The FBI and Justice Department have seized four domains they say were used by Iran’s Ministry of Intelligence and Security to host stolen data, intimidate targets, and amplify cyber operations under the “Handala” brand. As reported by The Record, the domains were allegedly tied to campaigns involving the Albanian government, Iranian dissidents, Israeli officials, and U.S. companies, including the recent Stryker incident that prosecutors said disrupted emergency medical care in Maryland hospitals.
The significance of the seizure is not just the takedown itself. It ties a live wartime cyber front to a broader Iranian state-linked infrastructure that, according to The Record’s account of court filings, has blended data theft, leak-site operations, wiper-style disruption, and psychological pressure against both state and civilian targets. That makes the case relevant not only to the Iran war but also to the growing risk that cyber activity can spill into hospital technology, diplomatic systems, and transnational political coercion.
The seized domains connect a leak-site network to a wider Iranian state-linked campaign
According to The Record, the Justice Department seized four domains — Justicehomeland[.]org, Handala-Hack[.]to, Karmabelow80[.]org, and Handala-Redwanted[.]to — and tied them to operations allegedly run by Iran’s Ministry of Intelligence and Security. The article says court filings linked those domains to campaigns dating back to 2022 and to multiple online identities, most recently operating under the Handala name.
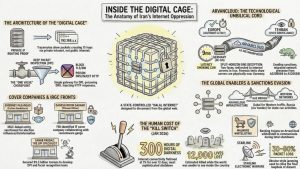
That attribution matters because it pushes the story beyond hacktivist-style branding. If the government’s allegation is accurate, the domains were not just publicity channels for stolen data. They were part of a state-linked infrastructure used to host leaks, threaten targets, and recycle data theft into coercive messaging. That is consistent with CWZ’s earlier coverage of Iran’s broader digital control and coercion infrastructure and with the larger pattern described in Cyberwarzone’s intelligence briefing on Iran’s 2026 cyber and war activity.
The Record also reported that the sites hosted stolen information tied to Albanian government victims, Iranian dissidents, Israeli officials, Israeli Defense Forces personnel, U.S. companies, and members of a Jewish community in New York. Not all of those allegations are independently verified in the article itself, but they show the breadth of the target universe the FBI is trying to map.
The Stryker intrusion pushed the story beyond data theft and into patient-care disruption
The most important detail in The Record’s report is not that Handala posted stolen material. It is that prosecutors said the Stryker incident interfered with hospital operations in Maryland. According to the article, some hospitals temporarily suspended connections to Stryker systems, a Stryker employee working inside a hospital lost device access after a wipe, and clinicians were told to fall back on radio consultation and verbal descriptions when communication systems were disrupted.
That shifts the story from cyber theater to operational risk. Stryker’s products are used inside hospitals for communication and workflow support, so even a compromise aimed at internal Microsoft systems can create downstream disruption if administrators lose trusted access or are forced to isolate connected services. That threat path aligns with CWZ’s earlier reporting on Handala’s claimed wiper attack on Stryker and CISA’s warning on Microsoft Intune after the Stryker incident.
The Record said investigators believe the attackers used Intune’s native device wipe functionality to destroy data across more than 200,000 employee devices in the United States, Ireland, India, and elsewhere. That detail matters because it shows how a state-linked operation can weaponize legitimate enterprise administration features instead of relying only on custom malware. In practice, that lowers the barrier to disruptive effects inside large organizations that already depend on centralized device management.
Why the MOIS seizure matters in the middle of a regional war
The timing of the seizure is important. The Record reported that after kinetic hostilities between the United States, Israel, and Iran intensified, Handala began publishing personal details linked to Israeli military officials and sending threatening messages. That suggests the leak sites were serving not only as repositories for stolen data but also as instruments of wartime intimidation and narrative warfare.
The Albania thread reinforces that point. According to The Record, one of the seized sites was linked to material stolen during the 2022 cyberattacks on the Albanian government, including operations that knocked services offline and exposed correspondence involving Albania and the United States. That history gives the current seizure a longer strategic arc: the same alleged ecosystem was not born in the current war but has now been repurposed inside it.
What still needs caution is attribution at the outer edge of the case. The seizure shows what the FBI believes the domains were used for, but domain takedowns do not by themselves answer every question about chain of command, contractor relationships, or how much operational autonomy a front brand like Handala actually had. Even so, the case provides one of the clearest public windows yet into how Iranian state-linked cyber operations may combine espionage, coercive leaks, disruptive device management abuse, and political signaling in a single campaign.