirms AS205585’s upstreams include:
- AS208006 – ArvanCloud Global Technologies L.L.C (Dubai)
- AS200315 – NetConnect Innovations LLC (Dubai)
- AS202468 – Noyan Abr Arvan Co. (Private Joint Stock)
Under this new AS, Anycast IPs for critical services in Europe are announced. AS205585 connects directly to the Dubai-based bridge entity NetConnect Innovations (AS200315), which in turn passes traffic to Western Tier-1 providers.
Physical Presence in Europe: Latency as Evidence
Notably, ArvanCloud claims it is merely a “cloud” whose physical location is irrelevant. Network forensics refutes this.
A traceroute from a Frankfurt server to the ArvanCloud IP 185.143.232.253
(nameserver for state apps) shows a latency of only 9 milliseconds. Given the speed of light in fiber optics (~200,000 km/s), 9 ms round-trip translates to a maximum distance of approximately 900 km.
Physical proof places the server is located in the immediate vicinity of the DE-CIX internet exchange in Frankfurt — not in Iran. In effect, ArvanCloud hosts the “signposts” for Iranian oppression infrastructure on European soil.
Case Studies: The Censorship Architecture in Action
Zarebin.ir: Iran’s State Search Engine
Zarebin.ir (“The Magnifying Glass”) is not merely a search engine;
it is a curated catalog of the regime. During a total internet shutdown, Google becomes useless — Zarebin takes over as the sole navigator within the NIN.
Technical analysis shows Zarebin is physically hosted in Iran at MCI
(Mobile Telecommunication Company of Iran), a company under control of the Revolutionary Guards. The data path from Europe to Zarebin reveals a massive latency jump from 20 ms to 172 ms during the transition into the Middle East via PCCW Global (AS3491).
Critically, ArvanCloud provides the DNS infrastructure for Zarebin (q.ns.arvancdn.com). Without ArvanCloud’s nameservers, Zarebin would be homeless in the global network.
Google SafeSearch Hijacking
One of the regime’s most insidious “smart censorship” tools is the manipulation of regular Google traffic. Forensic traceroutes to google.com from Iran show requests redirected to the IP 216.239.38.120 — the Google SafeSearch VIP. Originally developed for schools, the regime abuses this function via DNS hijacking. Users believe they are using the real Google, but see a politically sanitized version in which results regarding protests or opposition are suppressed.
Cafe Bazaar: The Espionage Vector
With Google Play frequently blocked in Iran, cafebazaar.ir serves as the default app store. Traceroute analysis confirms Cafe Bazaar is prioritized within the NIN (AS58224/TCI), while Google Play is throttled or blocked.
Cafe Bazaar operates outside Google Play Protect controls. The regime can distribute “Super-Apps” demanding excessive permissions — reading contacts, location data, and messages. During protest waves, forced updates carrying surveillance malware can be pushed without user warnings.
Rubika and Domestic Messaging: Surveillance by Design
Filterwatch reported that the Open Technology Fund’s Security Lab found three widely used Iranian messaging apps — including Rubika — are not safe.
Over 67% of Iranian internet users have been forced to download domestic messaging apps at least once. During shutdowns, apps like Rubika, Eitaa, and Bale become the only functional platforms — all operating under regime surveillance with no encryption guarantees.
Russia Connection: Sanctions Evasion and Cryptocurrency Laundering
Beyond the “West Route” via Frankfurt, ArvanCloud has established an “East Route” to Russia.
A dual purpose drives this route: as a strategic reserve and for processing sanctioned financial operations.
Energy Laundering via VimpelCom and Yandex
While the general population barely reaches 1% of normal traffic during shutdowns,
one channel remains open: state-run Bitcoin mining. Forensic data shows domains like btc.ir.powhashing.com resolving to IPs within the Yandex Cloud (AS13238) in Russia.
The mining endpoints observed:
stratum+tcp://btc.ir.powhashing.com:3333
stratum+tcp://btc.ir.powhashing.com:443
stratum+tcp://btc.ir.powhashing.com:25
stratum+tcp://btc.me.powhashing.com:3333
stratum+tcp://btc.me.powhashing.com:443
stratum+tcp://btc.me.powhashing.com:25A definitive routing chain emerges: Iran (ArvanCloud/AS208006) → Russia (VimpelCom/AS3216) → Russia (Yandex/AS208722). This path bypasses Western nodes entirely.
Authorities convert cheap Iranian electricity into Bitcoin, laundering proceeds through Russian exchanges to generate foreign currency. ArvanCloud provides the technical infrastructure for this channel, which remains functional even when Western connections are completely severed.

Emotet Evidence: Proof of State Whitelisting
Perhaps the most damning evidence of the NIN’s true purpose comes from the discovery of active malware on ArvanCloud infrastructure during an internet shutdown.
In January 2026, it was documented that the domain sarvkaran.com, hosting the Emotet banking trojan, was active on ArvanCloud’s AS205585. URLhaus records and VirusTotal detections confirm this malware presence.
Cloudflare Radar data confirms that at this time, the population’s mobile traffic had plummeted to 0.9% of normal levels.
Yet the malware server communicated unhindered with Command-and-Control servers abroad. This technically proves the state firewall operates a whitelist: communication between mothers and their children via WhatsApp is blocked, but the traffic of banking trojans targeting Western victims is explicitly permitted.
In practice, ArvanCloud effectively serves as a bulletproof hoster under state protection.
Iran’s Cyber Cover Companies: IRGC Front Entities Exposed
ArvanCloud does not operate in a vacuum. It exists within a broader ecosystem of Iranian “cover companies” — corporate shells that masquerade as legitimate IT firms while conducting offensive cyber operations on behalf of the IRGC and intelligence services.
Afkar System Yazd Company & Najee Technology: IRGC Ransomware Operations
On September 14, 2022, the US Treasury sanctioned Afkar System Yazd Company and Najee Technology Hooshmand Fater LLC as IRGC-affiliated entities responsible for ransomware campaigns against US critical infrastructure.
Afkar System, based at Building 5, Amir al-Momenein Alley, Yazd, was managed by Ahmad Khatibi Aghda, who personally participated in encrypting victim networks using Microsoft BitLocker and negotiated ransoms. Their operations overlapped with campaigns attributed to APT35, Charming Kitten, Nemesis Kitten, and Tunnel Vision.
Victim targets included a US children’s hospital, a New Jersey municipality, electric utility companies, healthcare practices, emergency services, educational institutions, and transportation providers — all attacked between 2020 and 2022 using exploits for Fortinet and Microsoft Exchange ProxyShell vulnerabilities.
Companion entity Najee Technology Hooshmand Fater LLC, located in Karaj, Alborz Province, was owned by Mansour Ahmadi. Together with Afkar System, these firms provided the operational cover for 10+ IRGC-linked cyber operatives, including individuals with active $10 million Rewards for Justice bounties.

Emennet Pasargad: Election Interference and Hack-and-Leak Operations
Emennet Pasargad — formerly known as Net Peygard Samavat Company and also operating under the alias Eeleyanet Gostar — represents a different branch of Iran’s offensive cyber apparatus: information warfare and election interference.
Linked directly to the IRGC Electronic Warfare and Cyber Defense Organization (IRGC-EWCD), Emennet was sanctioned by OFAC on November 18, 2021 for attempting to influence the 2020 US presidential election.
Between August and November 2020, Emennet operatives obtained US voter information from state election websites, sent threatening emails to intimidate voters, and compromised content management systems of US media entities to inject disinformation — including a fabricated video designed to undermine faith in ballot integrity.
Managed by Mohammad Bagher Shirinkar, Emennet was previously designated under its former name in February 2019 for supporting the IRGC-EWCD. After sanctions were imposed, the company simply rebranded — a pattern identical to ArvanCloud’s AS metamorphosis from AS208006 to AS205585.
In September 2024, Treasury expanded sanctions against additional Emennet operatives for continued attempts to interfere in US elections. Operations attributed to Emennet have also targeted European and Israeli organizations with “hack-and-leak” campaigns.
Danesh Novin Sahand: FBI-Identified Ransomware Cover Entity
Danesh Novin Sahand has been identified by the FBI as an Iranian IT cover company enabling ransomware attacks. While not yet listed in international sanctions databases like OpenSanctions, FBI advisories flag this entity as providing operational cover for Iranian cyber actors conducting ransomware and data theft campaigns.
FBI analysis in a joint CISA/FBI/DC3 advisory (August 2024) reveals Danesh Novin Sahand as the cover for Pioneer Kitten (Fox Kitten, UNC757, Parisite, Lemon Sandstorm).
Active since 2017, Pioneer Kitten targets U.S. defense, education, finance, and healthcare sectors by exploiting VPN vulnerabilities in Citrix, Palo Alto PAN-OS, Check Point, and BIG-IP F5 devices.
Critically, FBI confirmed Pioneer Kitten collaborates directly with ransomware affiliates including NoEscape, Ransomhouse, and ALPHV/BlackCat.
Operators use the handles ‘Br0k3r’ and ‘xplfinder’ to sell domain admin credentials on cybercrime forums. Data theft operations have also targeted Israel and Azerbaijan in direct support of GOI interests.
Cover Entity Summary
| Entity | APT Alias | IRGC Link | Sanctioned | Primary Activity |
|---|---|---|---|---|
| Emennet Pasargad | Cotton Sandstorm | IRGC-EWCD | OFAC Nov 2021 | Election interference, hack-and-leak |
| Danesh Novin Sahand | Pioneer Kitten | GOI-linked | FBI-flagged (not yet OFAC) | VPN exploitation, access brokering |
| ArvanCloud | N/A (infrastructure) | State-aligned | OFAC June 2023 | CDN/DNS for censorship apparatus |
Operational Pattern: Rebrand, Repeat, Deny
A consistent pattern emerges across all documented Iranian cover entities: operate under a legitimate IT company facade, conduct offensive cyber operations, get exposed by Western intelligence, then rebrand and continue.
Net Peygard Samavat became Emennet Pasargad, which became Aria Sepehr Ayandehsazan. ArvanCloud migrated its BGP presence from AS208006 to AS205585. Each transformation preserved operational continuity while resetting attribution clocks.
ArvanCloud fits within this ecosystem not as a direct APT operator, but as the infrastructure backbone that enables the entire apparatus — providing CDN, DNS, and hosting services within the NIN’s controlled architecture.
Global Network of Enablers
Neither ArvanCloud nor NetConnect Innovations could operate without access to Western networks. The following maps the infra providers and responsible authorities.
UAE — The Hub
| Company | ASN | Role |
|---|---|---|
| NetConnect Innovations LLC | AS200315 | Main bridge between ArvanCloud and the West |
| ArvanCloud Global Tech. | AS208006 | Dubai branch for bypassing sanctions |
Germany — The Technical Base
| Company | ASN | Role |
|---|---|---|
| uvensys GmbH | AS58010 | Upstream provider for NetConnect (AS200315) |
| Core-Backbone GmbH | AS33891 | Transit provider Frankfurt–Iran |
| Vodafone Group PLC | AS1273 | German backbone transport |
Responsible: BAFA (Federal Office for Economic Affairs and Export Control)
US — Global Tier-1 Carriers
| Company | ASN | Role |
|---|---|---|
| GTT Communications | AS3257 | Major Tier-1 carrier for ArvanCloud Europe traffic |
| Cogent Communications | AS174 | Transit for NetConnect (AS200315) |
| Hurricane Electric | AS6939 | Peering for ArvanCloud and NetConnect |
| TATA Communications | AS6453 | International transit hub |
| Zenlayer Inc. | AS21859 | Edge cloud partner for emerging markets |
Responsible: OFAC (Office of Foreign Assets Control, US Treasury)
Additional Transit Countries
| Country | Company | ASN | Role |
|---|---|---|---|
| Lithuania | Melbikomas UAB | AS56630 | Upstream for NetConnect |
| UK | Datacamp Limited (CDN77) | AS60068 | Upstream services |
| Canada | Aptum Technologies | AS13768 | Global connectivity partner |
| Italy | Telecom Italia Sparkle | AS6762 | Transit for ArvanCloud traffic |
| France | Orange S.A. | AS5511 | Transit and peering |
| Turkey | Superonline (Turkcell) | AS34984 | Main transit at border with Iran |
Four Smoking Guns: Forensic Evidence Summary
To establish accountability, the following four technical proofs form the evidentiary basis of this investigation:
- Latency Proof (Physical Location): The 9 ms latency from Frankfurt to ArvanCloud nameservers physically proves these servers are located in Germany or France — not Iran. Western companies actively host these servers on European soil.
Each of these findings is independently verifiable using publicly available tools: traceroute, dig, BGP looking glasses, and threat intelligence databases. Together, they form an irrefutable forensic case.
Sahab Pardaz
Sahab Pardaz, a little-known Iranian technology firm founded in 2014 rapidly grew into a key component of the country’s digital surveillance architecture. Within three years of its creation, the company secured a massive 99.3 billion toman contract from Iran’s state-owned Telecommunications Infrastructure Company to develop components of the government’s “Social and Cultural Protection Plan,” an initiative tied to Tehran’s broader national internet and censorship strategy.
The firm reportedly specialized in advanced data analytics and network intelligence systems. Among the technologies it developed were network traffic monitoring platforms, deep packet inspection (DPI) tools, large-scale data analysis systems, and facial recognition technologies. Such capabilities allow authorities to examine internet traffic in detail, identify individual users, and block or throttle specific content. Deep packet inspection in particular enables governments to analyze the contents of internet communications beyond basic metadata, making it one of the most powerful tools for large-scale internet filtering.
These technologies are widely believed to have contributed to Iran’s expanding digital control infrastructure, often referred to as the “national internet” or National Information Network (NIN). The system allows authorities to filter websites, restrict social media platforms, and in some cases disconnect parts of the country from the global internet while maintaining domestic services.
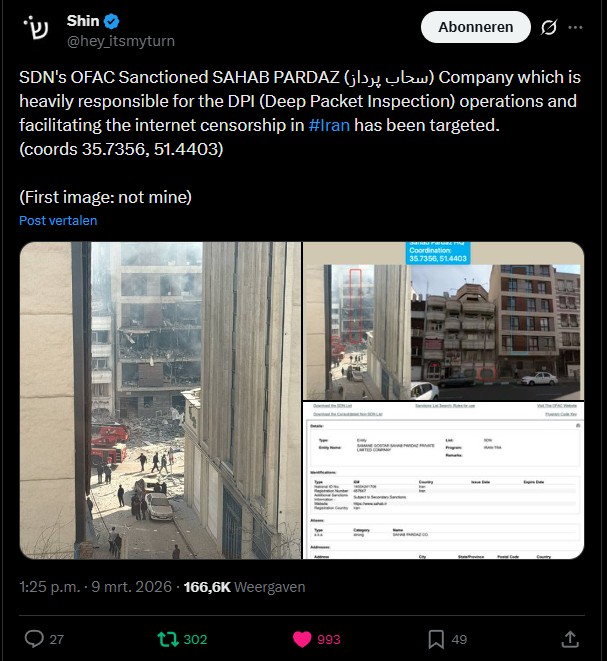
Several IT engineers were killed after an airstrike struck the Tehran offices of Sahab Pardaz, a technology company involved in building and operating parts of Iran’s internet filtering and digital censorship infrastructure.
2025–2026 Crackdown: When the Kill Switch Met Reality
None of the infrastructure documented above is theoretical. In January 2026, Iran executed its most severe internet shutdown in history.
Anatomy of a Total Blackout
The shutdown followed a precise escalation documented by Filterwatch and corroborated by Cloudflare Radar and Kentik telemetry:
- 15:19 Iran Time (11:49 UTC): IPv6 traffic collapsed — recorded by Cloudflare and Kentik simultaneously.
- 18:00 Iran Time: ArvanCloud Radar showed severe datacenter disruptions at MCI, Afranet, and HostIran.
- 20:00 Iran Time: The “Digital Curfew.” International access cut as protests escalated nationwide. IODA Active Probing dropped sharply.
- 22:15 Iran Time (18:45 UTC): Total blackout. Traffic dropped to “effectively zero” per Cloudflare Radar.
Iran International confirmed traffic hit zero at 10:15 PM local time. The Guardian reported 90% of traffic evaporated — a “new high-water mark” in shutdown sophistication.
The blackout was a layered dismantling: mobile networks collapsed first, then fixed-line became “ghost connectivity” (routers connected, no data passing), then the NIN itself was disrupted. Filterwatch documented users describing interference as “living inside a microwave.”
The Human Cost Behind the Blackout
By January 13, Iran had been without internet for over 120 hours. An estimated 87 million citizens were severed from the global internet.
The Guardian reported protests erupted in all 31 provinces, with at least 45 killed including 8 children in the first days alone. Food prices surged 70%, medicine 50%.
Iran International, cross-referencing sources within the Supreme National Security Council and IRGC, reported at least 12,000 killed — mostly on January 8–9 during the blackout, on Khamenei’s direct order with SNSC live-fire authorization.
A Tehran insider’s letter captured the reality: “There is no internet, Starlink is patchy, the killing is unprecedented… everyone knew there was a kill switch.” Only state “alerts” arrived on phones. Hundreds of newspapers fell silent.
The Whitelist Strategy: Degraded State by Design
The Guardian called the shutdown “strikingly sophisticated and chillingly precise.”
Doug Madory of Kentik warned: “This might be for the long haul.” The regime operated a whitelist — approved government and banking services stayed accessible while the global internet was blocked.
Khamenei himself posted 12 times on X on a single Friday during the blackout while 87 million citizens could not send a text message. This two-tier “degraded state” model enables indefinite shutdowns without collapsing regime command infrastructure.
As Northeastern’s David Choffnes explained: “These are splinter nets. Countries creating their own internet and tightly controlling how they interact with the rest of the world.”
Starlink Jamming: Electronic Warfare on Iranian Soil
With terrestrial internet destroyed, an estimated 30,000 to over 50,000 smuggled Starlink terminals became the last lifeline.
Cybersecurity expert Amir Rashidi reported 30–80% packet loss on Starlink: “This is not normal jamming. It very much reminds me what happened in Ukraine. This is electronic warfare.”
Satellite analyst Carlos Placido noted 15–60 Starlink satellites overhead at any time in Iran: “It’s hard to fully jam a system with so many connectivity paths.” NasNet reported working with SpaceX to reduce interference from 35% to 10%.
Security forces conducted door-to-door operations confiscating satellite dishes and seizing private CCTV recordings to identify protesters.
Information Warfare: Altered Footage
Iran International documented state media broadcasting “helicopter footage” of pro-government rallies identified as green-screen fabrications — unnatural edges, mismatched lighting, wind on hair but not clothing.
The regime has form: during 2025, IRIB TV1 reused 2022 Russian missile footage as Iranian strikes, and state accounts used Arma 3 videogame graphics to claim F-35 kills. Foreign influencers posted staged “calm Tehran” content amid the crackdown.
Filternet Plus: The $1 Billion Isolation Engine
CircleID reported a Huawei-based platform managed through ArvanCloud via a front company, costing $700M–$1 billion.
The data center beneath Fanap’s headquarters in Pardis IT Town houses 400 server racks. Equipment was smuggled from China in 24 containers. President Pezeshkian and China’s ambassador both visited the site in early 2025.
The “white SIM card” scandal confirmed the two-tier design: specially provisioned SIMs for regime loyalists, security officials, and IRGC businesses maintained full internet during shutdowns. Blackouts are not failures — they are features with ruling-class exceptions.
Circumvention at Scale
Over 11 million users connected through Psiphon alone. Filterwatch documented that most mainstream VPNs ceased functioning: upload speeds near-zero, tunnels “pulsing,” and Telegram proxies showed green status but transmitted no data.
SpaceX granted free Starlink access to Iran. But as Choffnes warned: “You may be risking your life by using one of these receivers” — possession of a Starlink terminal is illegal in Iran, and security forces actively hunted for dishes.
Digital Oppression Has a Paper Trail
Despite its branding, ArvanCloud is not merely a CDN provider that happens to operate in Iran. Forensic evidence presented in this analysis demonstrates that Noyan Abr Arvan — operating through a deliberately complex web of autonomous systems, shell entities, and European hosting arrangements — functions as a critical technological enabler of Iran’s digital oppression infrastructure.
The (OSINT) investigation reveals:
- European data centers actively host infrastructure used for censorship and surveillance.
- Western transit providers carry traffic that enables sanctions evasion.
- Russian networks provide both digital routing and physical jamming capabilities.
- State-controlled malware operates freely through ArvanCloud even during total shutdowns.
- Iran’s NIN is not a defensive measure — it is a weapon deployed against civilians.

Recommendations
Sanctions authorities (OFAC, OFSI, EU): Expand designations to include upstream transit providers knowingly carrying ArvanCloud traffic. Investigate European hosting providers for sanctions violations.
RIPE NCC and regional registries: Review AS205585 and associated ASNs for policy violations regarding sanctioned entities operating European network resources.
Threat intelligence community: Monitor ArvanCloud infrastructure for ongoing malware hosting and C2 activity. Emotet findings suggest systematic state-sponsored abuse.
Civil society and digital rights organizations: Use this forensic methodology to map similar infrastructure in other authoritarian regimes building sovereign internet architectures.
Iran’s digital cage has an address, a BGP path, and a paper trail. Will the international community act on the evidence?
Great source
This document was used as a great source. Thank you to the person(s) that made it. Sadly it is difficult for us to find the author(s).
https://drive.google.com/file/d/1OR26vKfIaoshC3TBJS5tQoOD5WjFGzn1/view
Additional sources
Iran International:
- https://www.iranintl.com/en/202601089575 — Traffic drops to zero, Cloudflare Radar (Jan 8)
- https://www.iranintl.com/en/202601133935 — 120+ hours without internet (Jan 13)
- https://www.iranintl.com/en/202601130145 — At least 12,000 killed, SNSC sourcing
- https://www.iranintl.com/en/202601137586 — Altered rally footage, green-screen fabrications
- https://www.iranintl.com/en/202601126803 — Satellite dish confiscation raids
The Guardian:
- https://www.theguardian.com/world/2026/jan/08/iran-plunged-into-internet-blackout-after-protest-crackdown-leaves-at-least-45-dead — 45+ killed, 31 provinces
- https://www.theguardian.com/world/2026/jan/10/irans-internet-shutdown-is-strikingly-sophisticated-and-chillingly-precise — “Chillingly precise,” Madory/Rashidi quotes
Filterwatch:
- https://filter.watch/english/2026/01/09/network-monitoring-january-2026-internet-repression-in-times-of-protest/ — Minute-by-minute shutdown timeline
- https://filter.watch/english/2024/12/17/investigative-report-december-iranian-messaging-apps/ — OTF Security Lab: Rubika/Eitaa/Bale
Academic / Research:
- https://arxiv.org/html/2507.14183v1 — “Iran’s Stealth Internet Blackout”
Northeastern University:
- https://news.northeastern.edu/2026/01/14/iran-internet-shutdown/
CircleID:
- https://circleid.com/posts/iran-nears-completion-of-internet-kill-switch-amid-protests-says-iran-international — Huawei platform, $700M-$1B, Fanap datacenter
PCMag:
- https://au.pcmag.com/networking/115300/iran-appears-to-be-jamming-starlink-amid-protests-internet-blackout — Starlink jamming, Rashidi/Placido analysis
US Treasury / OFAC:
- https://home.treasury.gov/news/press-releases/jy0948 — Afkar System Yazd sanctions (Sept 2022)
- https://home.treasury.gov/news/press-releases/jy0494 — Emennet Pasargad sanctions (Nov 2021)
- https://home.treasury.gov/news/press-releases/jy2629 — Emennet expanded sanctions (Sept 2024)
OFAC Sanctions Search:
- https://sanctionssearch.ofac.treas.gov/ — Sanctions database reference
OpenSanctions:
- https://www.opensanctions.org/entities/NK-a7rFVTm2V3NhDQfwNKhmrP/ — Australian DFAT designation
UK Government:
- https://www.gov.uk/government/publications/the-uk-sanctions-list — UK OFSI sanctions list
Rewards for Justice:
- https://rfj.tips/Iran-246 — $10M bounties on IRGC cyber operatives
BleepingComputer:
- https://www.bleepingcomputer.com/news/security/iranian-hackers-work-with-ransomware-gangs-to-extort-breached-orgs/ — FBI/CISA/DC3 joint advisory (Pioneer Kitten / Danesh Novin Sahand)
Threat Intelligence Databases:
- https://urlhaus.abuse.ch/host/sarvkaran.com/ — Emotet malware evidence
- https://www.virustotal.com/gui/url/e31376a9621d15ae2bc2cee42594c92a75d6fb63481d26fb19c729b3466ed8f3/detection — Malware detection confirmation
Network Intelligence:
- https://radar.cloudflare.com/routing/as205585 — Cloudflare Radar (AS205585 traffic data)
- https://bgp.tools/as/205585 — BGP analysis AS205585
- https://bgp.tools/as/200315 — BGP analysis AS200315
Standards / Regulatory:
- https://datatracker.ietf.org/doc/html/rfc1918 — RFC 1918 (private IP address definition)
- https://www.bafa.de/EN/Service/Contact/contact_node.html — German BAFA (export control authority)
Cyberwarzone Internal:
- https://cyberwarzone.com/2026/01/17/iran-revolution-2026-nationwide-internet-blackout-continues/