A supply chain attack against Aqua Security’s open-source Trivy vulnerability scanner has led to the distribution of malicious artifacts via Docker Hub, spreading an information-stealer malware known as TeamPCP, along with a worm and a Kubernetes wiper. The incident highlights a widening attack radius across developer environments.
On March 22, new malicious versions of Trivy, specifically 0.69.4, 0.69.5, and 0.69.6, were pushed to Docker Hub without corresponding GitHub releases or tags. These compromised versions have since been removed from the container image library. The last known clean release of Trivy on Docker Hub was 0.69.3.
TeamPCP Infostealer and GitHub Organization Compromise
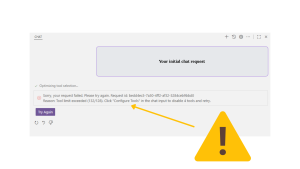
Socket security researcher Philipp Burckhardt confirmed the presence of the TeamPCP infostealer within the malicious images. Burckhardt stated in a blog post,
“New image tags 0.69.5 and 0.69.6 were pushed on March 22 without corresponding GitHub releases or tags. Both images contain indicators of compromise associated with the same TeamPCP infostealer observed in earlier stages of this campaign.”
The attackers leveraged the supply chain compromise of Trivy to distribute not only the infostealer but also a worm and a Kubernetes wiper. This escalation means that developer environments pulling these compromised images from Docker Hub could face severe consequences, including data theft and significant infrastructure disruption.
This incident follows a trend of cloud-native attacks targeting development tools and platforms.
Further investigation revealed that an attacker force-pushed 75 out of 76 version tags in the aquasecurity/trivy-action repository, which is the official GitHub Action for running Trivy vulnerability scans in CI/CD pipelines.
Security researcher Paul McCarty also noted that the Aqua Security GitHub organization was briefly modified, with archived snapshots showing unauthorized repositories prefixed with tpcp-docs-* and descriptions stating “TeamPCP Owns Aqua Security.” These actions indicate a deeper level of compromise within the GitHub organization.
The initial compromise was traced to a compromised Argon-DevOps-Mgt service account, which served as a crucial link between the affected GitHub organizations (aquasec-com and aquasecurity).
This compromise also led to the defacement of 44 repositories within the aquasec-com GitHub organization.
Remediation and Subsequent Attacks
Following the discovery, Aqua Security took steps to revoke compromised credentials and clean up the affected GitHub repositories and Docker Hub images. The malicious versions of Trivy (0.69.4, 0.69.5, and 0.69.6) were promptly removed from Docker Hub.
Further investigations revealed that the threat actors behind the Trivy supply chain attack also launched follow-on attacks, compromising 47 npm packages with a novel self-propagating worm named CanisterWorm.
This malware uniquely leverages an ICP canister, a tamperproof smart contract on the Internet Computer blockchain, as a dead drop resolver for its command-and-control (C2) server. This marks the first publicly documented abuse of an ICP canister for such a purpose, as noted by Aikido Security researcher Charlie Eriksen.
Kubernetes Wiper Targets Iranian Systems
The Python-based payload distributed through the compromised Trivy images also included functionalities to wipe Iranian Kubernetes clusters. This was achieved using a container named kamikaze.
For non-Kubernetes Iranian hosts, the attackers utilized the destructive command rm -rf / --no-preserve-root to erase data. These actions demonstrate the attackers’ intent for widespread data destruction targeting specific regions.